Similar presentations:
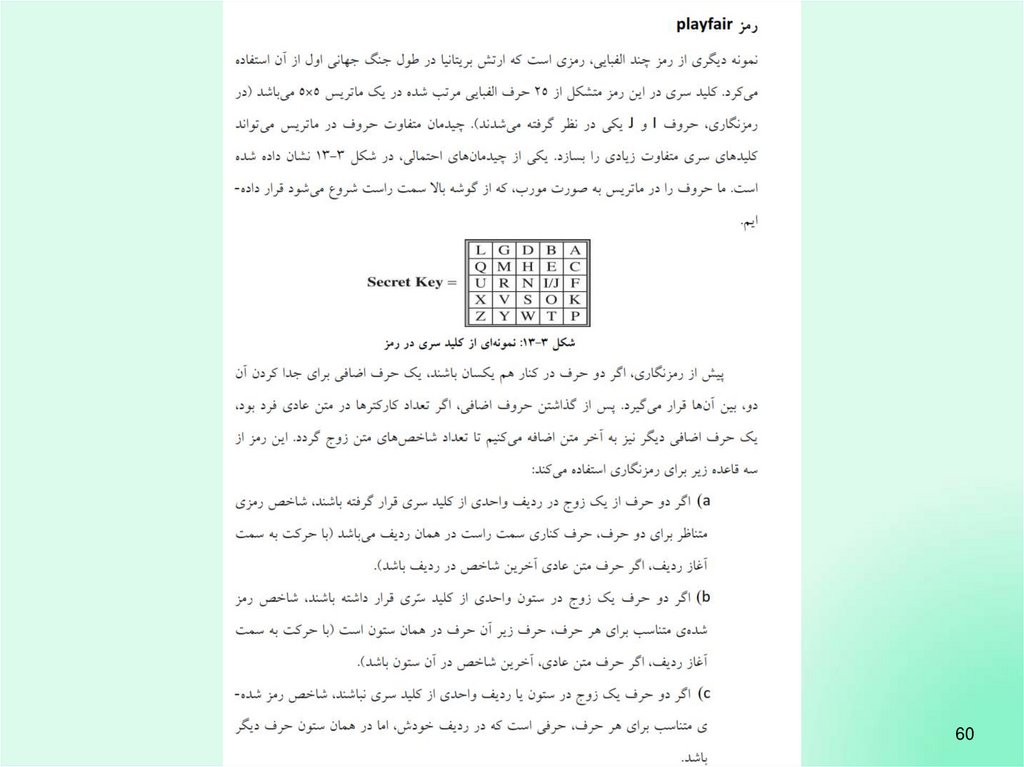
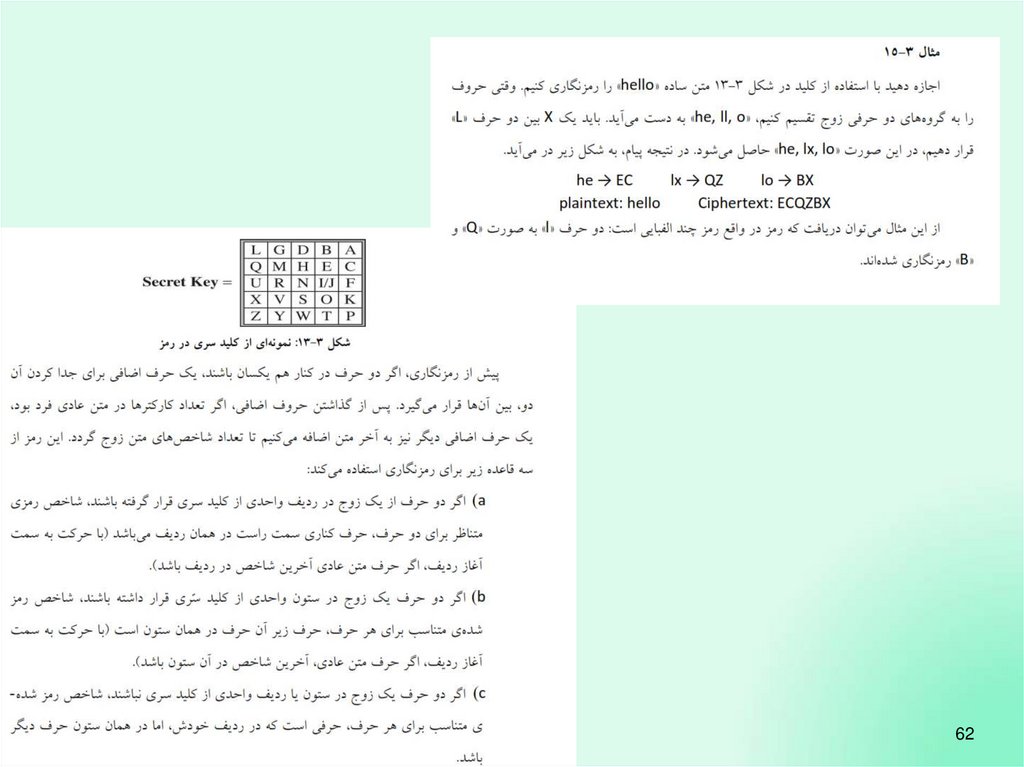
What is network security?
1. What is network security?
Principles of cryptography2. Principles of cryptography
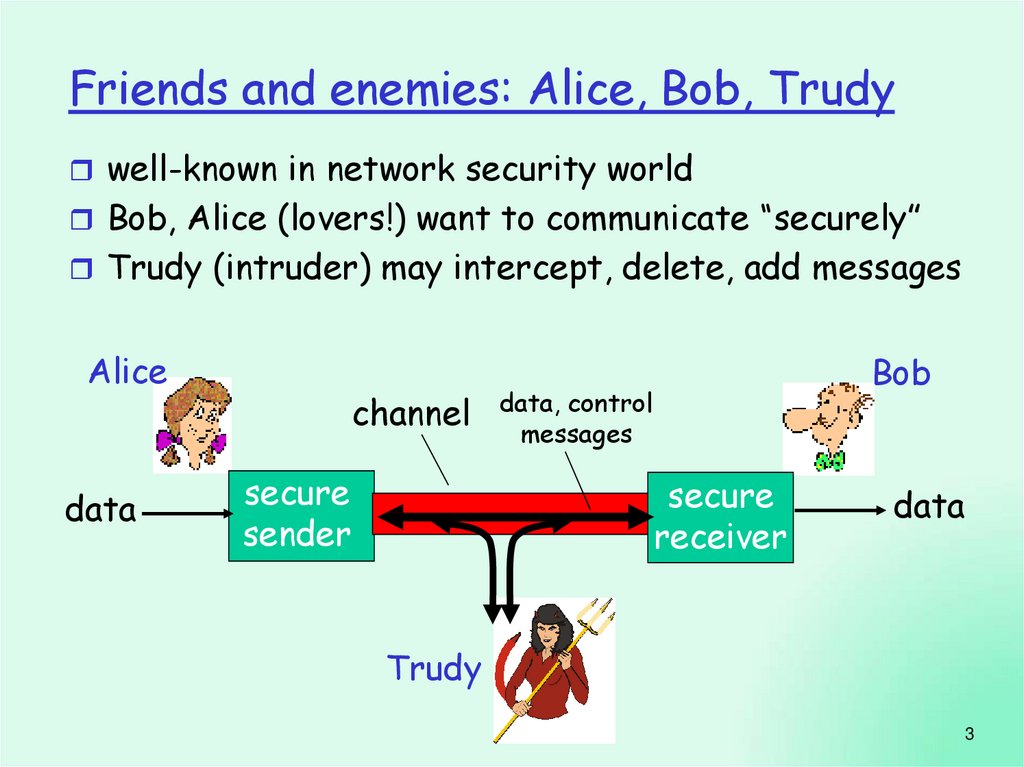
Friends and enemies: Alice, Bob, Trudywell-known in network security world
Bob, Alice (lovers!) want to communicate “securely”
Trudy (intruder) may intercept, delete, add messages
Alice
data
channel
secure
sender
Bob
data, control
messages
secure
receiver
data
Trudy
3
3. Friends and enemies: Alice, Bob, Trudy
Who might Bob, Alice be?… well, real-life Bobs and Alices!
Web browser/server for electronic
transactions (e.g., on-line purchases)
on-line banking client/server
DNS servers
routers exchanging routing table updates
other examples?
8: Network Security
8-4
4. Who might Bob, Alice be?
Cryptography8: Network Security
8-6
5. There are bad guys (and girls) out there!
8: Network Security8-7
6. Cryptography
8: Network Security8-8
7.
108.
119.
8: Network Security8-12
10.
8: Network Security8-13
11.
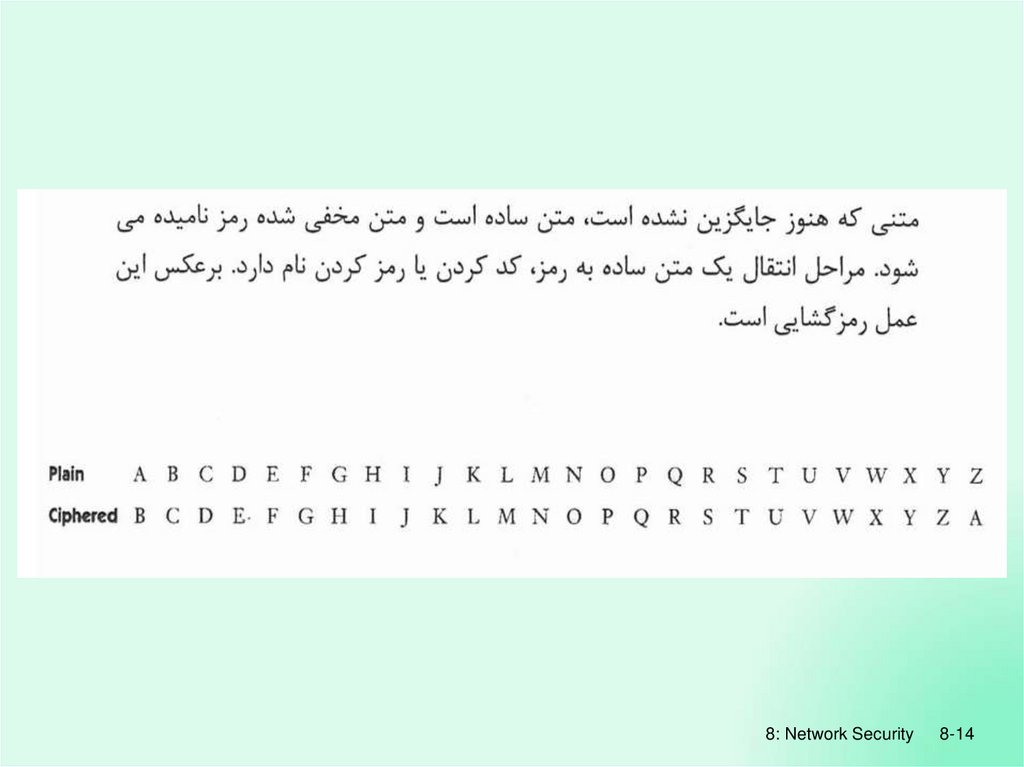
8: Network Security8-14
12.
8: Network Security8-15
13.
8: Network Security8-16
14.
8: Network Security8-19
15.
8: Network Security8-20
16.
8: Network Security8-21
17.
8: Network Security8-22
18.
8: Network Security8-23
19.
8: Network Security8-24
20.
8: Network Security8-25
21.
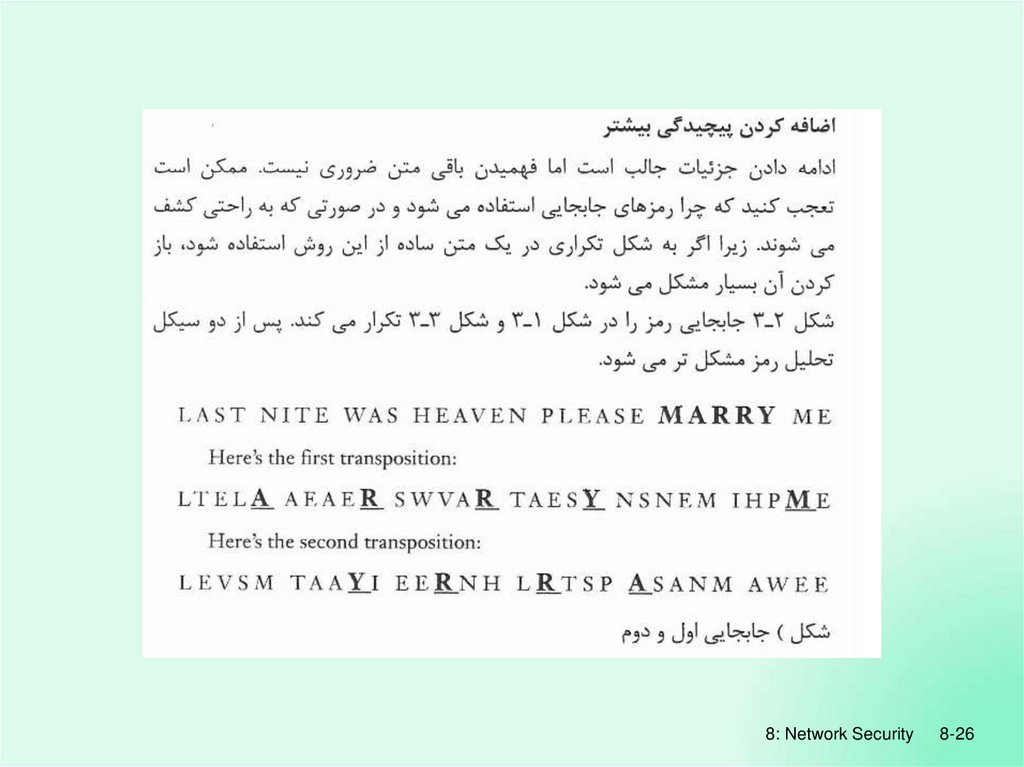
8: Network Security8-26
22.
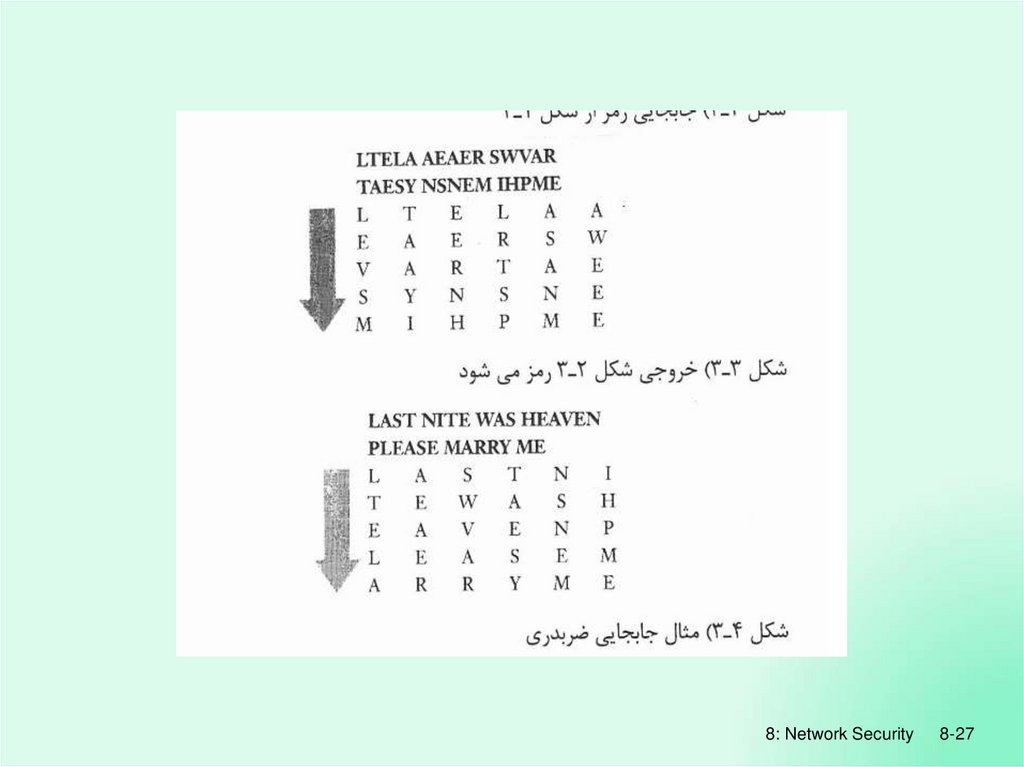
8: Network Security8-27
23.
8: Network Security8-28
24.
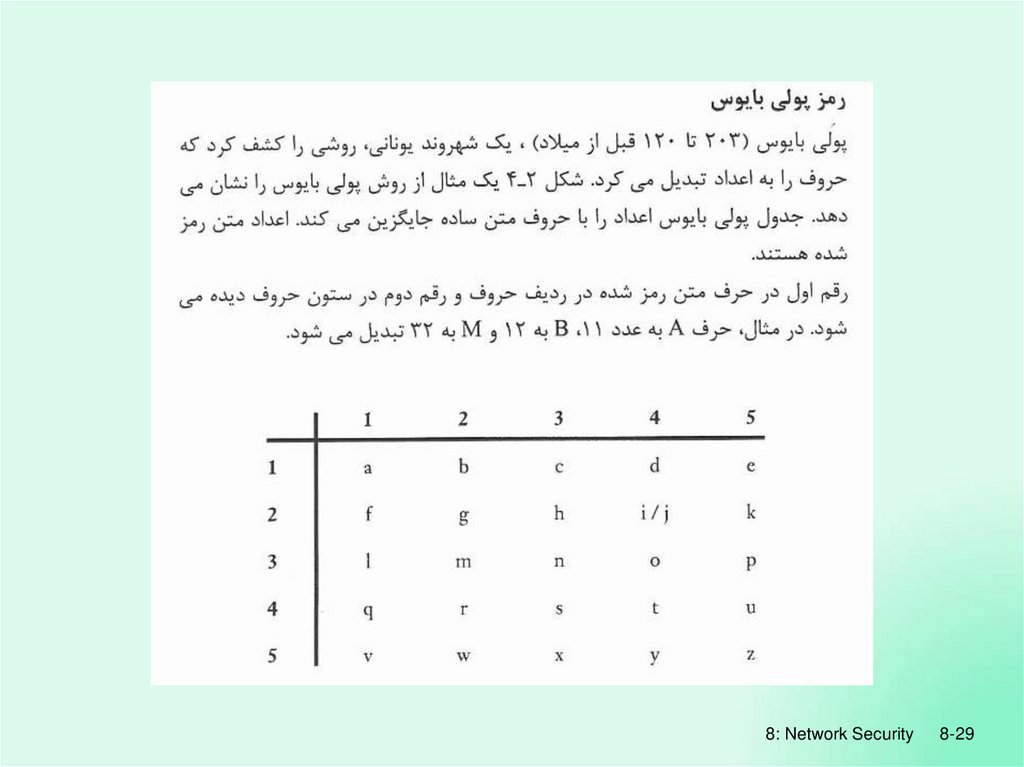
8: Network Security8-29
25.
8: Network Security8-30
26.
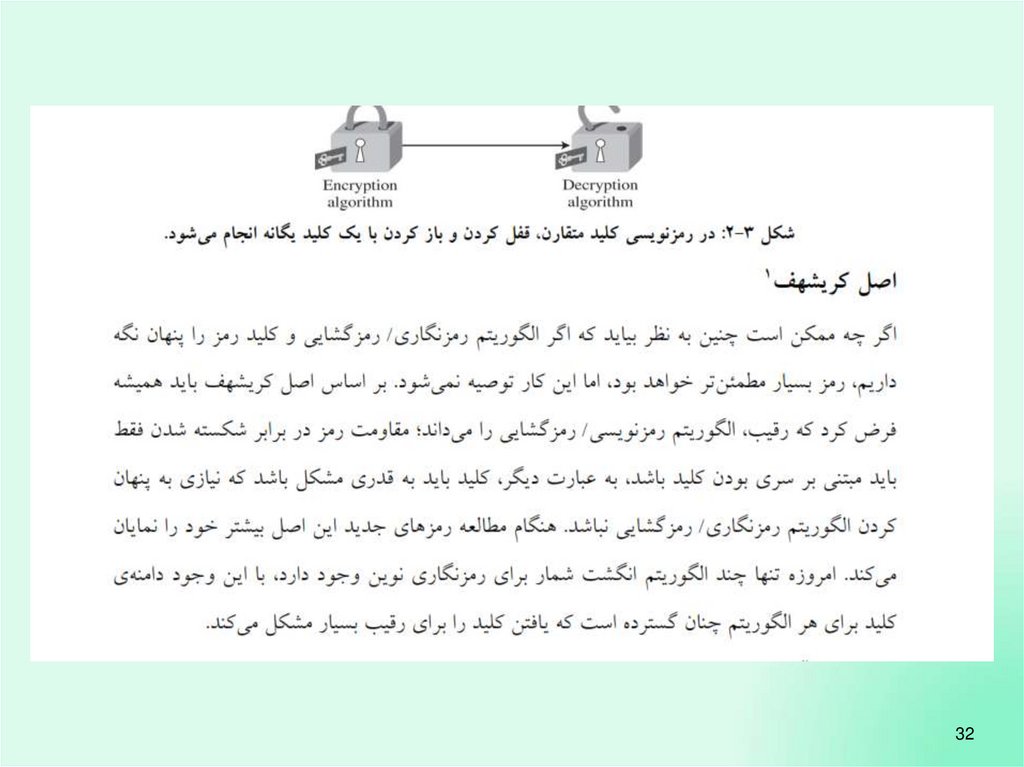
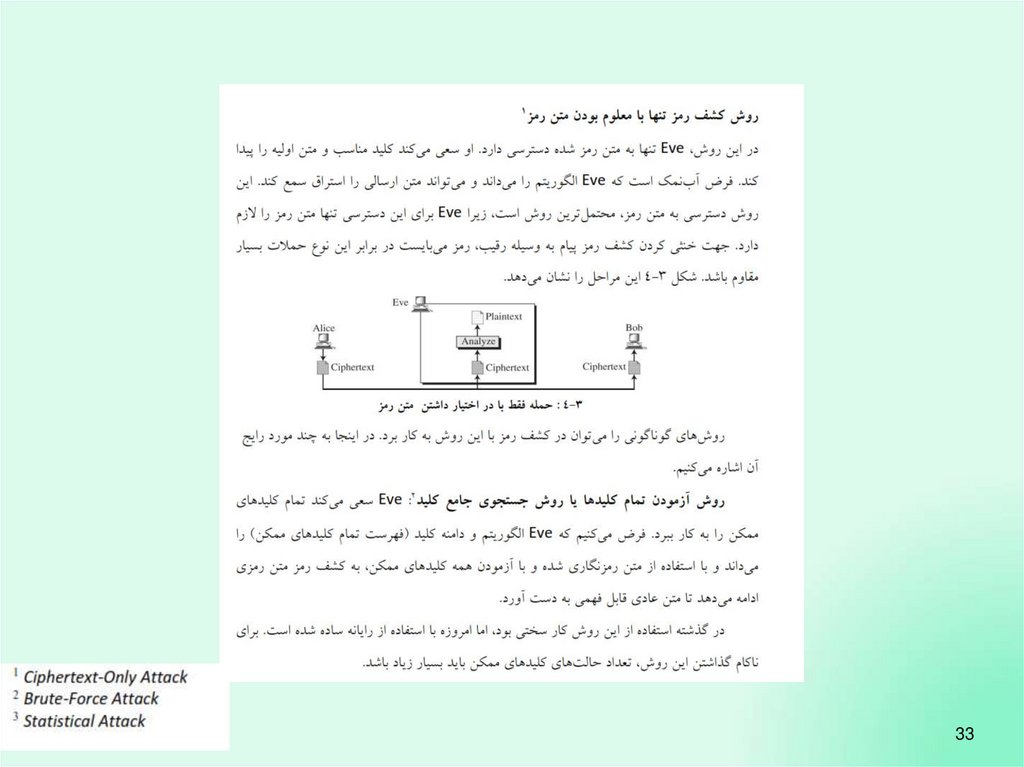
3227.
3328.
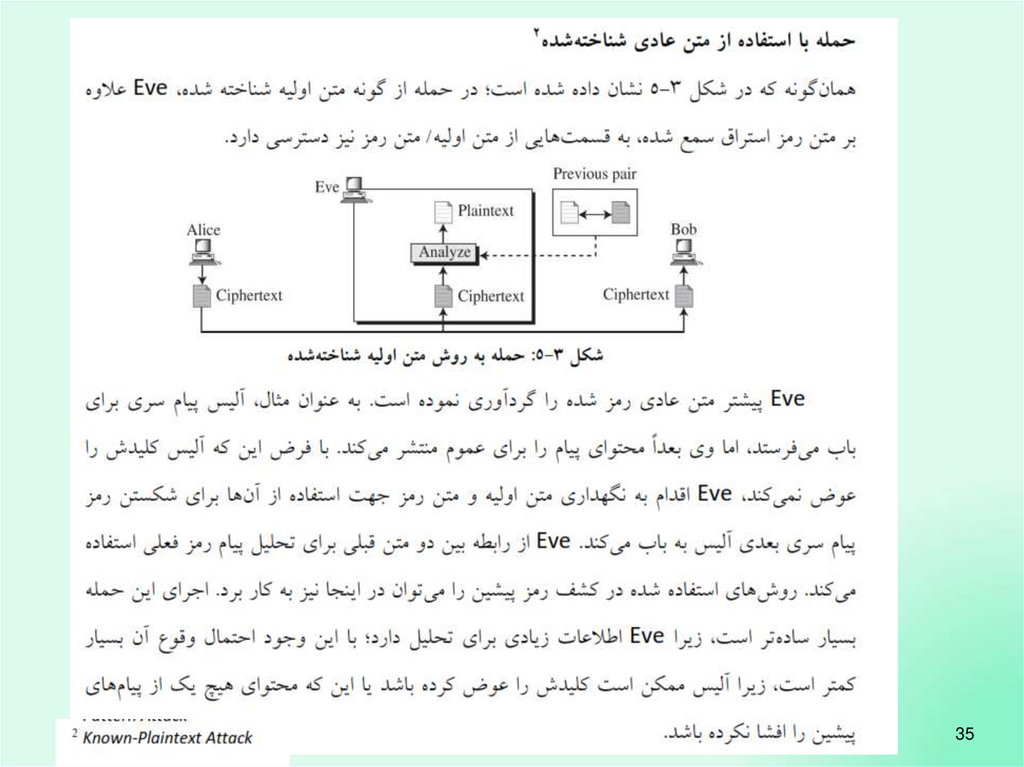
3429.
3530.
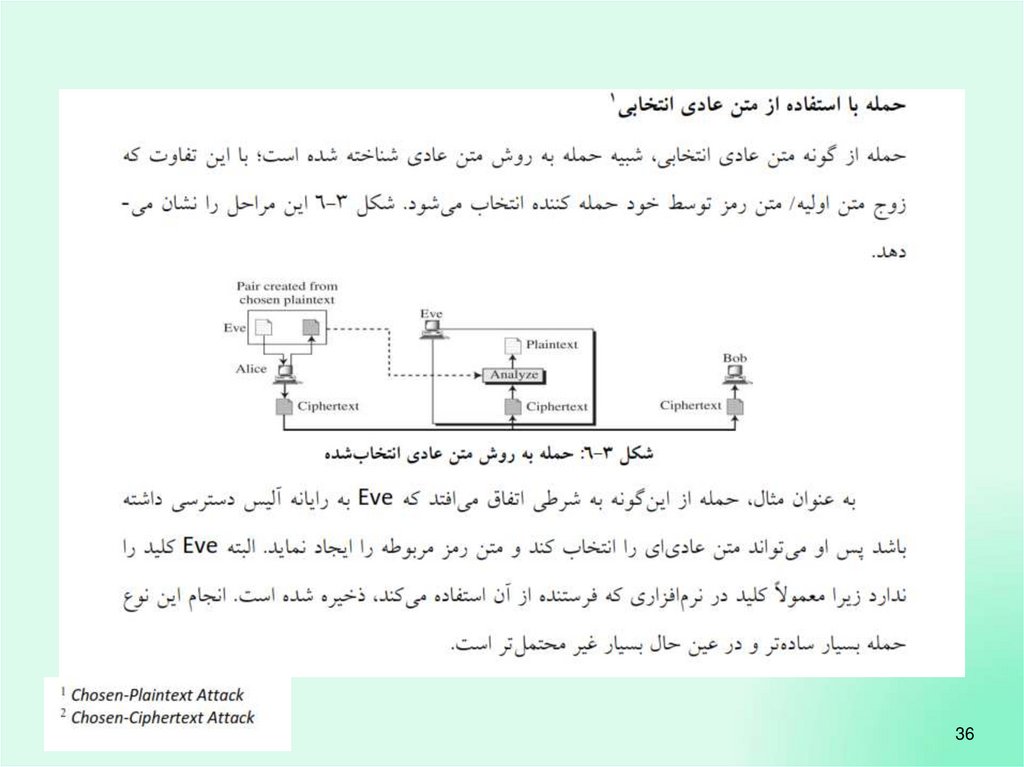
3631.
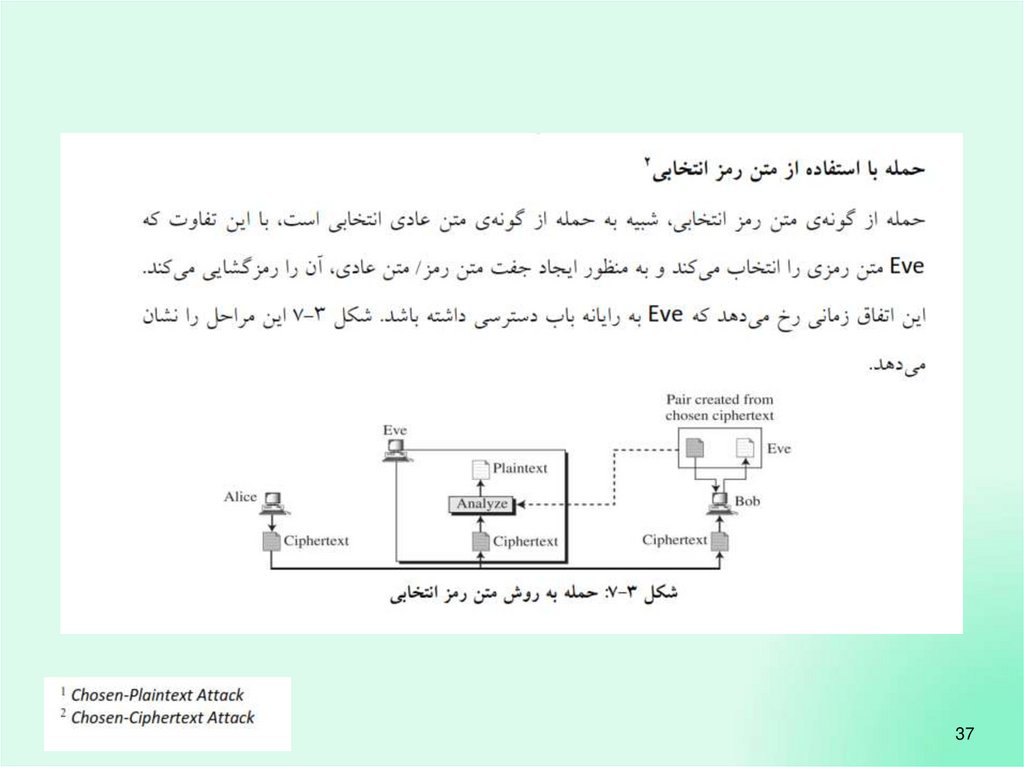
3732.
3833.
3934.
4035.
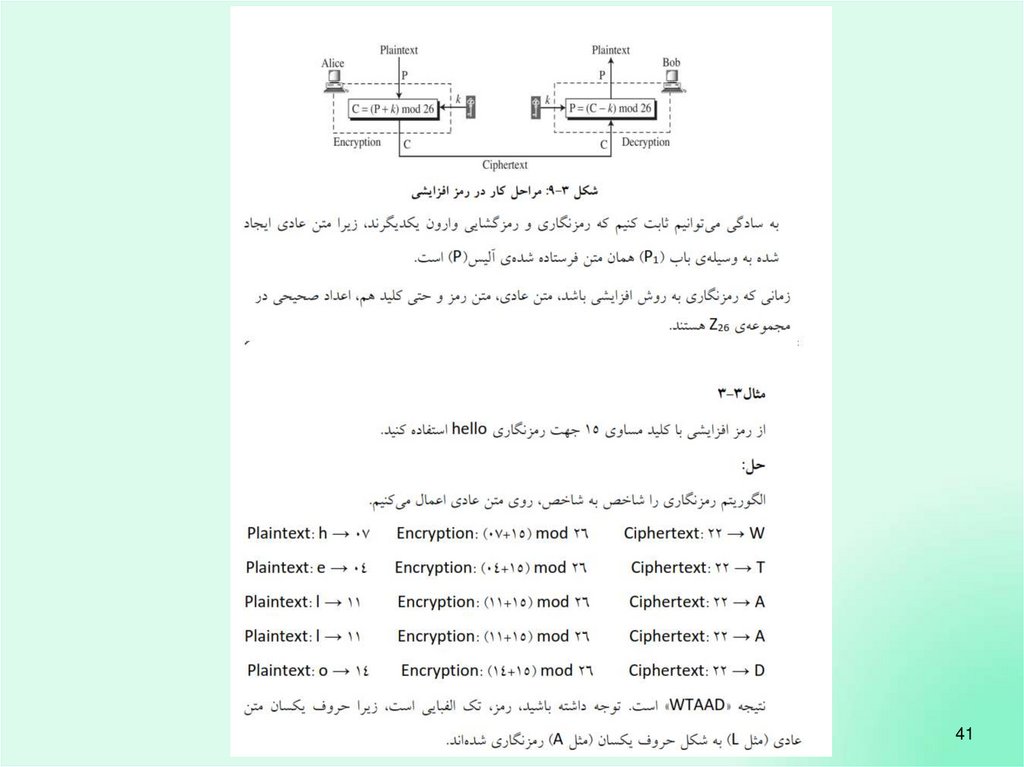
4136.
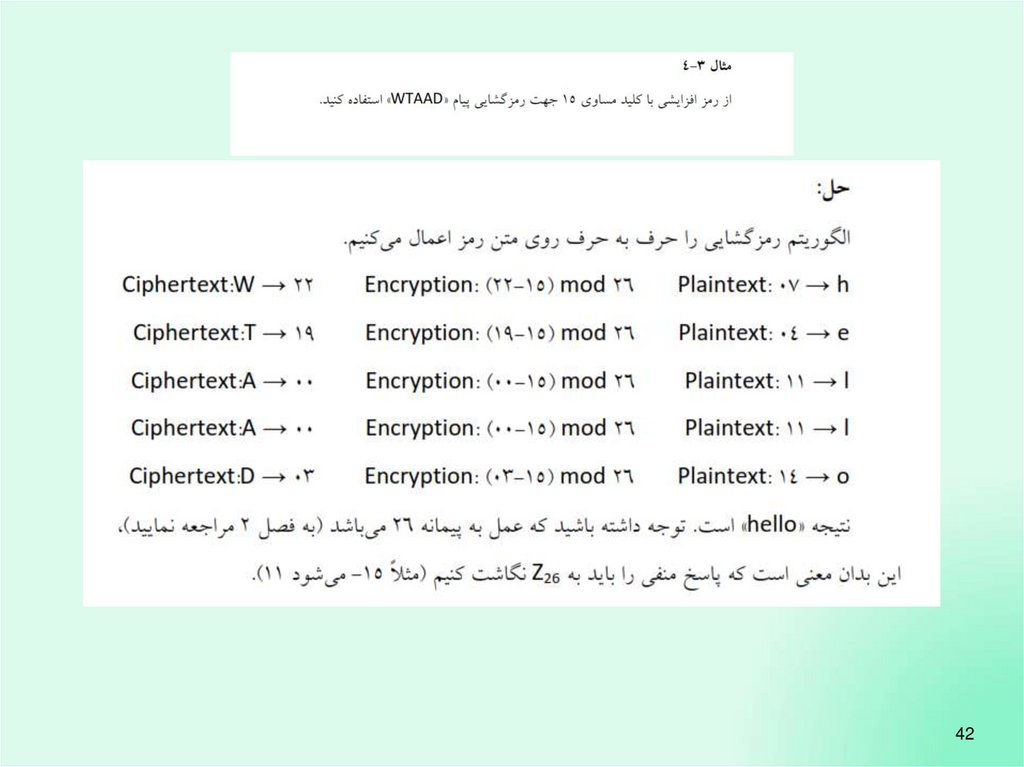
4237.
4338.
4439.
4540.
4641.
4742.
gcd(k,26)=148
43.
4944.
5045.
5146.
5247.
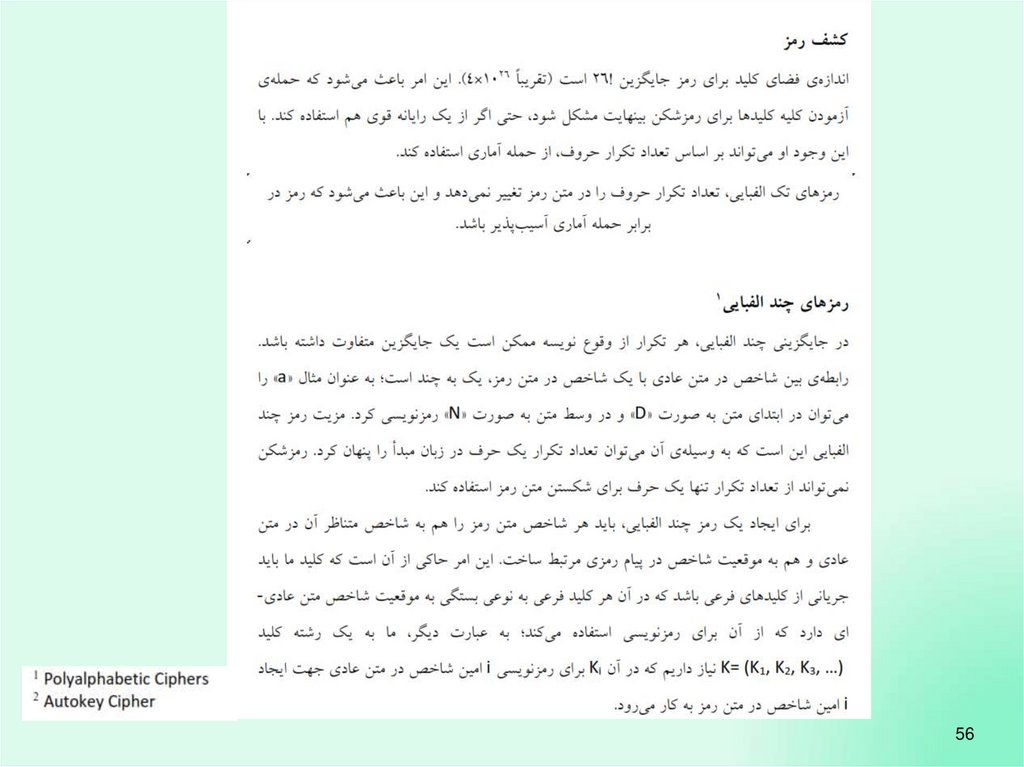
5548.
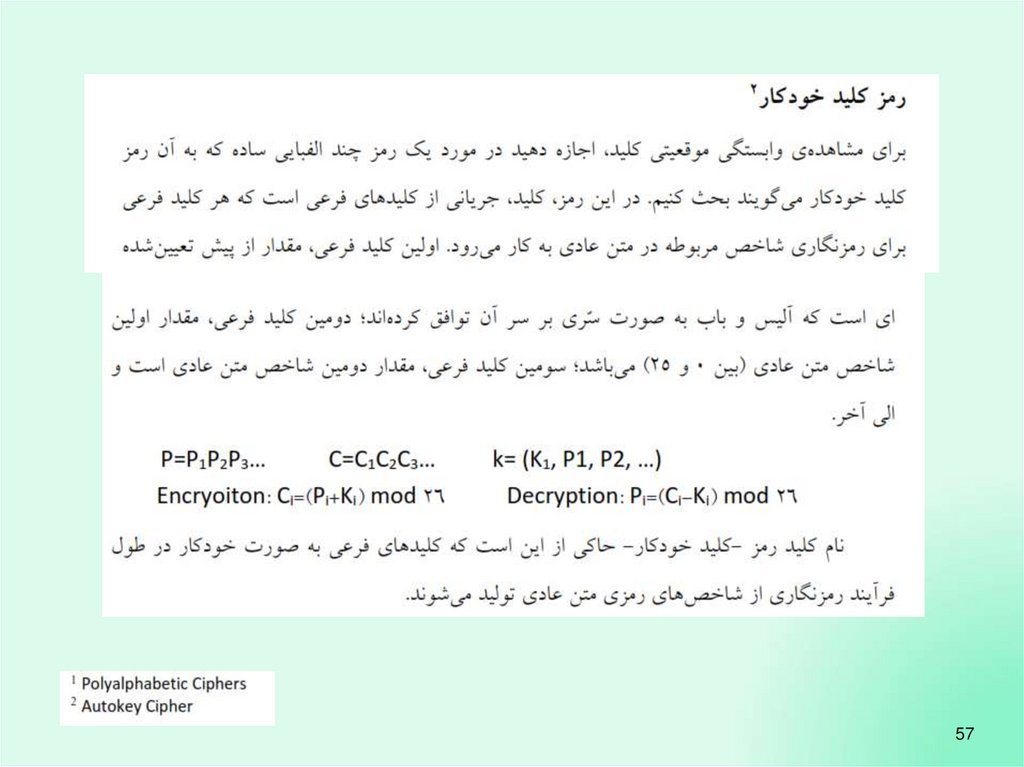
5649.
5750.
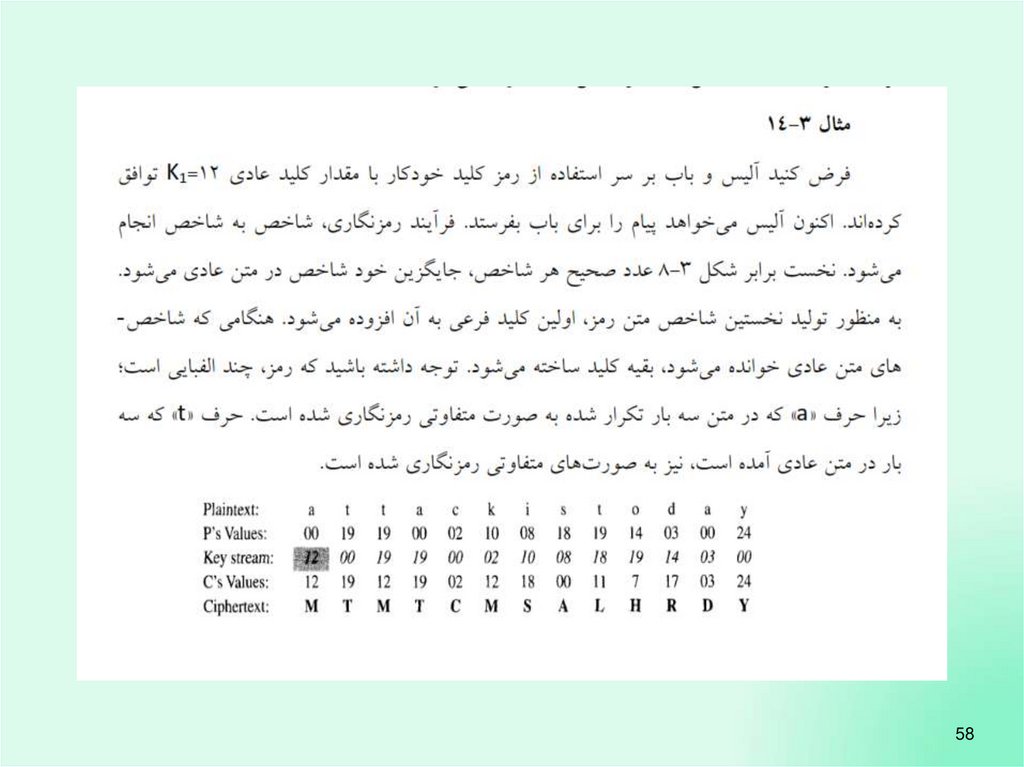
5851.
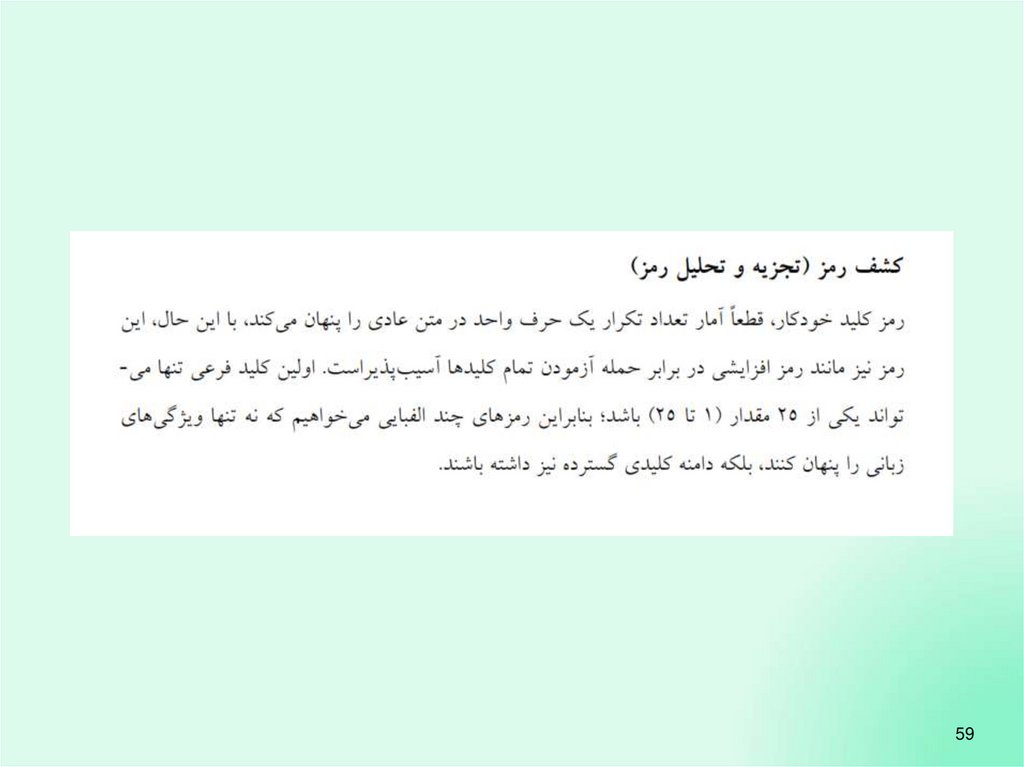
5952.
6053.
6154.
6255.
6356.
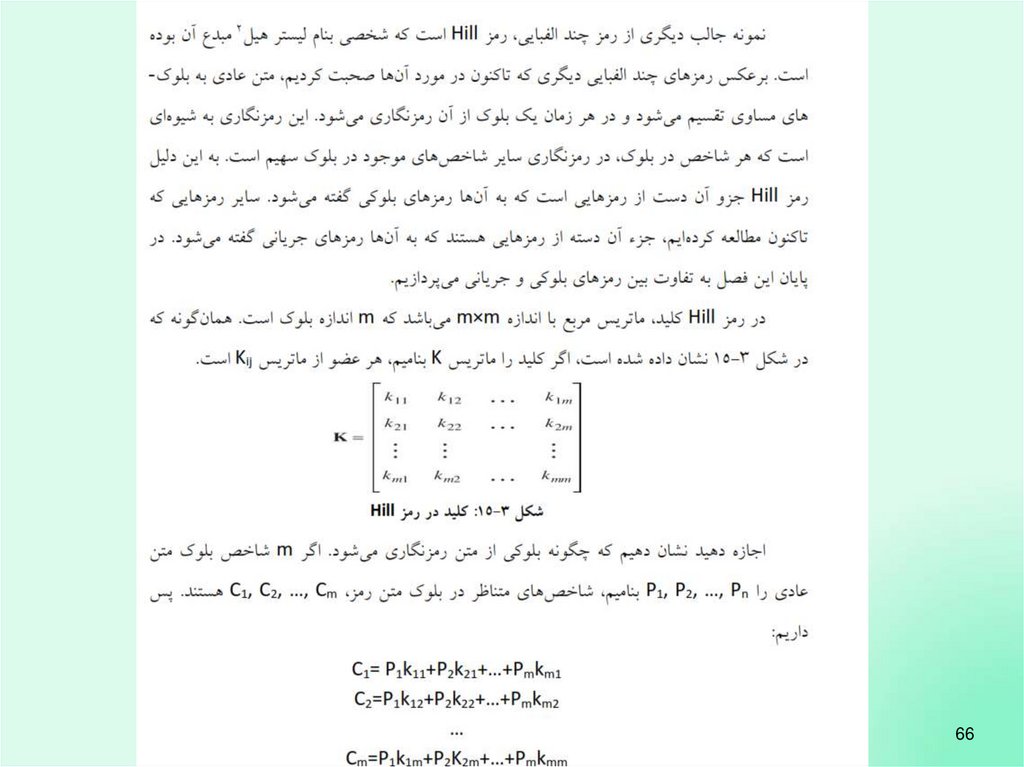
6657.
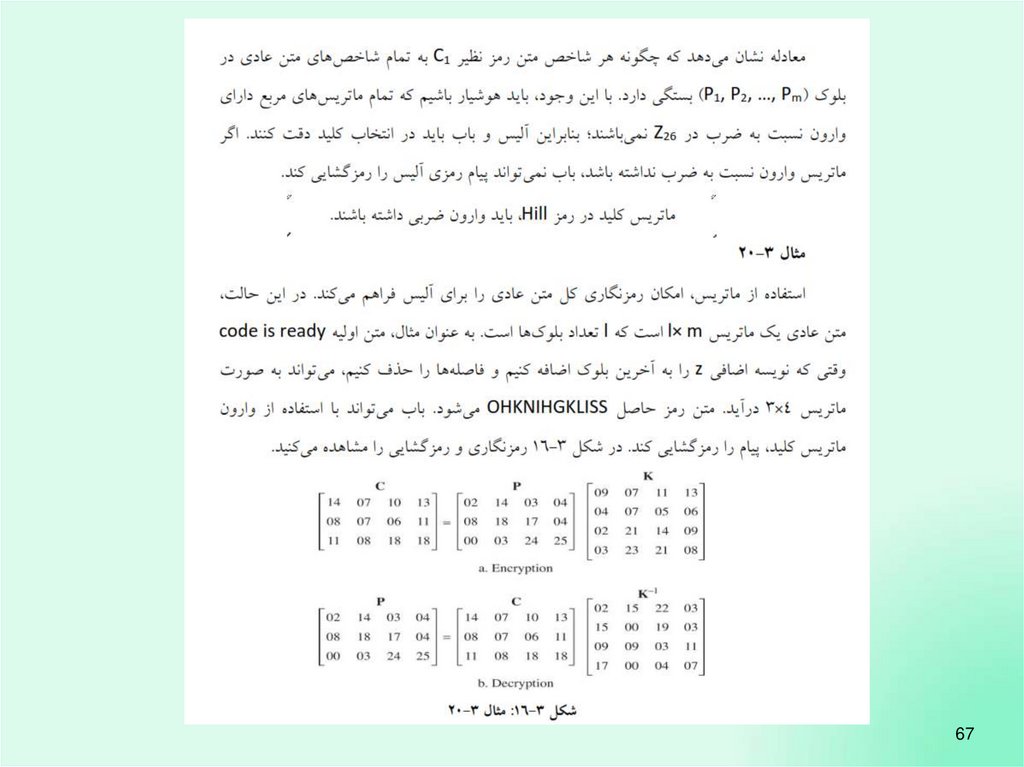
6758.
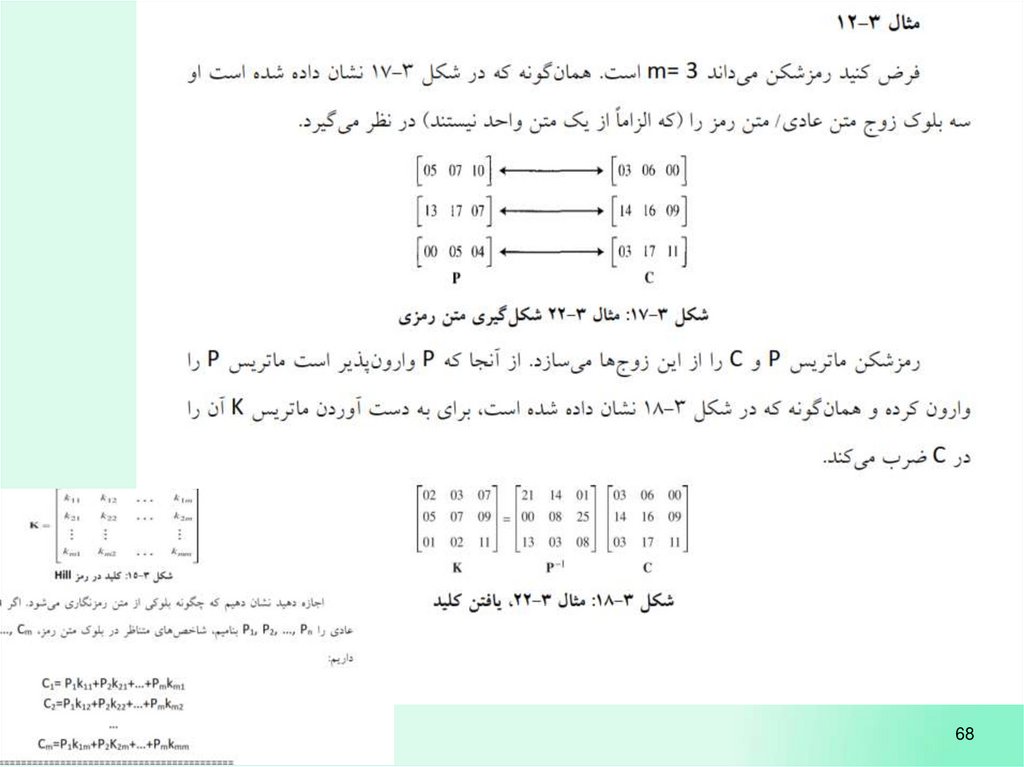
6859.
6960.
7061.
7162.
7263.
7364.
7465.
7566.
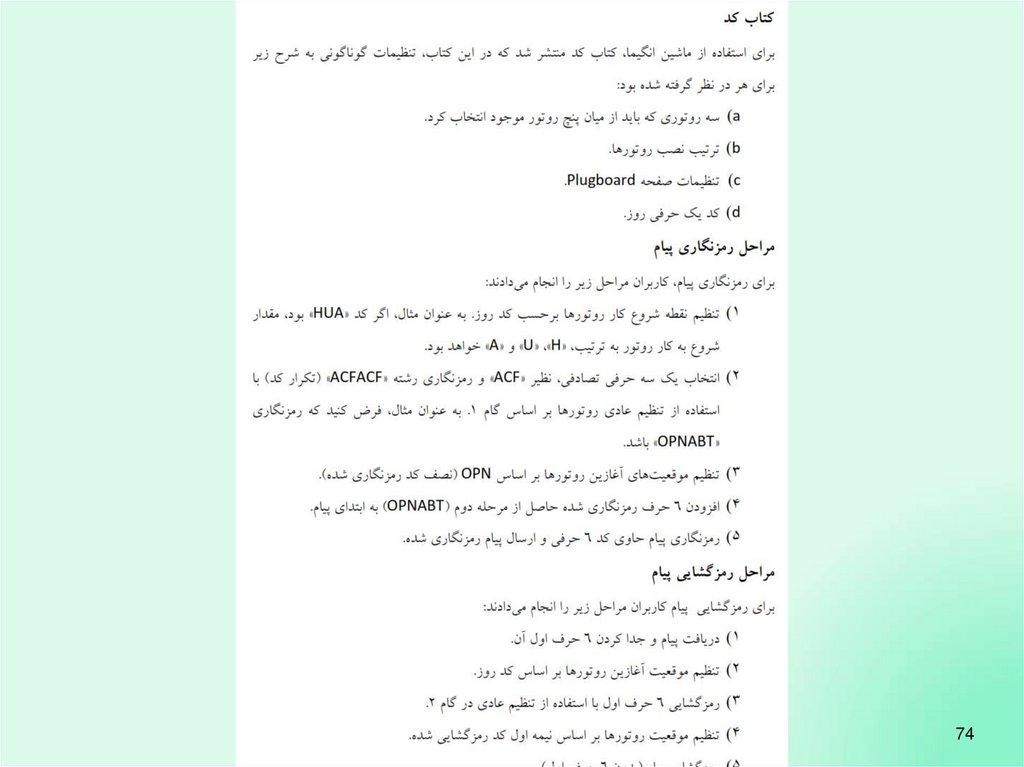
7667.
7768.
7869.
7970.
8071.
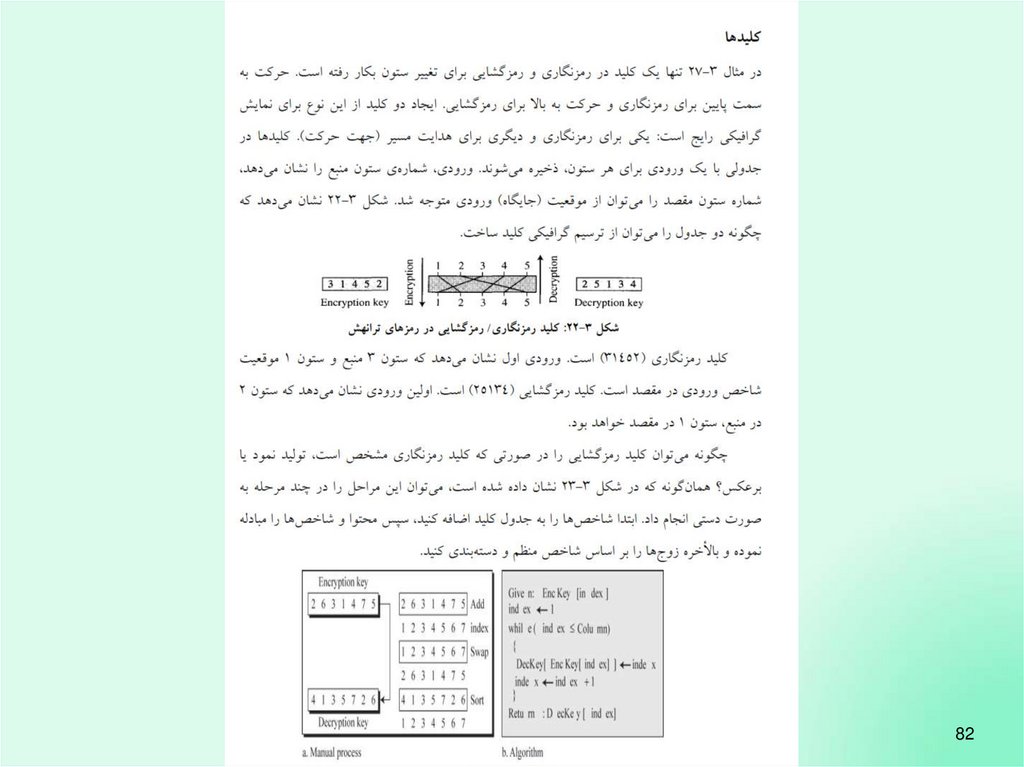
8172.
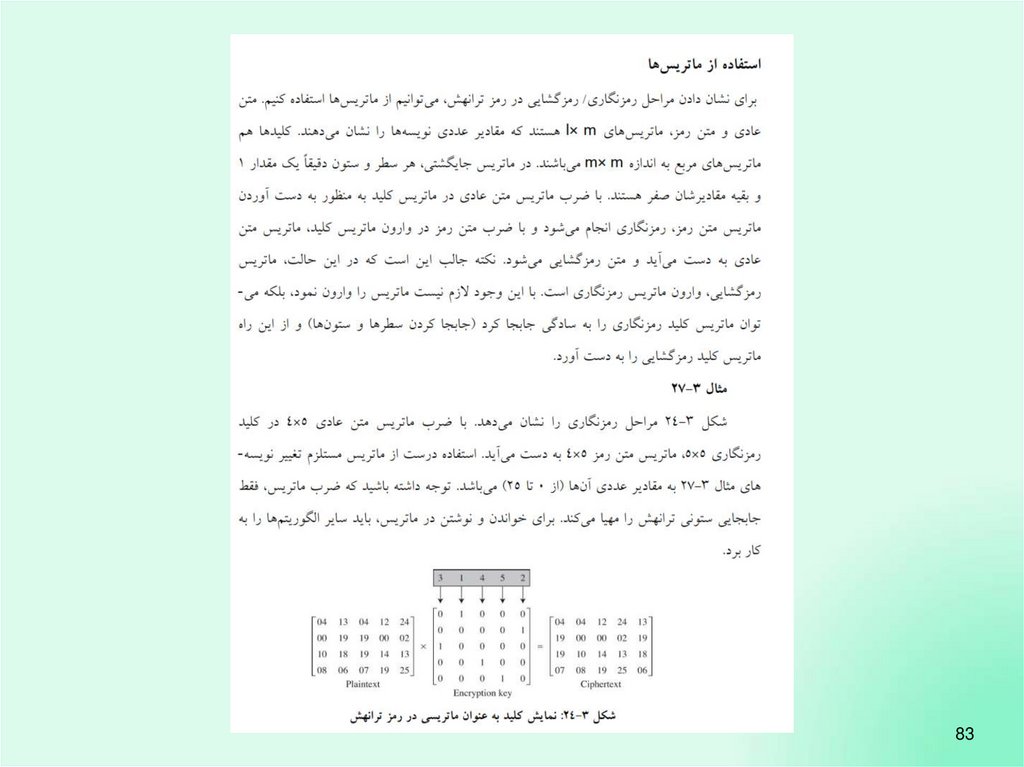
8273.
8374.
8475.
8576.
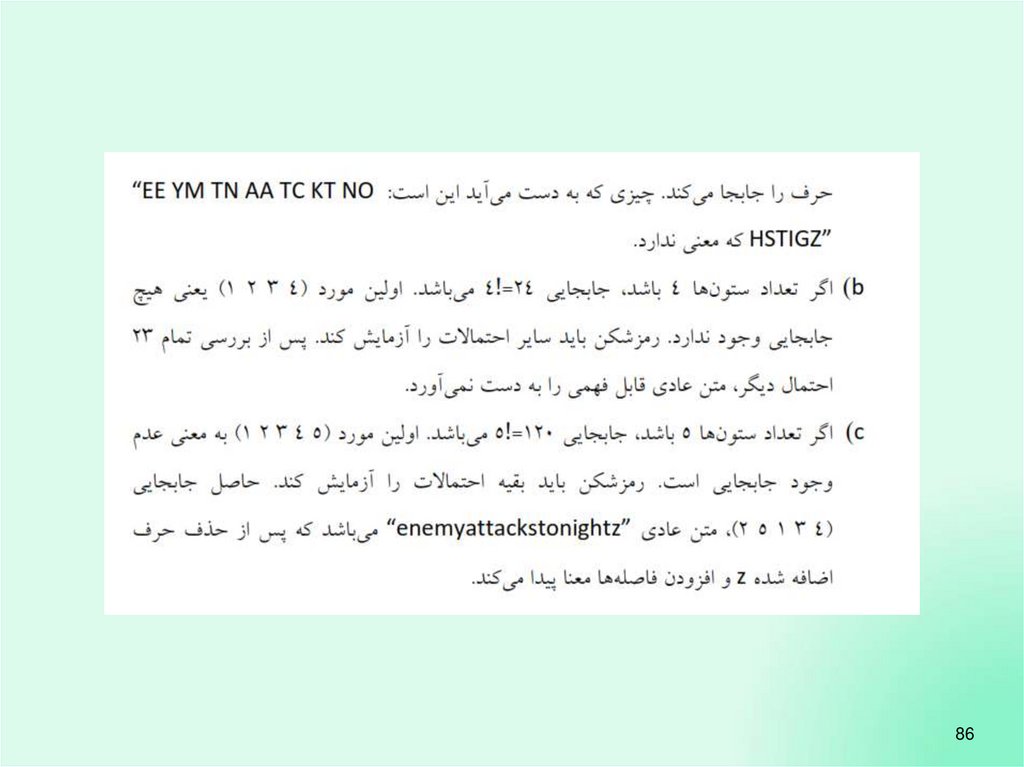
8677.
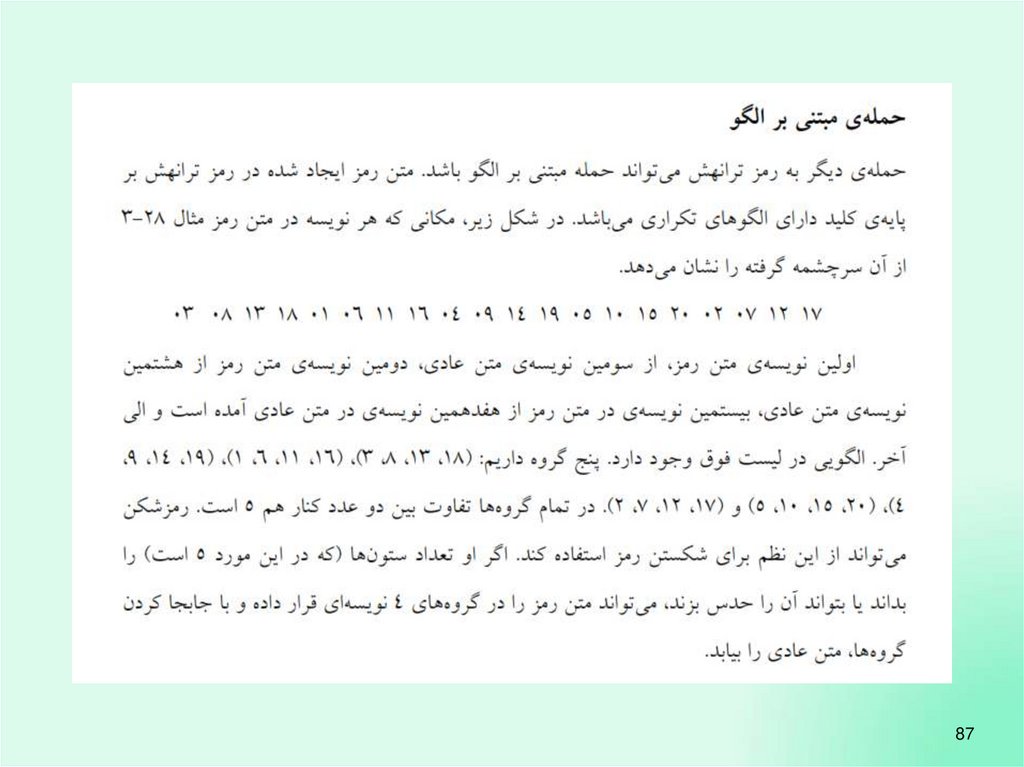
8778.
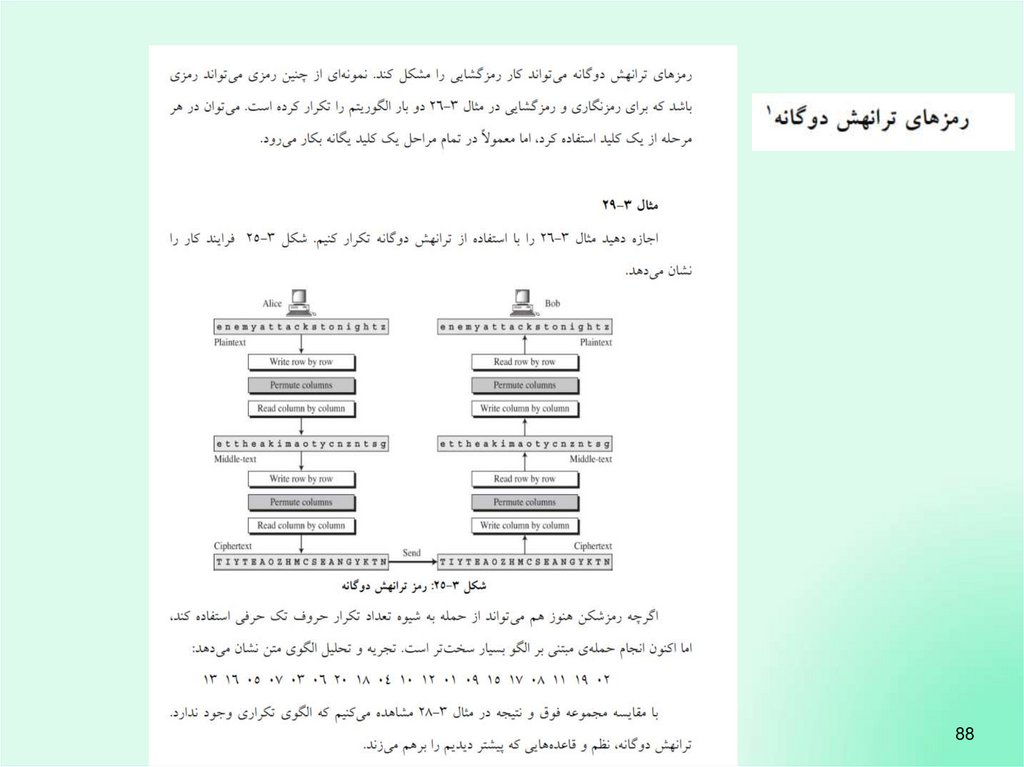
8879.
8980.
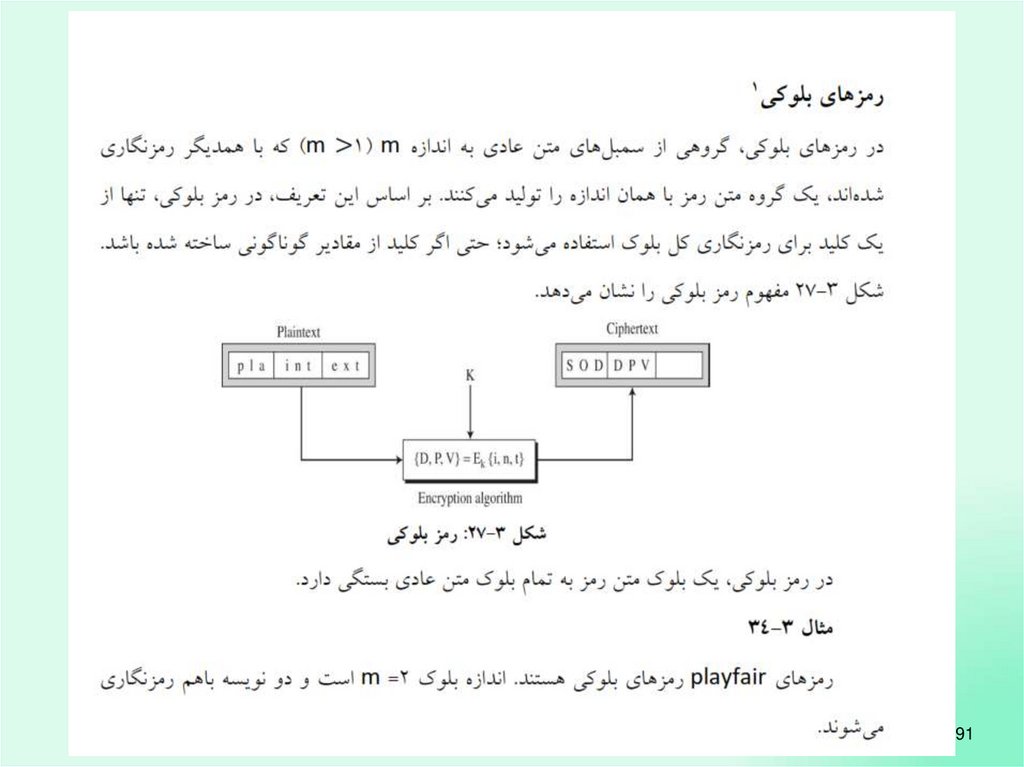
9081.
9182.
9283.
9384.
The language of cryptographyAlice’s
K encryption
A
key
plaintext
encryption
algorithm
ciphertext
Bob’s
K decryption
B key
decryption plaintext
algorithm
symmetric key crypto: sender, receiver keys identical
public-key crypto: encryption key public, decryption key
secret (private)
8: Network Security
8-94
85.
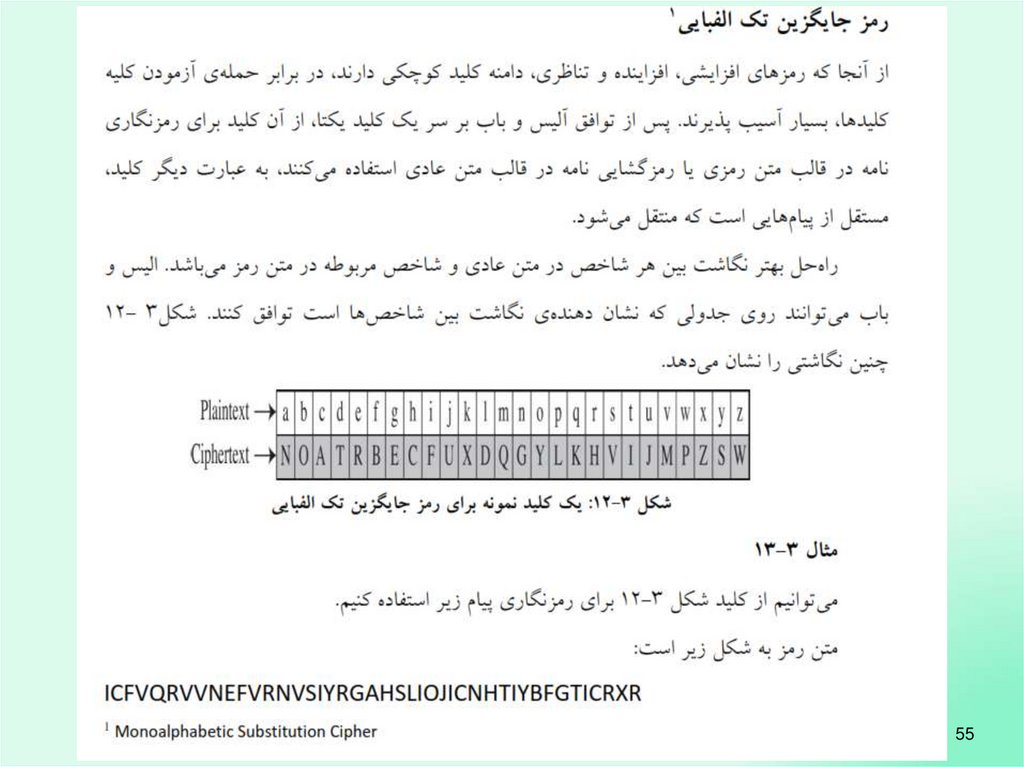
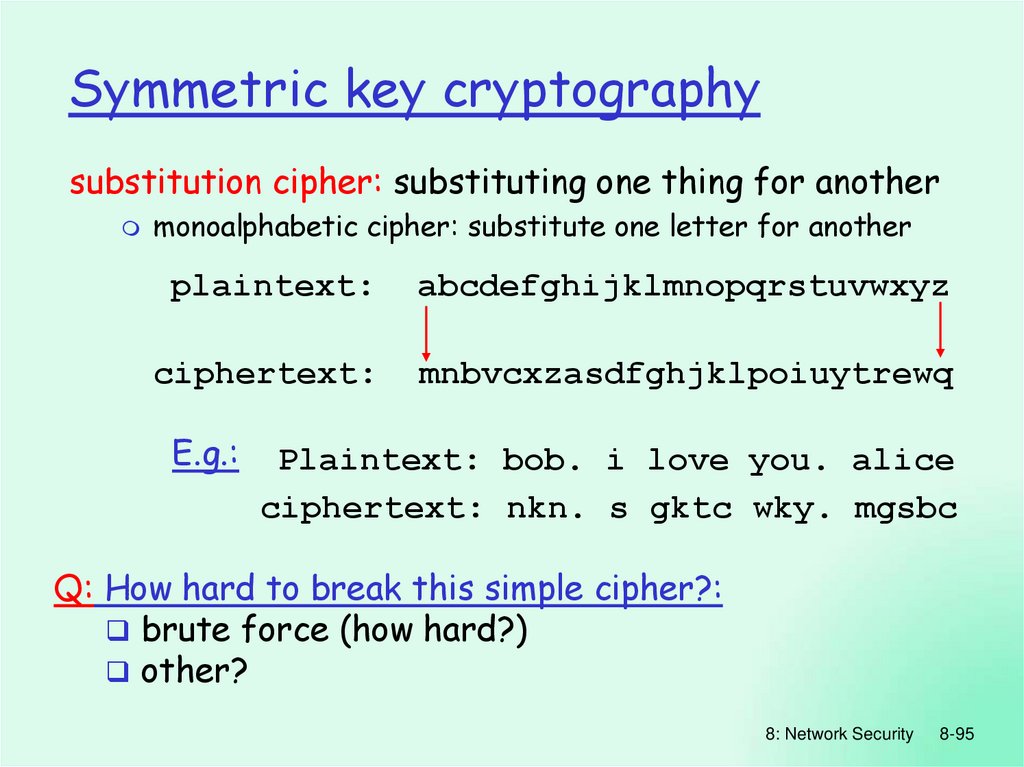
Symmetric key cryptographysubstitution cipher: substituting one thing for another
monoalphabetic cipher: substitute one letter for another
plaintext:
abcdefghijklmnopqrstuvwxyz
ciphertext:
mnbvcxzasdfghjklpoiuytrewq
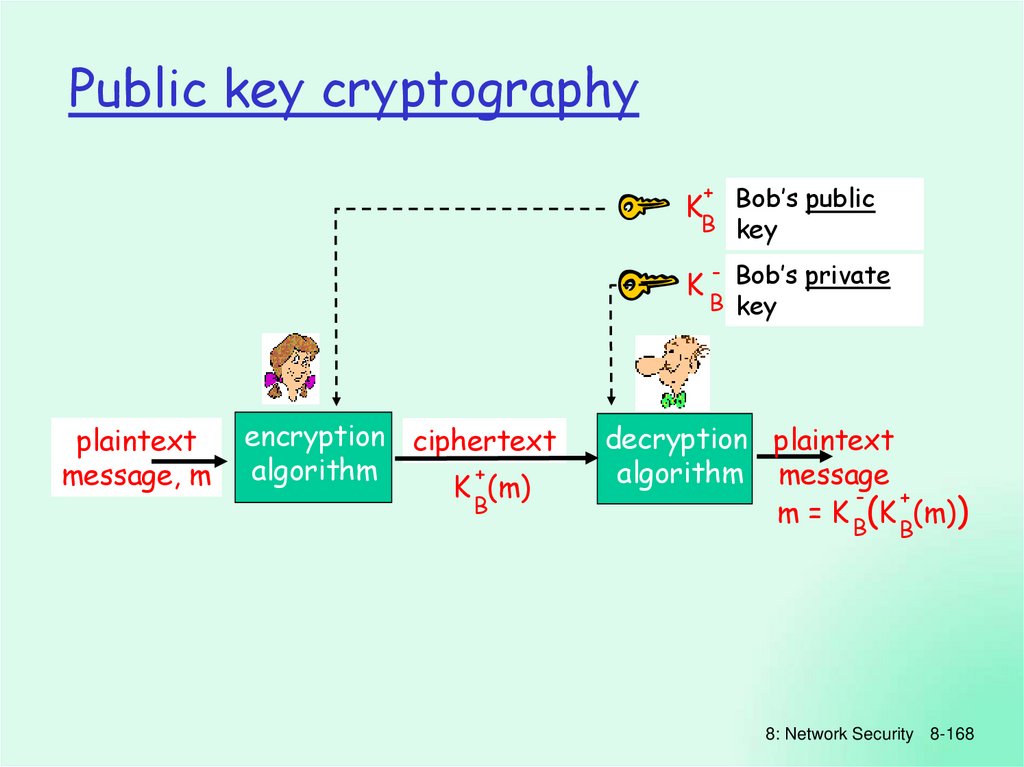
E.g.:
Plaintext: bob. i love you. alice
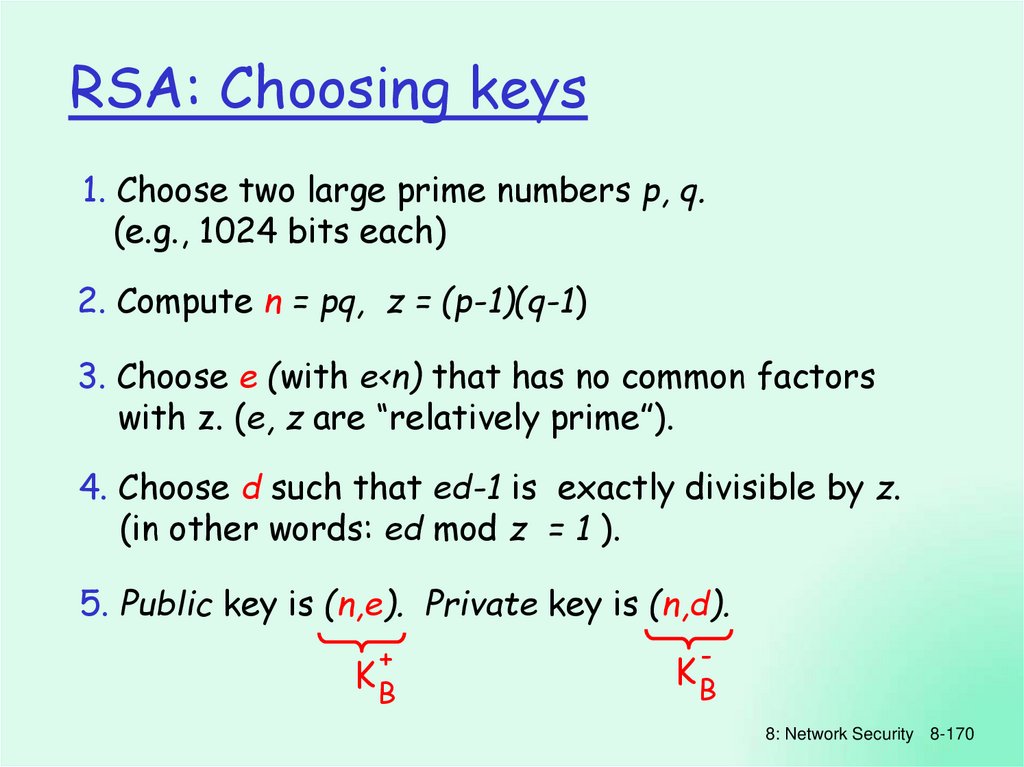
ciphertext: nkn. s gktc wky. mgsbc
Q: How hard to break this simple cipher?:
brute force (how hard?)
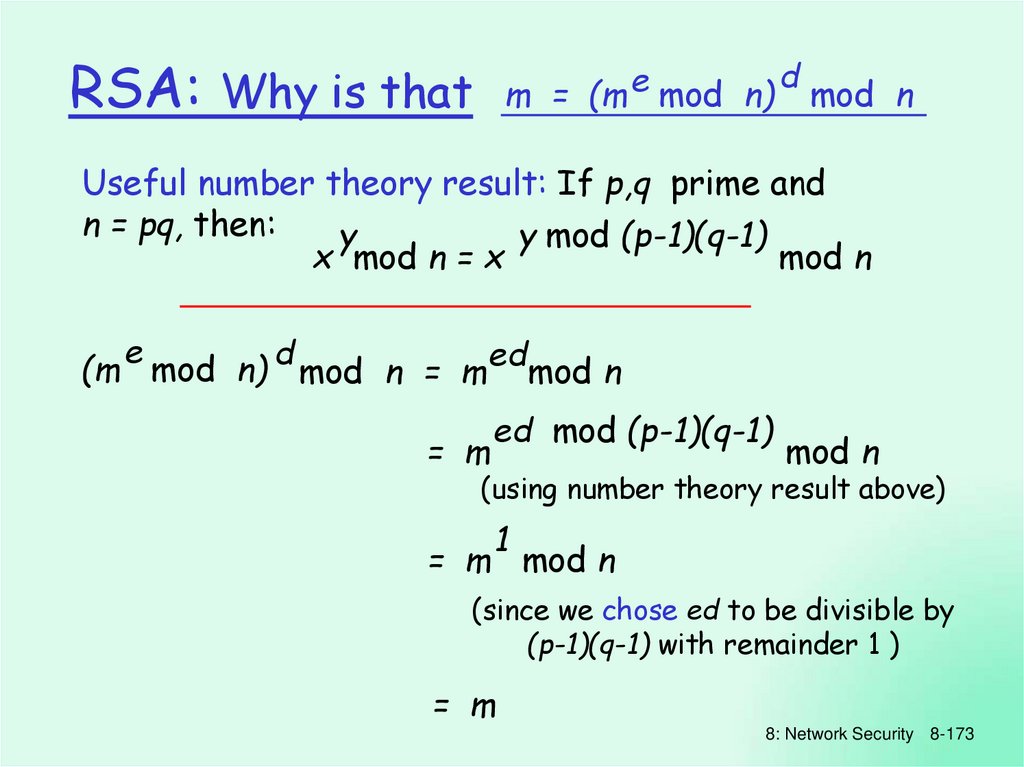
other?
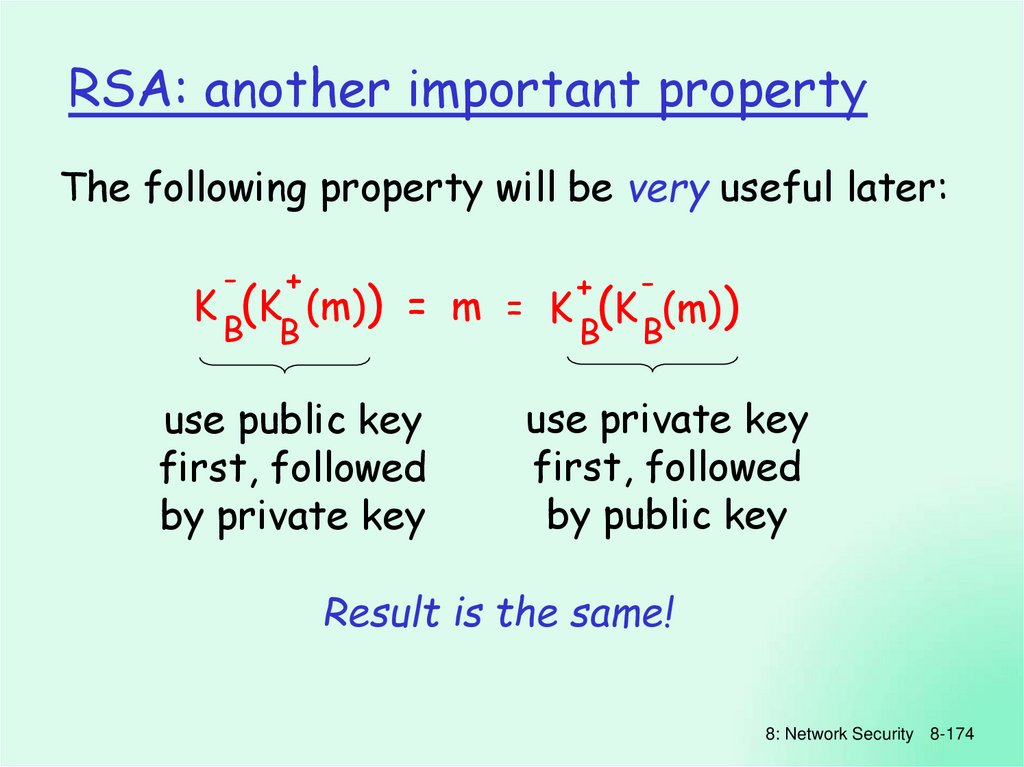
8: Network Security
8-95
86.
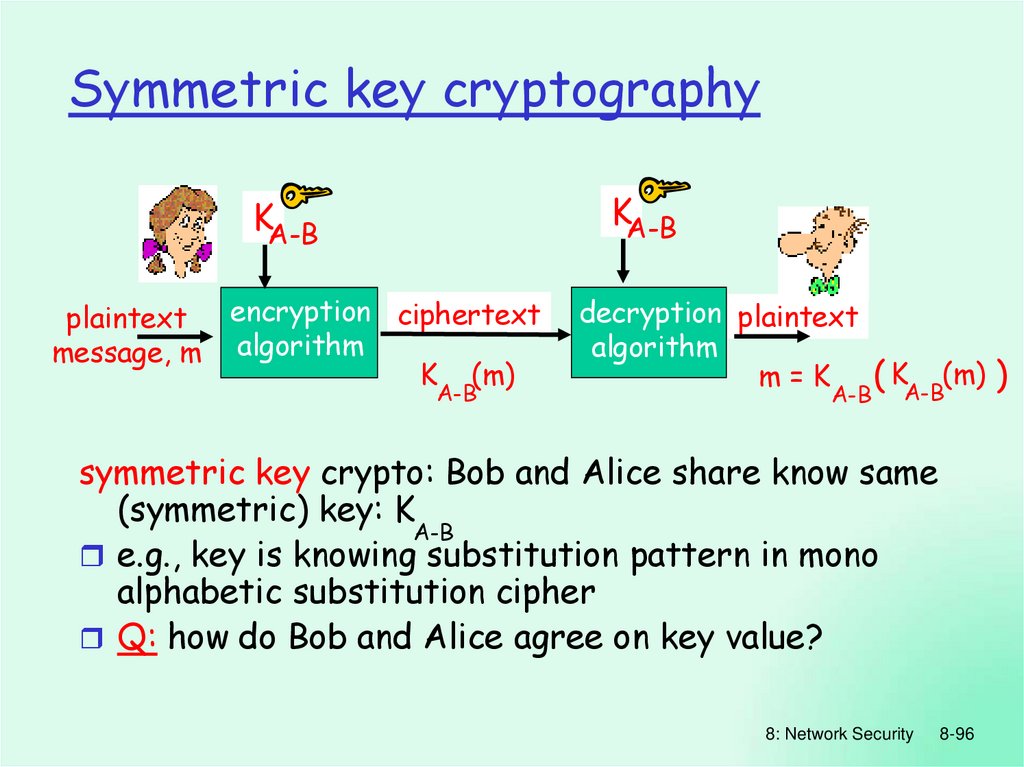
Symmetric key cryptographyKA-B
KA-B
plaintext
message, m
encryption ciphertext
algorithm
K (m)
A-B
decryption plaintext
algorithm
m = K ( KA-B(m) )
A-B
symmetric key crypto: Bob and Alice share know same
(symmetric) key: K
A-B
e.g., key is knowing substitution pattern in mono
alphabetic substitution cipher
Q: how do Bob and Alice agree on key value?
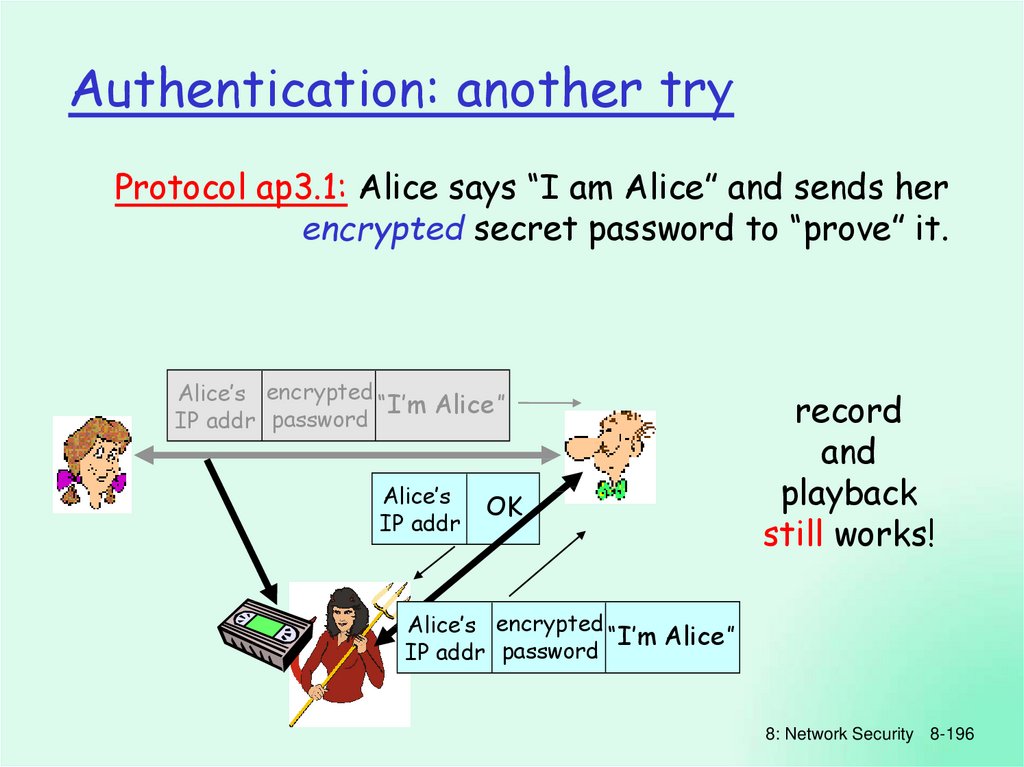
8: Network Security
8-96
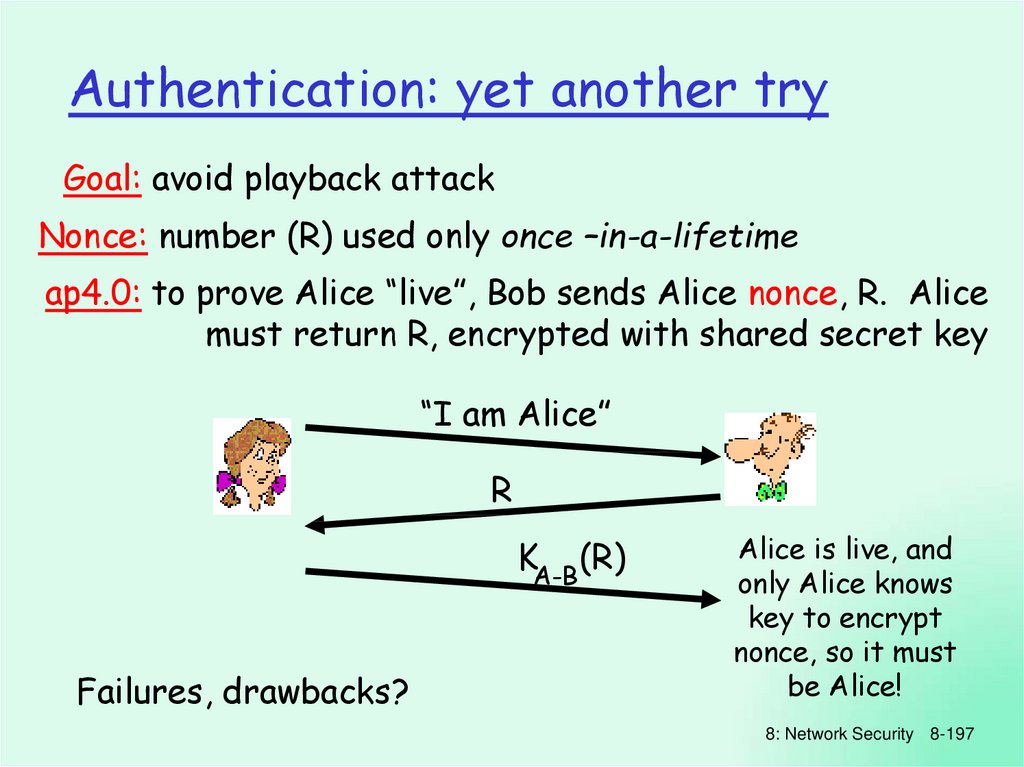
87.
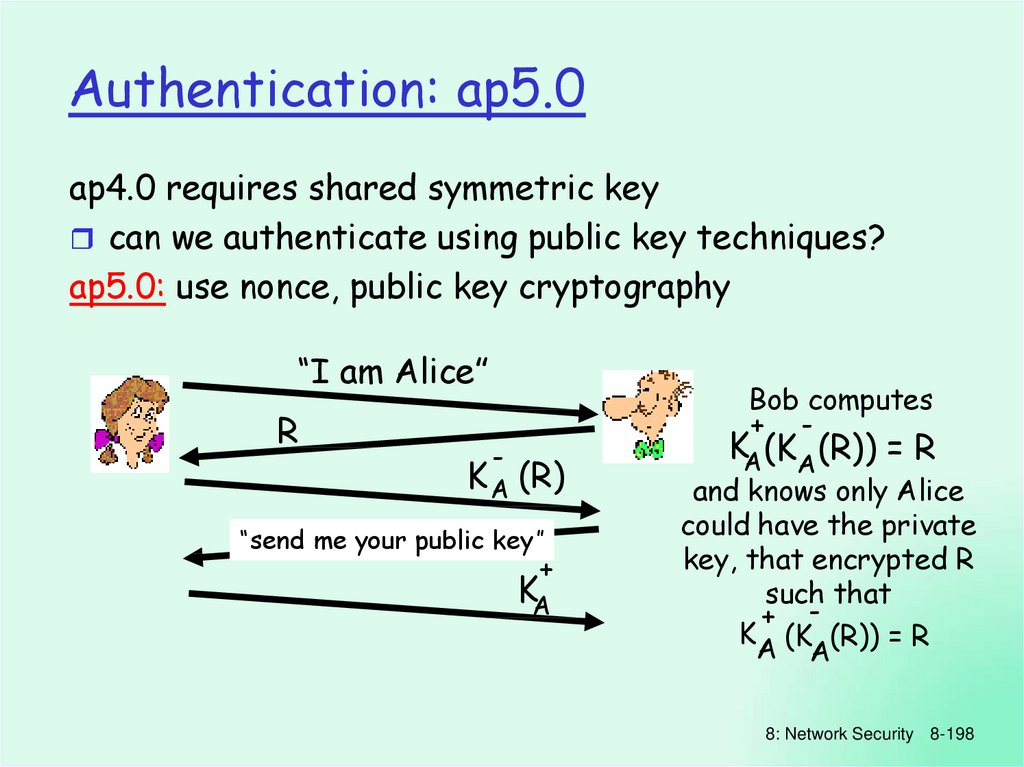
8: Network Security8-97
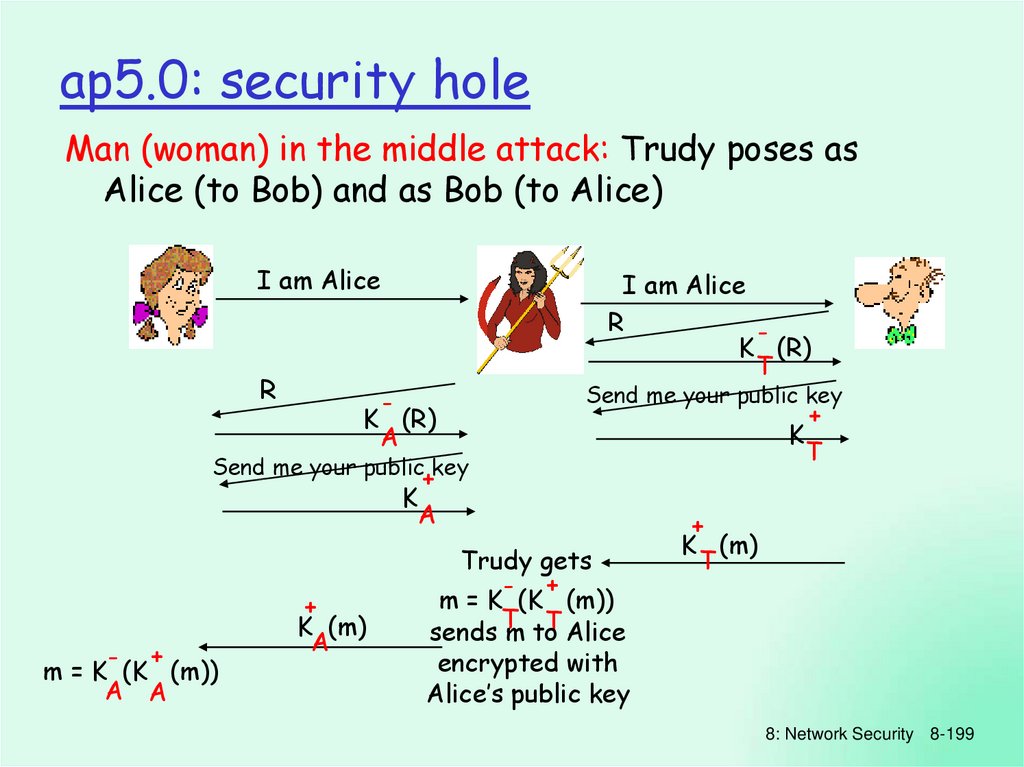
88.
8: Network Security8-98
89.
9990.
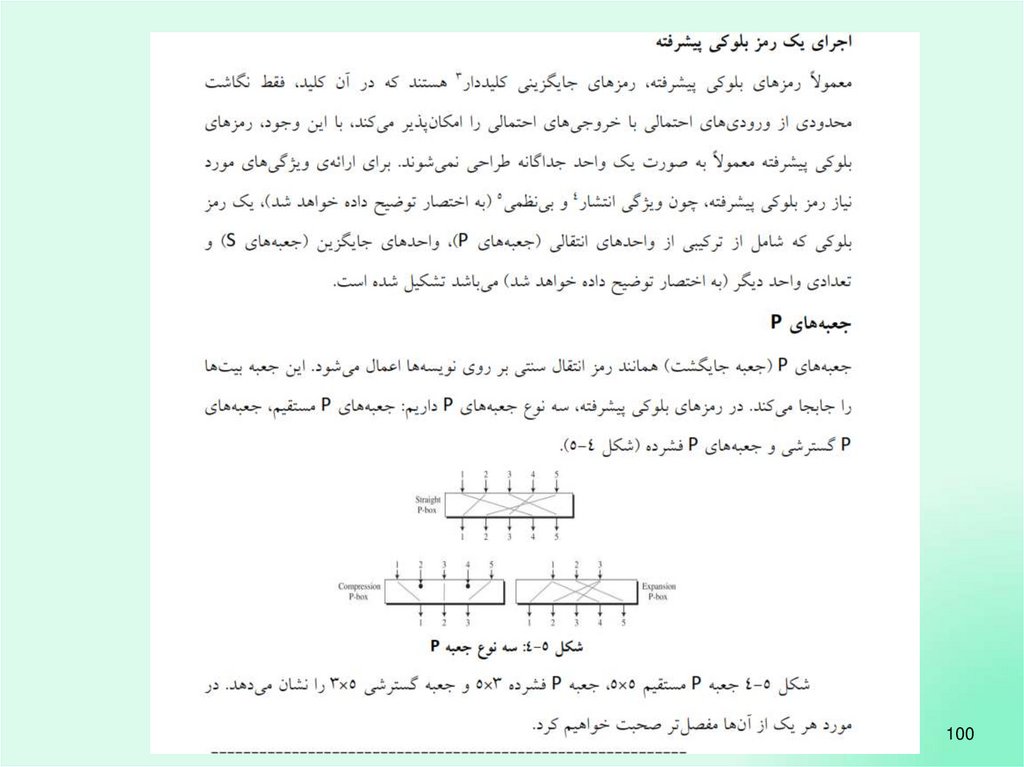
10091.
10192.
10293.
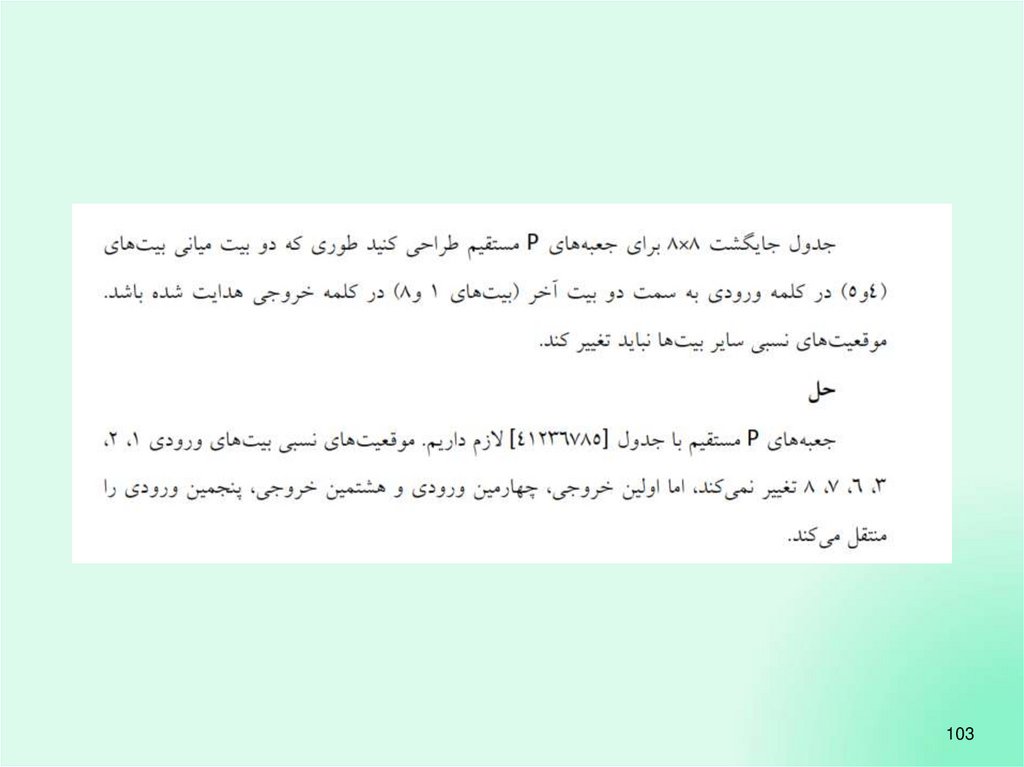
10394. The language of cryptography
10495. Symmetric key cryptography
10596. Symmetric key cryptography
10697.
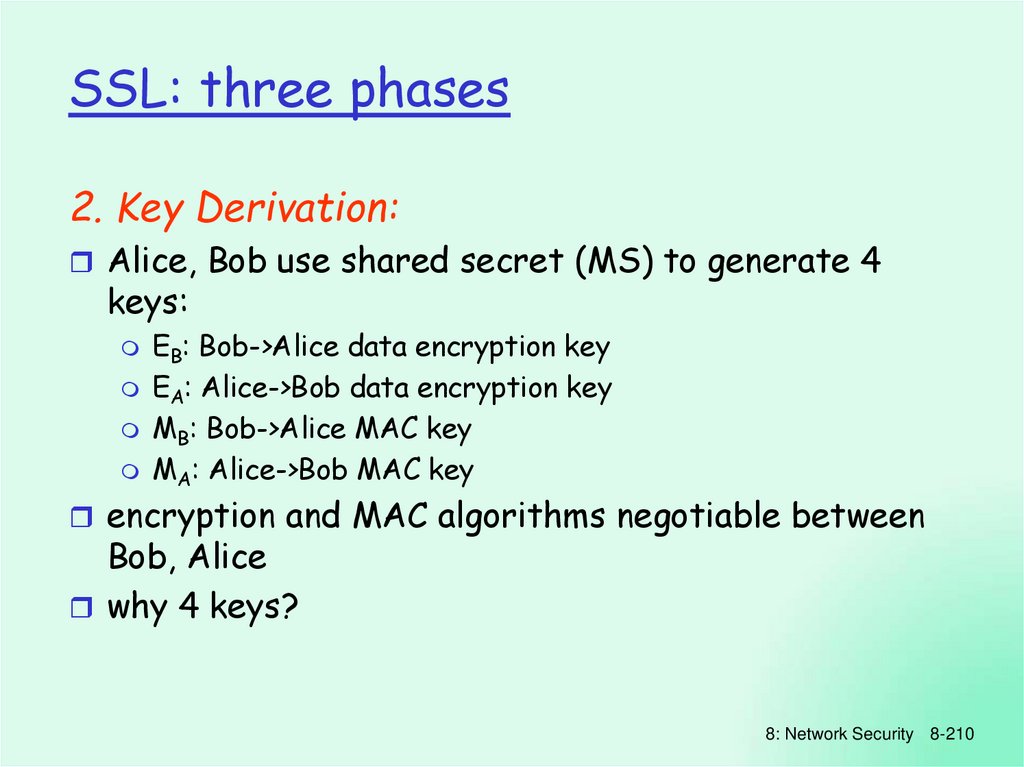
10798.
10899.
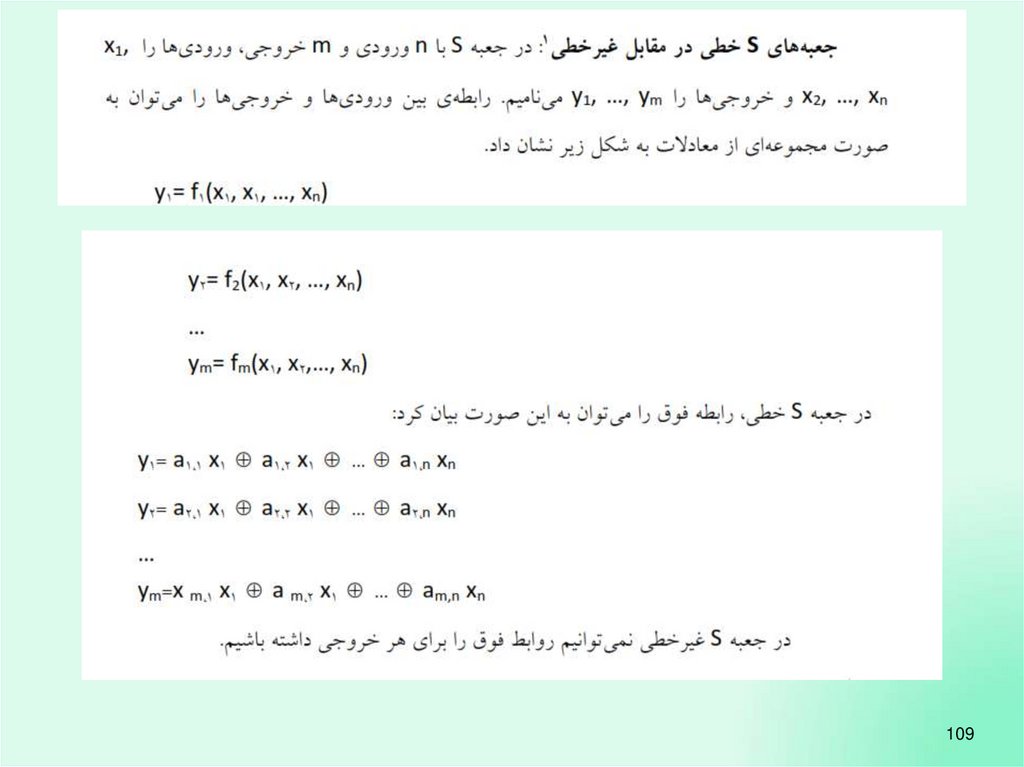
109100.
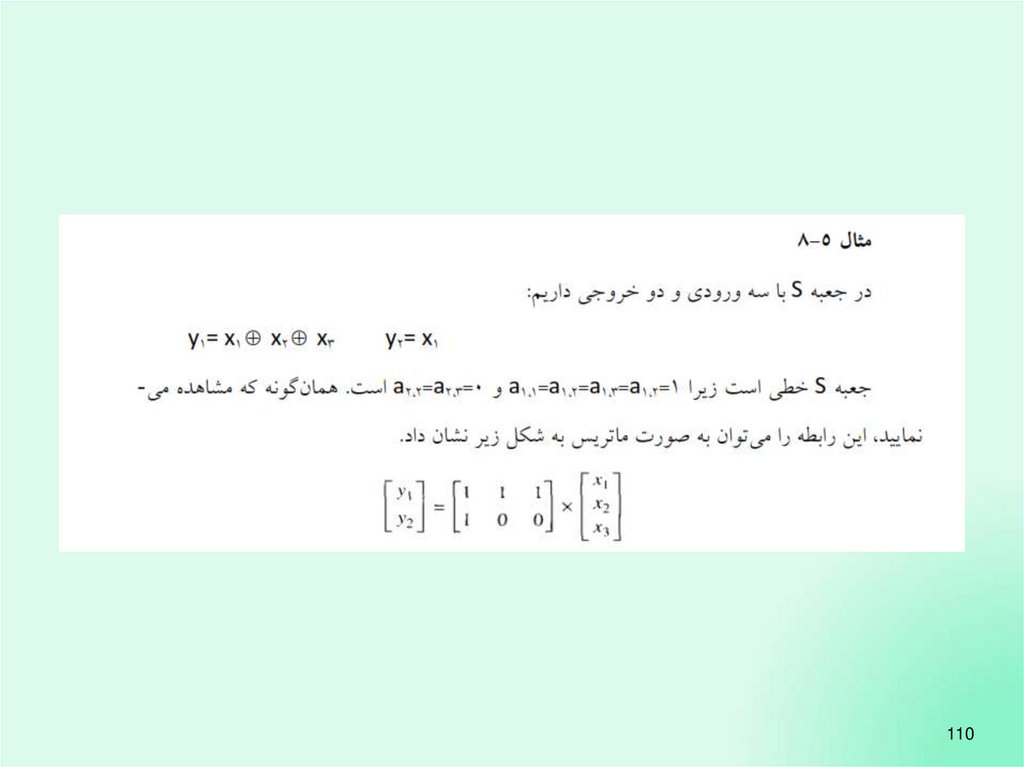
110101.
111102.
112103.
113104.
114105.
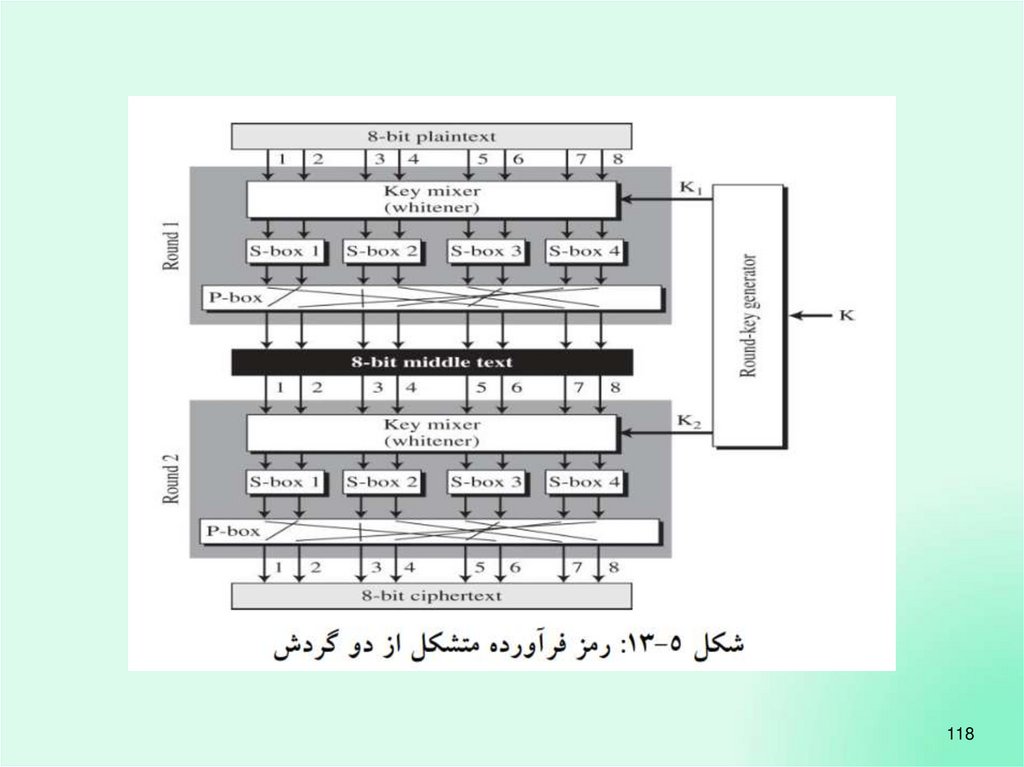
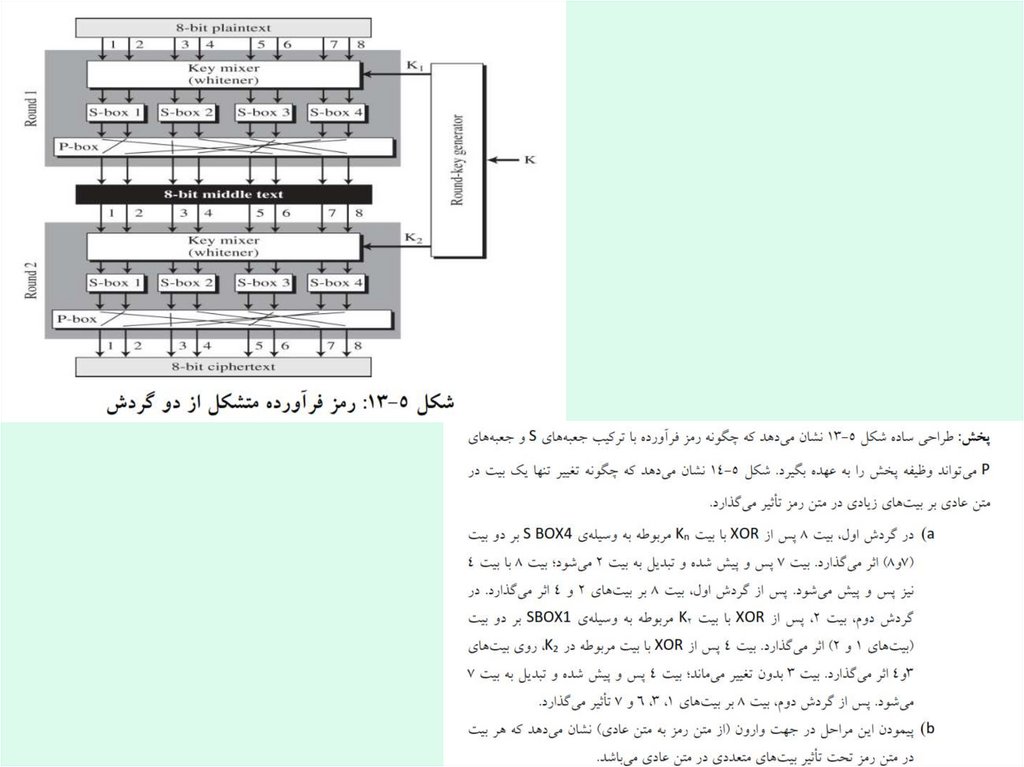
115106.
116107.
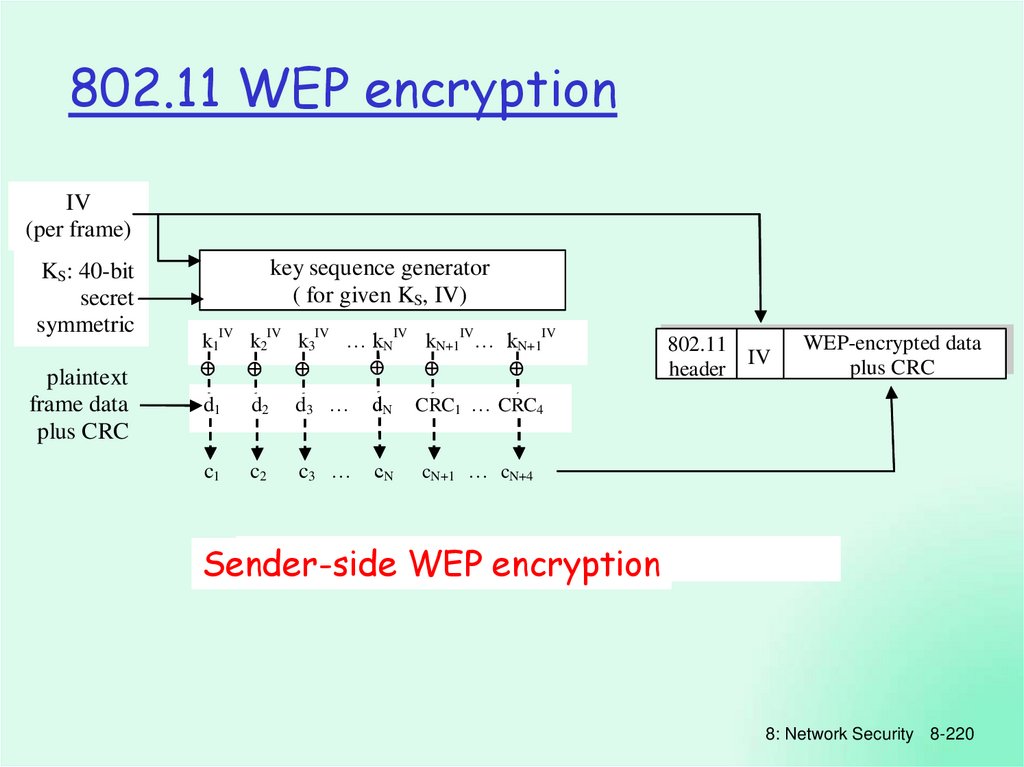
117108.
118109.
119110.
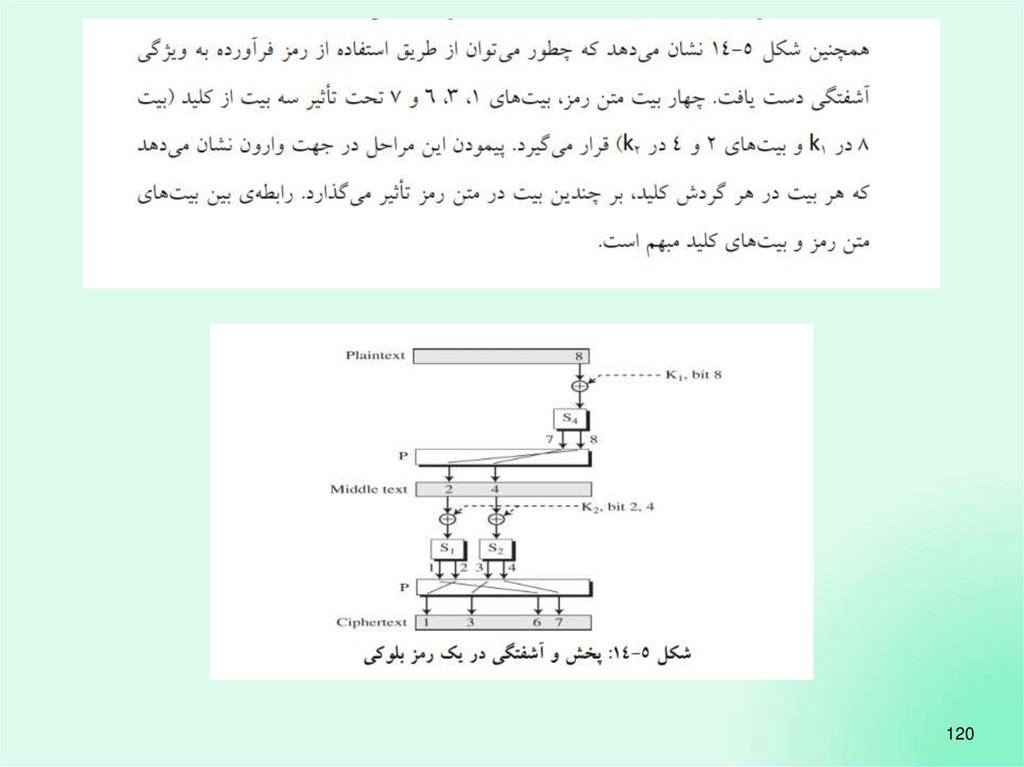
120111.
121112.
122113.
123114.
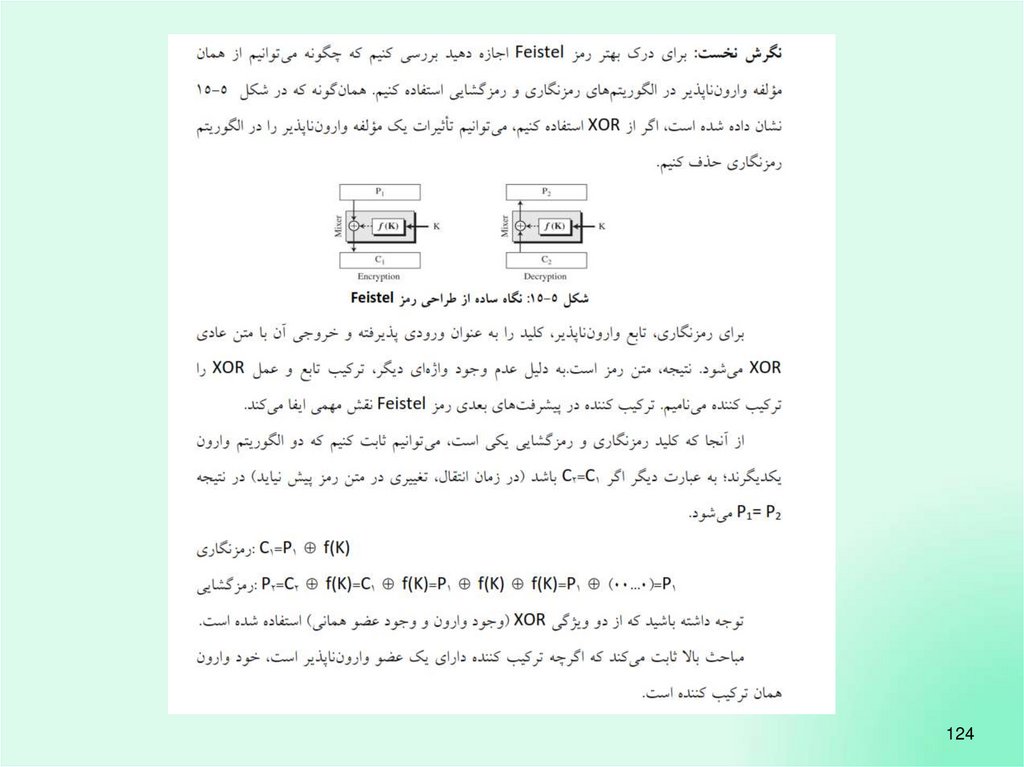
124115.
125116.
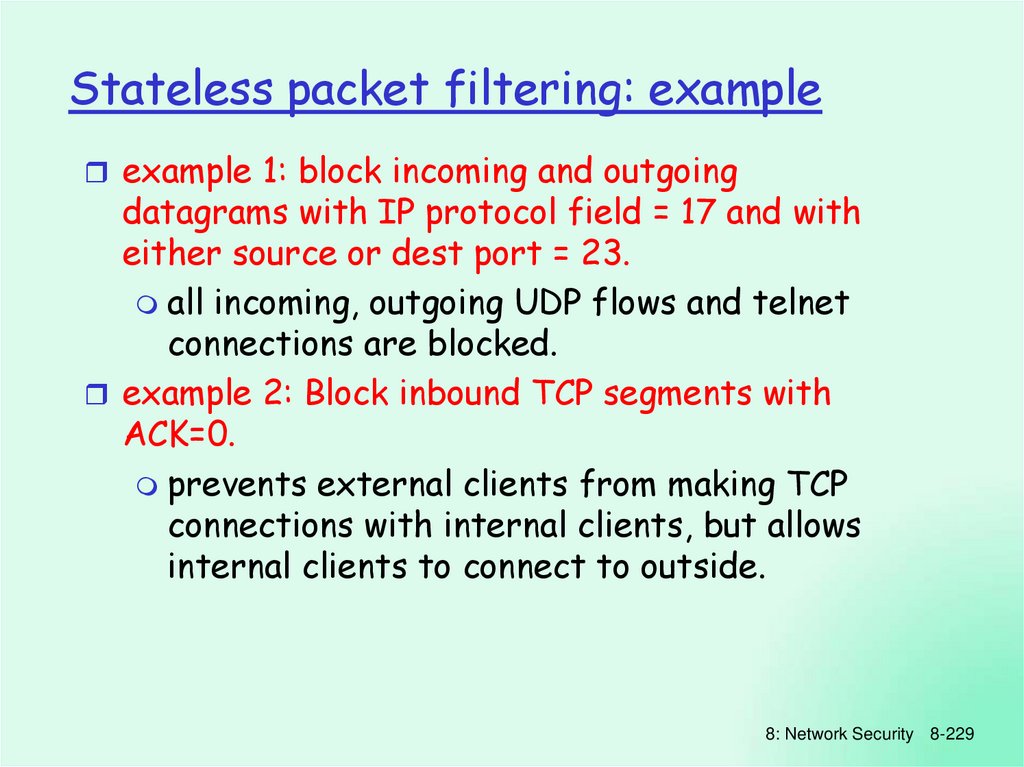
126117.
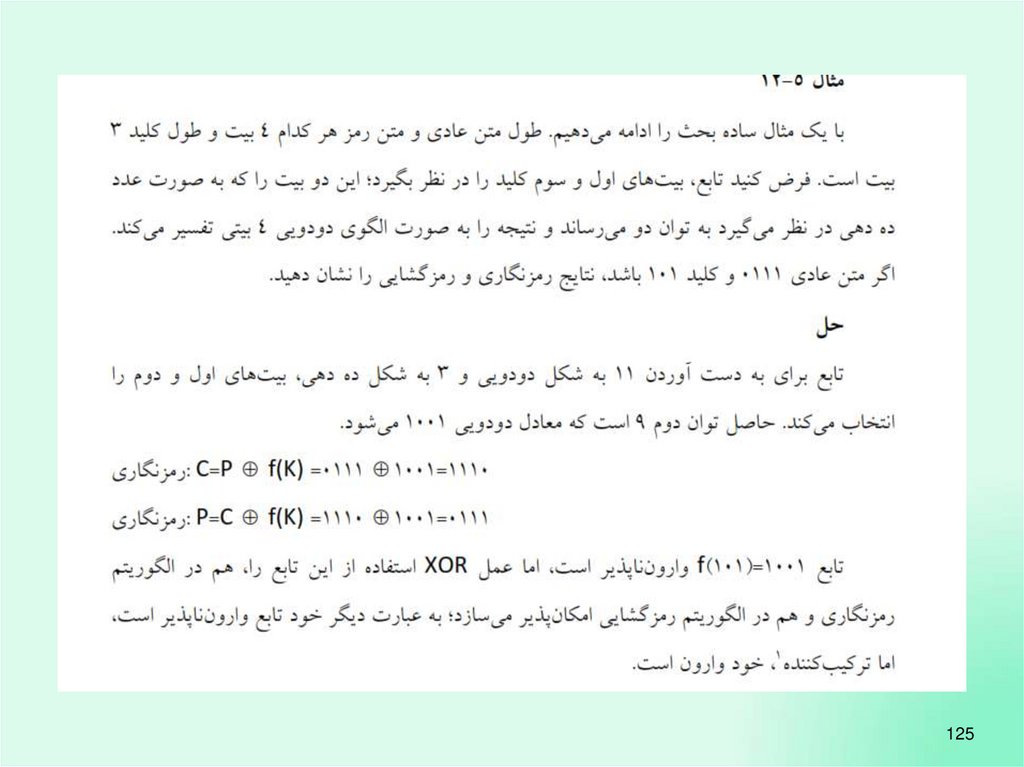
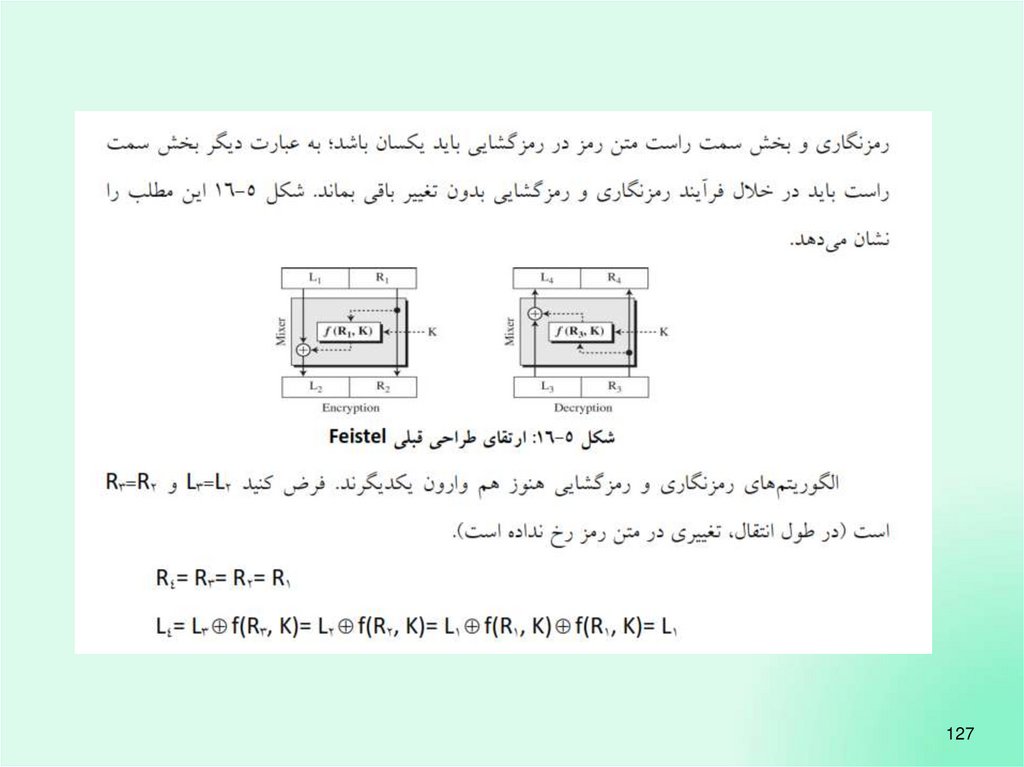
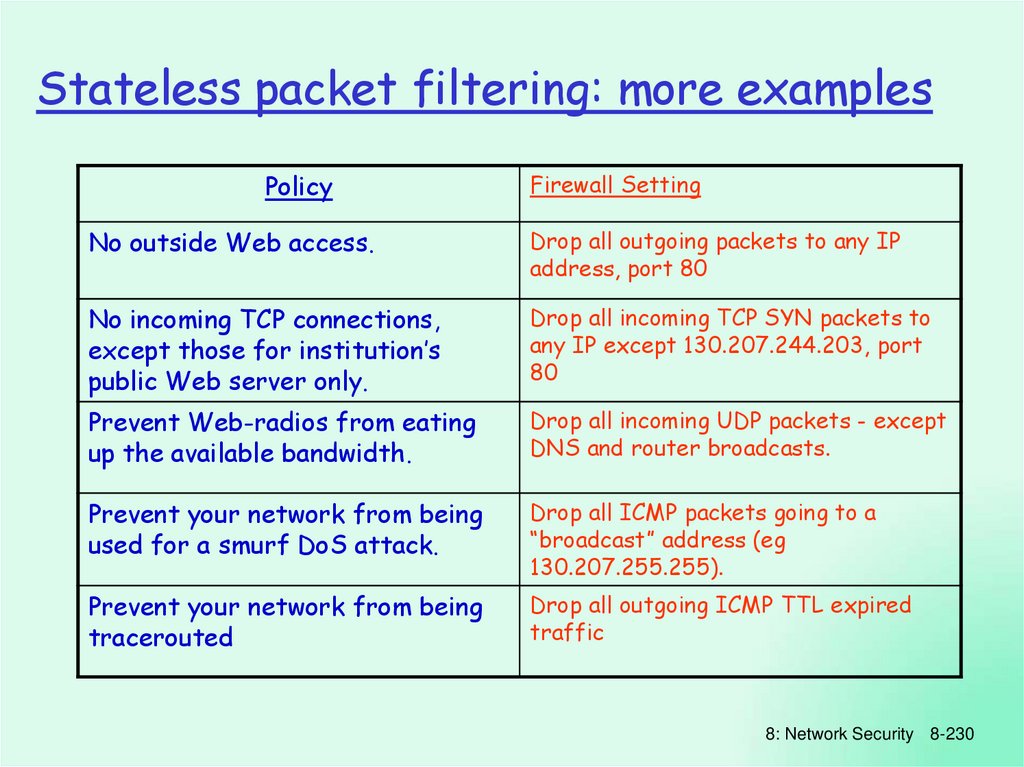
127118.
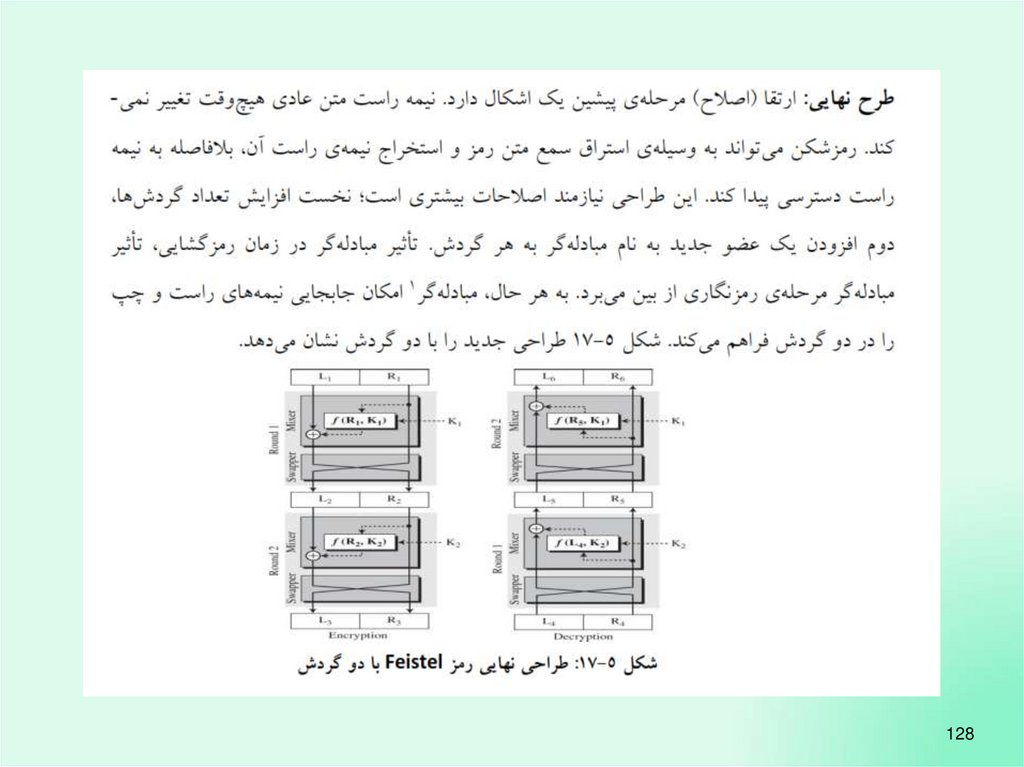
128119.
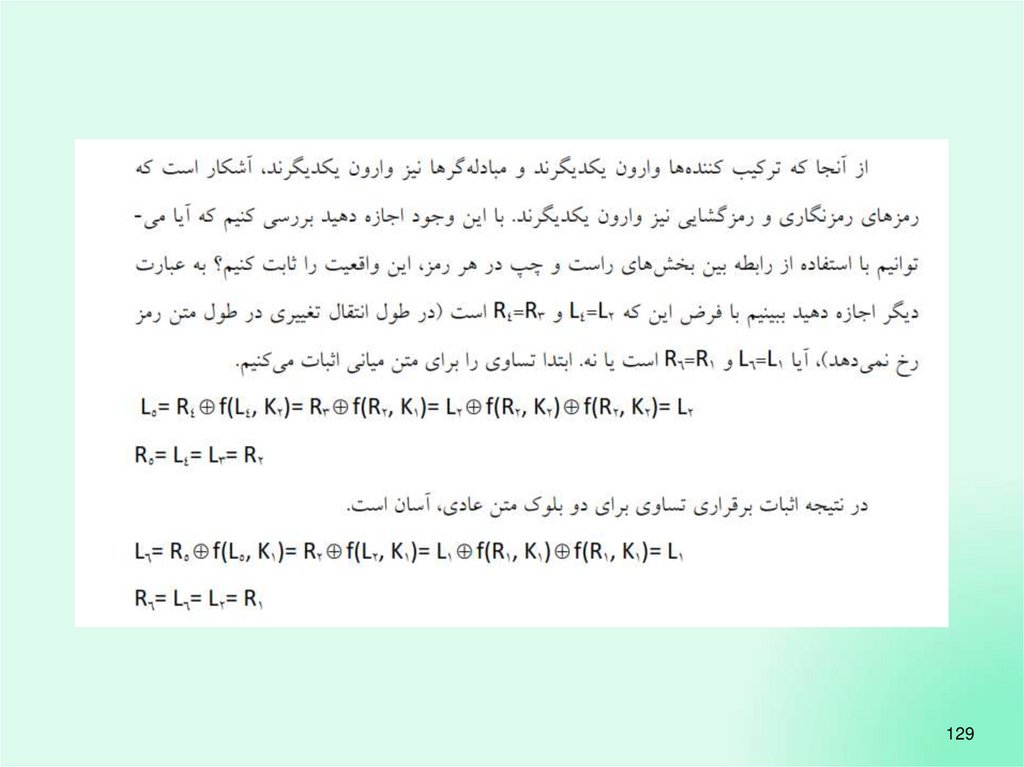
129120.
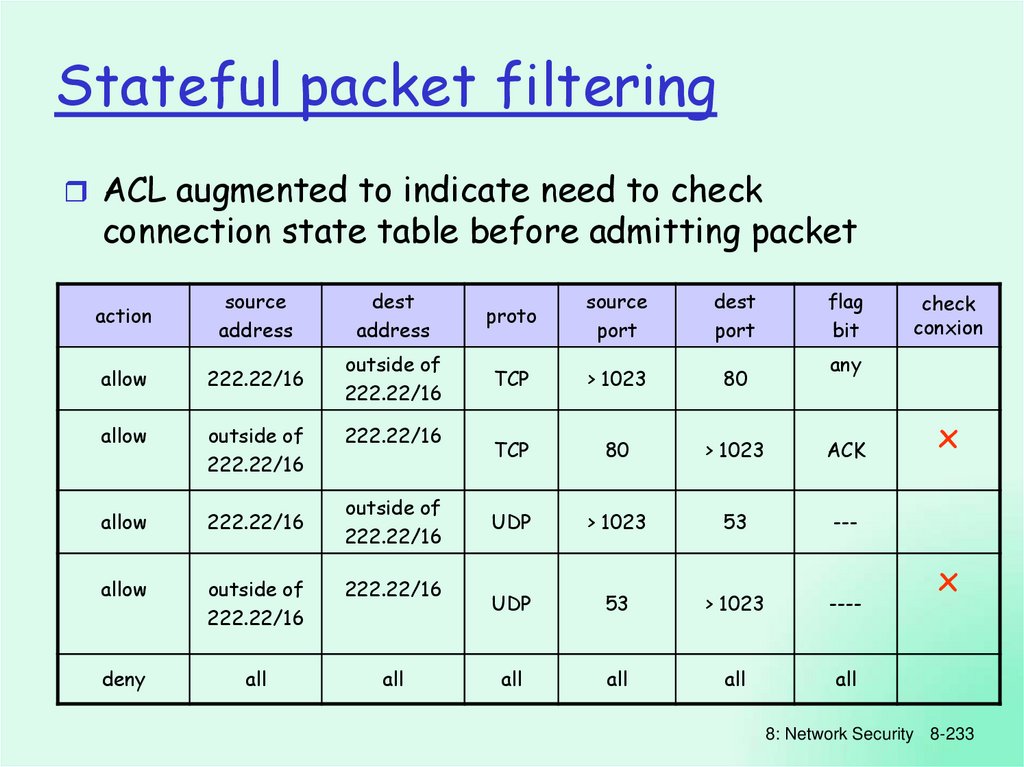
130121.
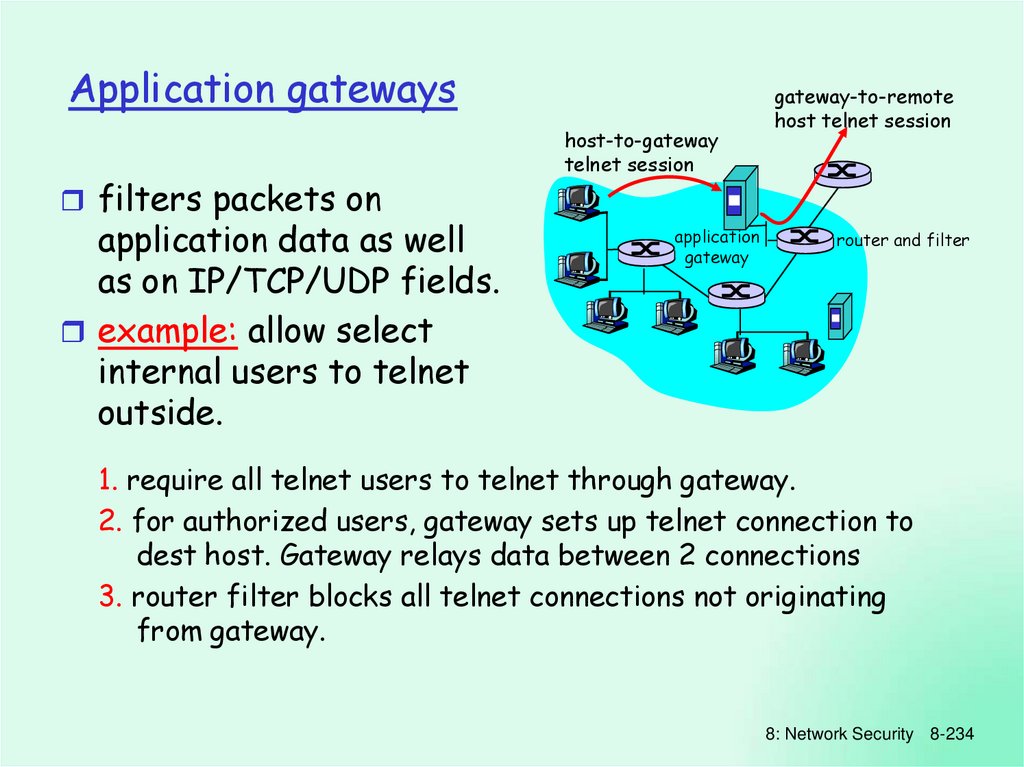
131122.
132123.
133124.
134125.
135126.
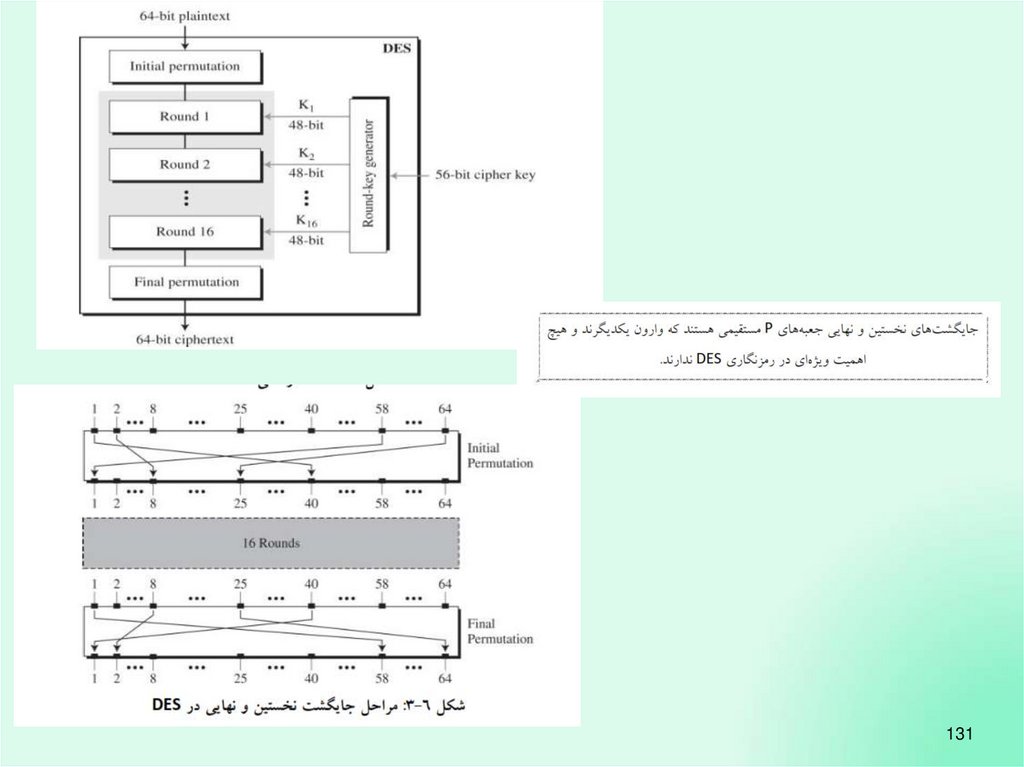
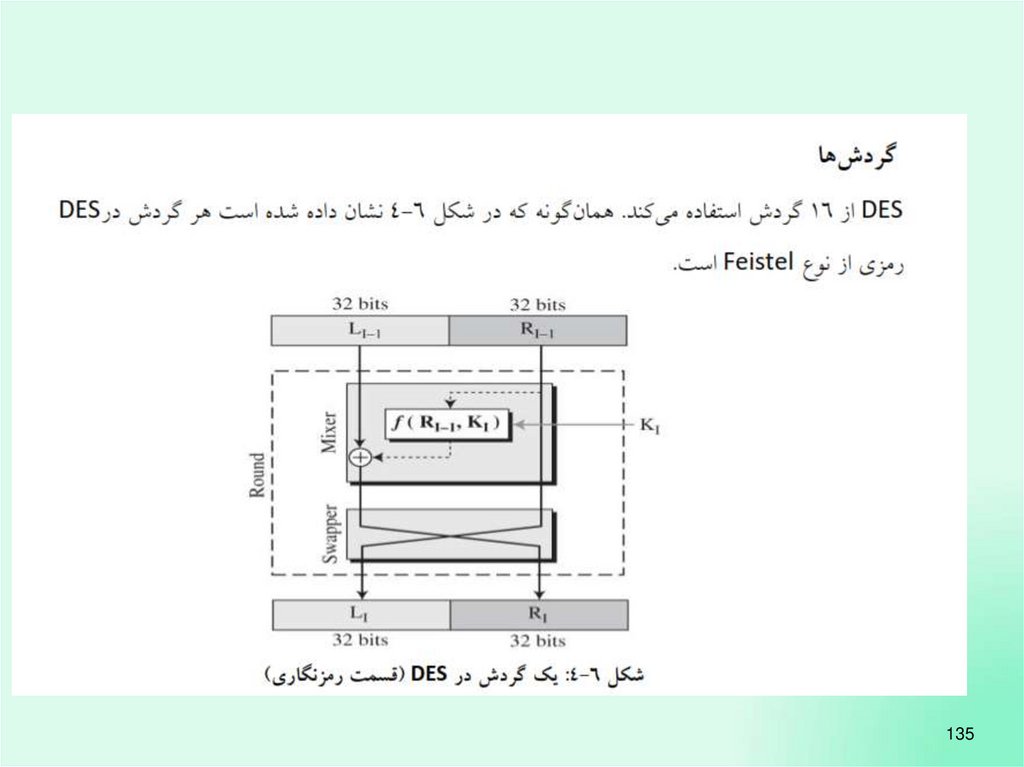
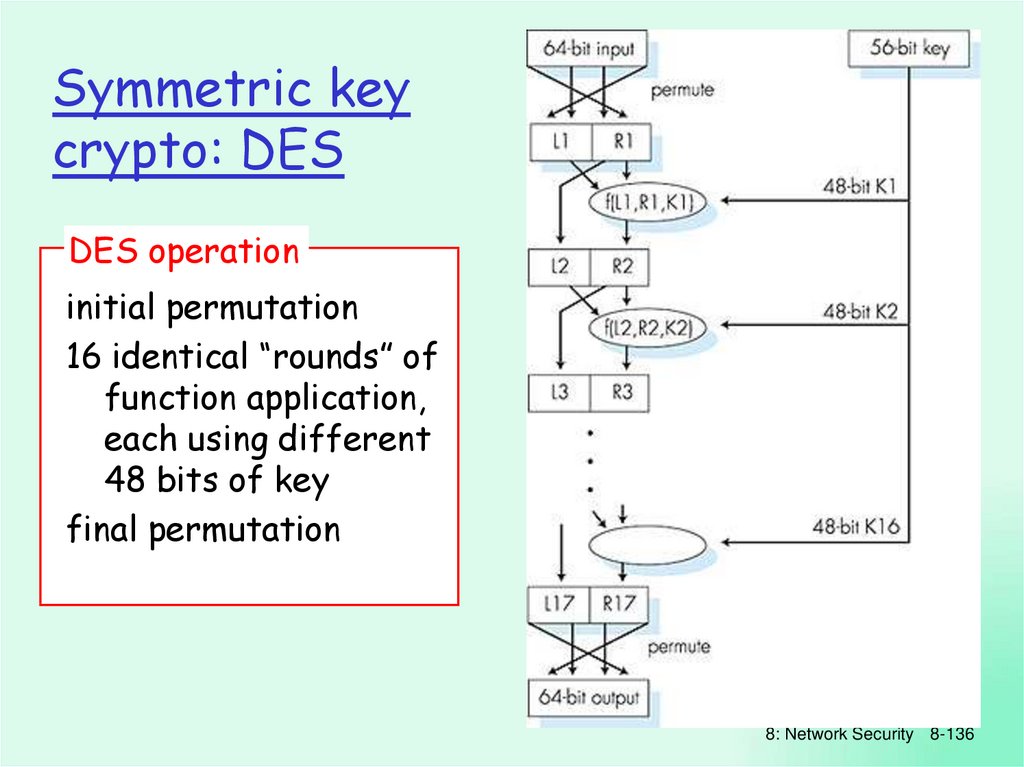
Symmetric keycrypto: DES
DES operation
initial permutation
16 identical “rounds” of
function application,
each using different
48 bits of key
final permutation
8: Network Security 8-136
127.
137128.
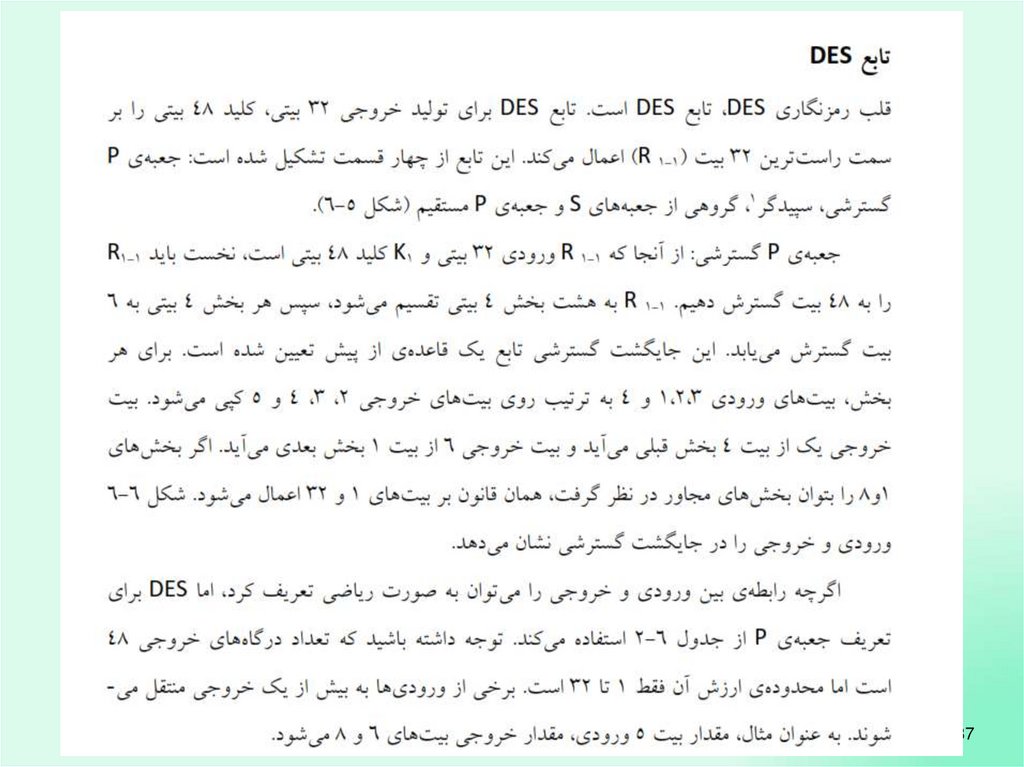
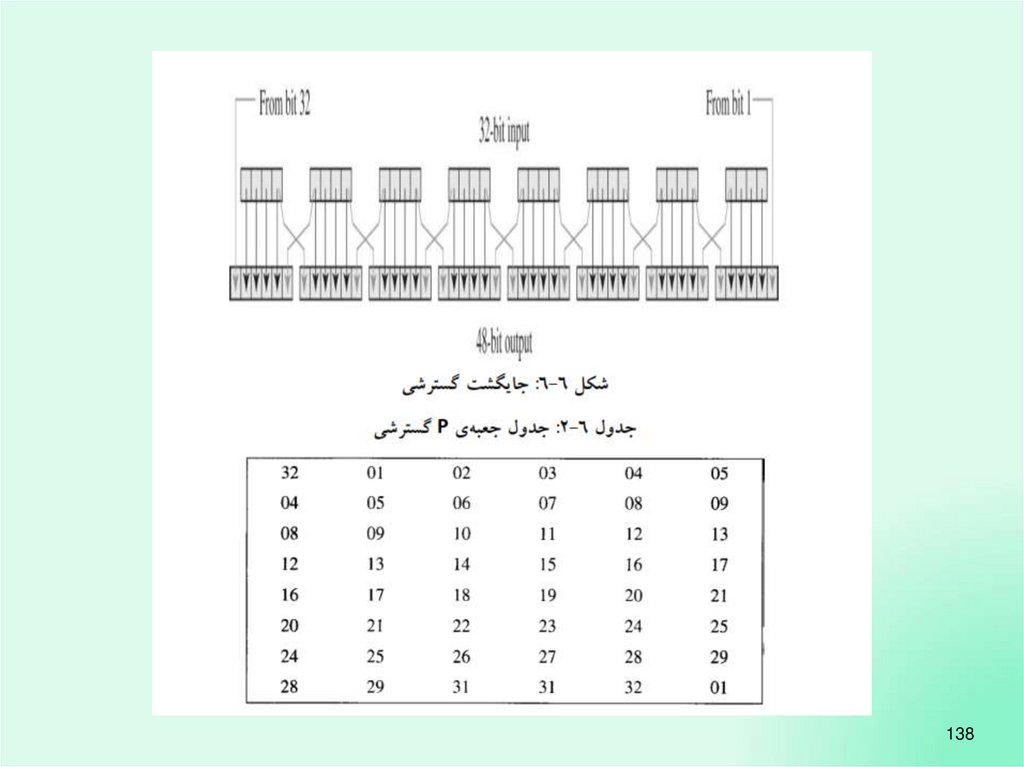
138129.
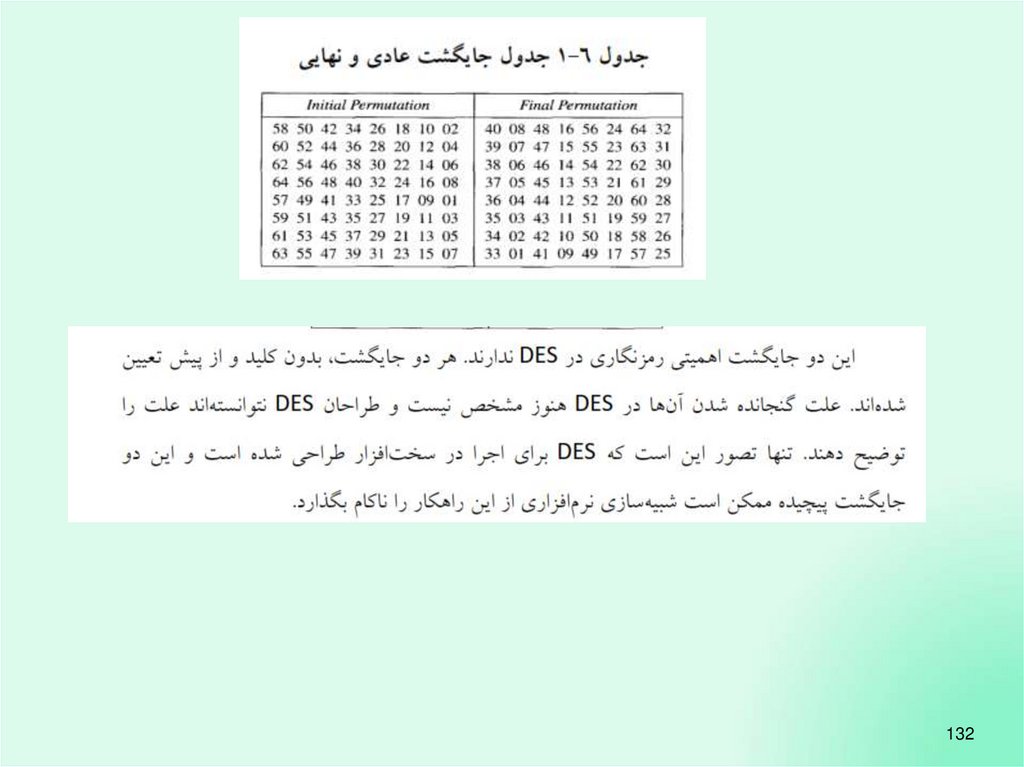
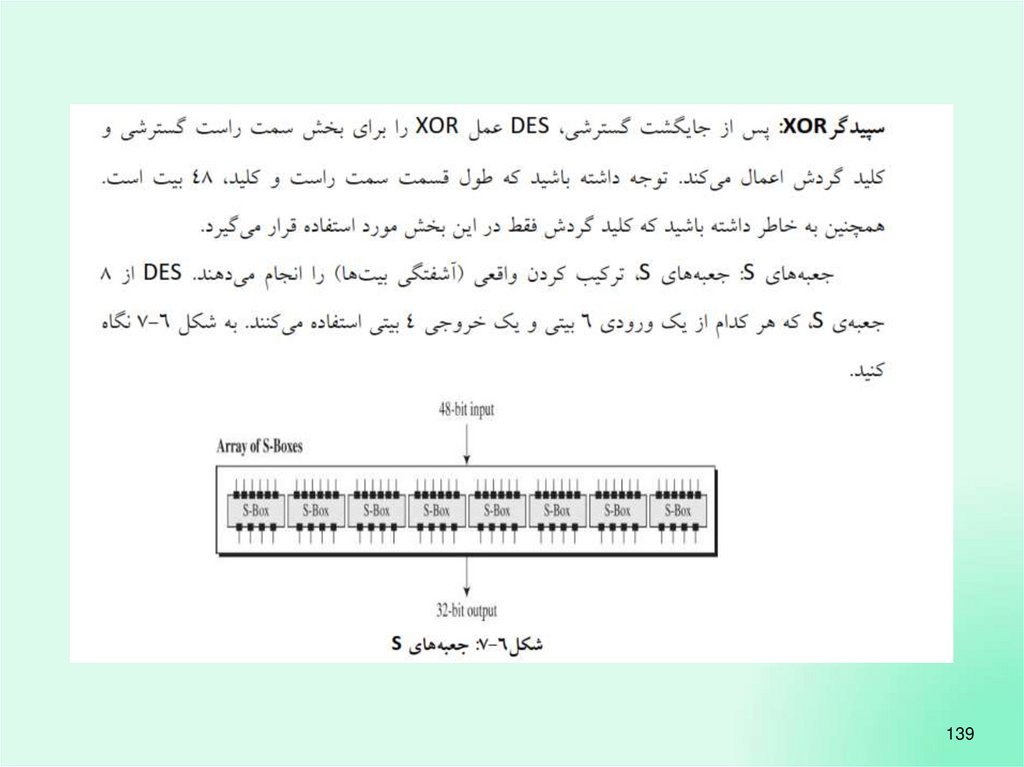
139130.
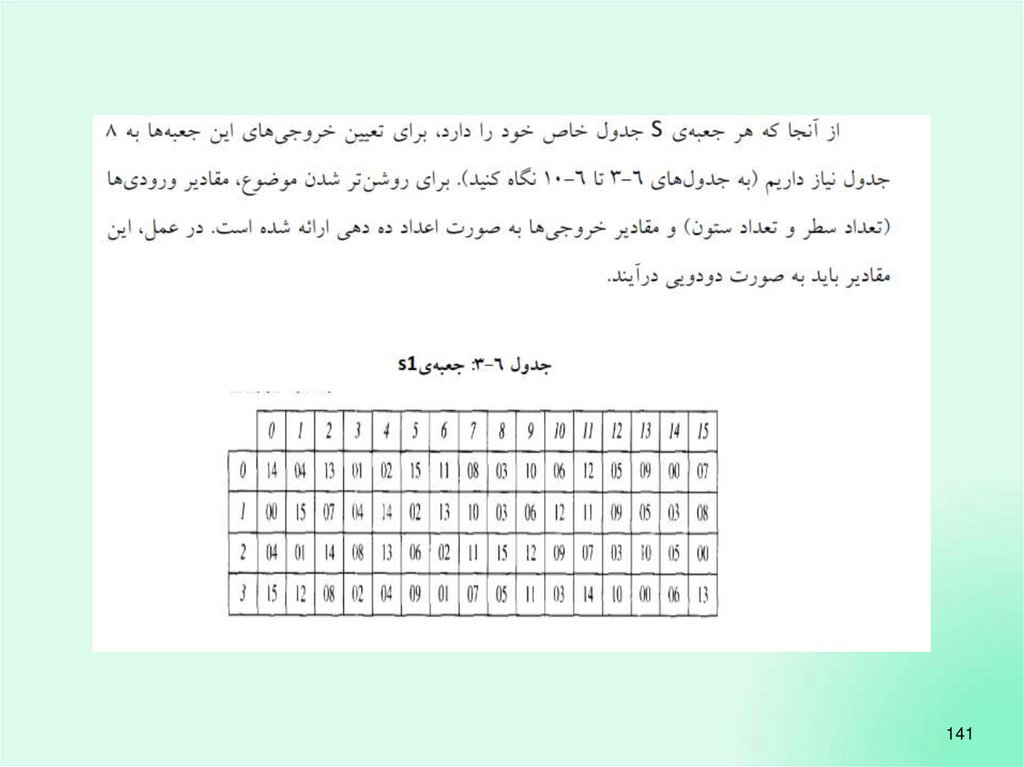
140131.
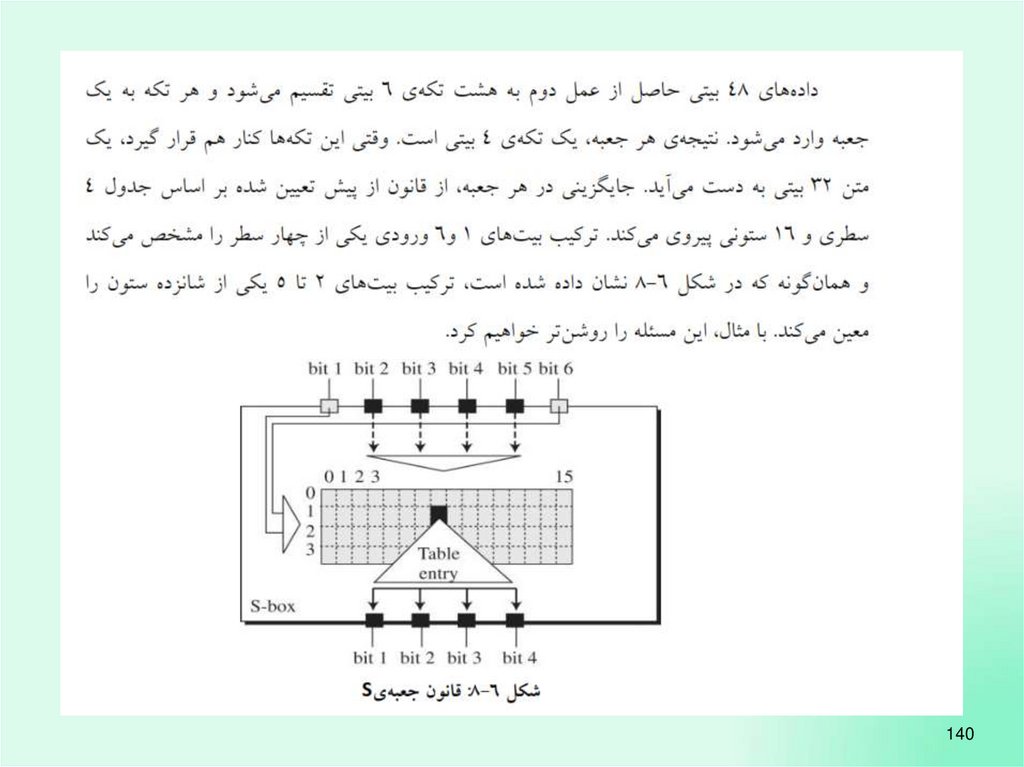
141132.
142133.
143134.
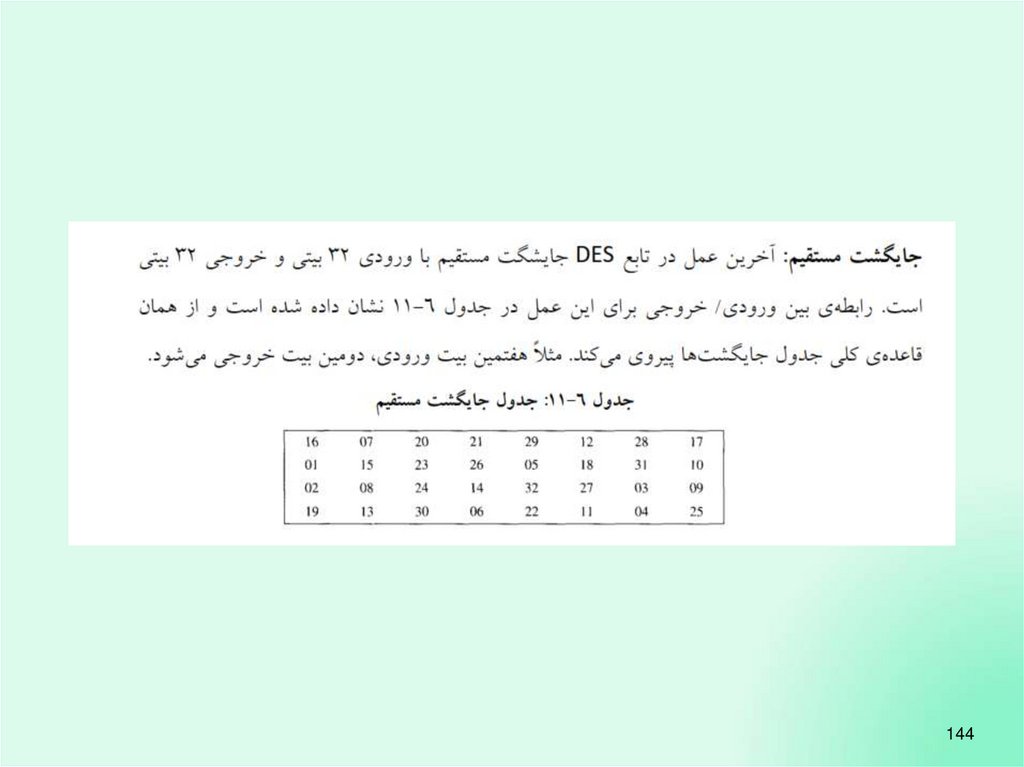
144135.
145136. Symmetric key crypto: DES
8: Network Security 8-146137.
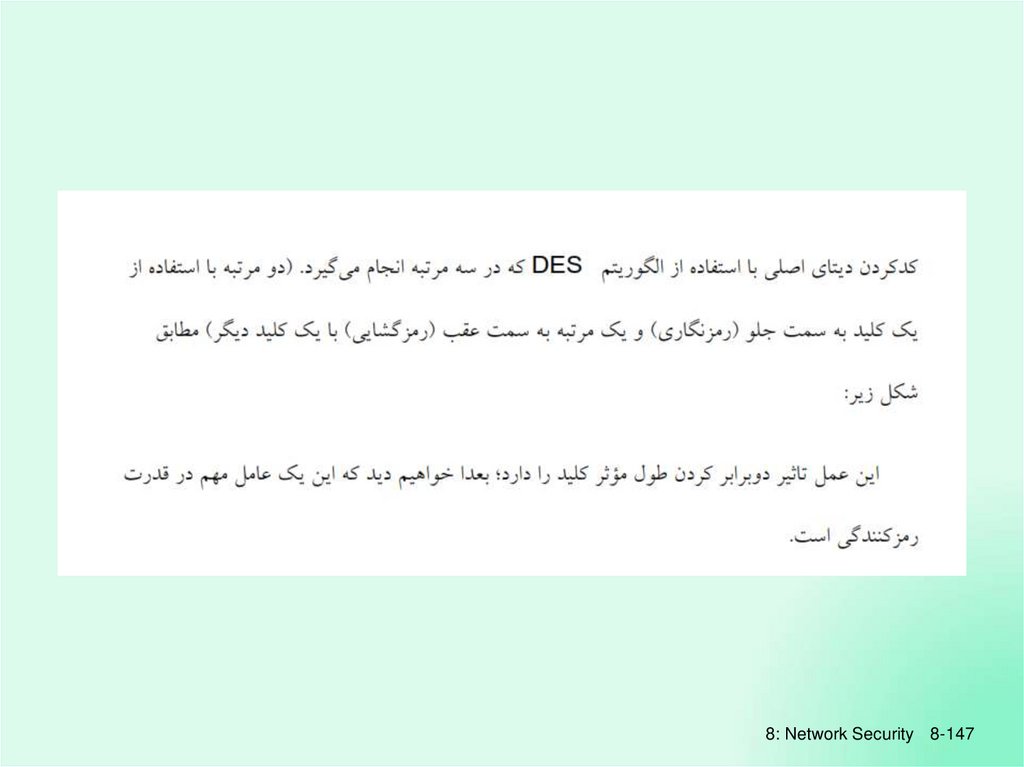
8: Network Security 8-147138.
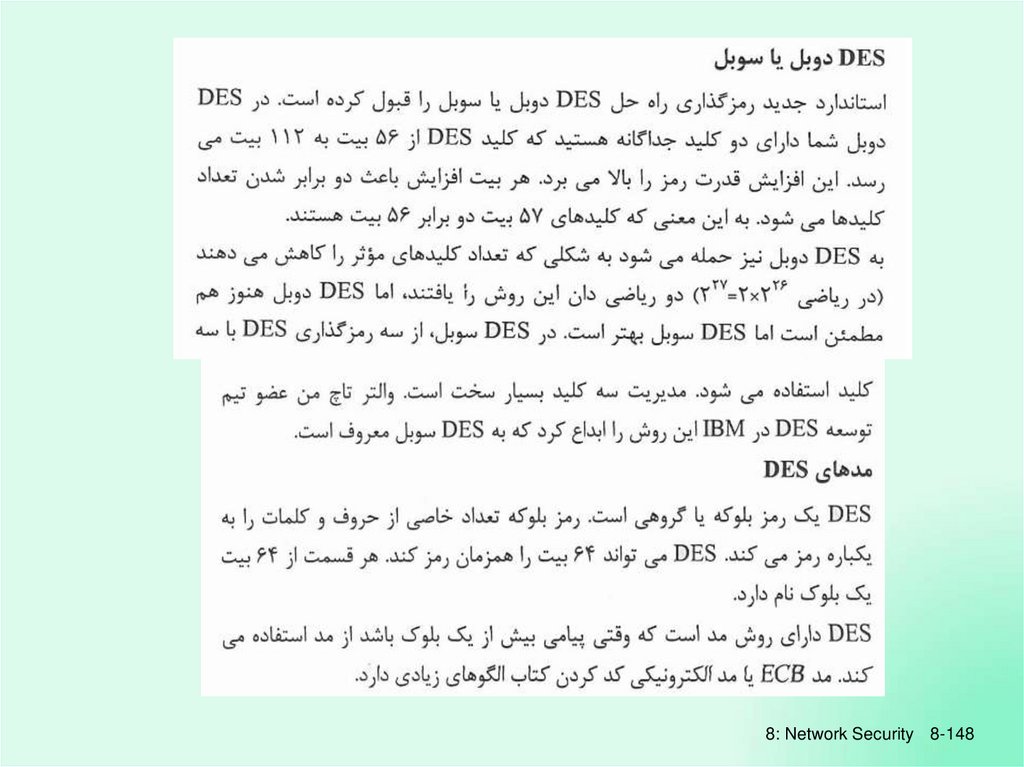
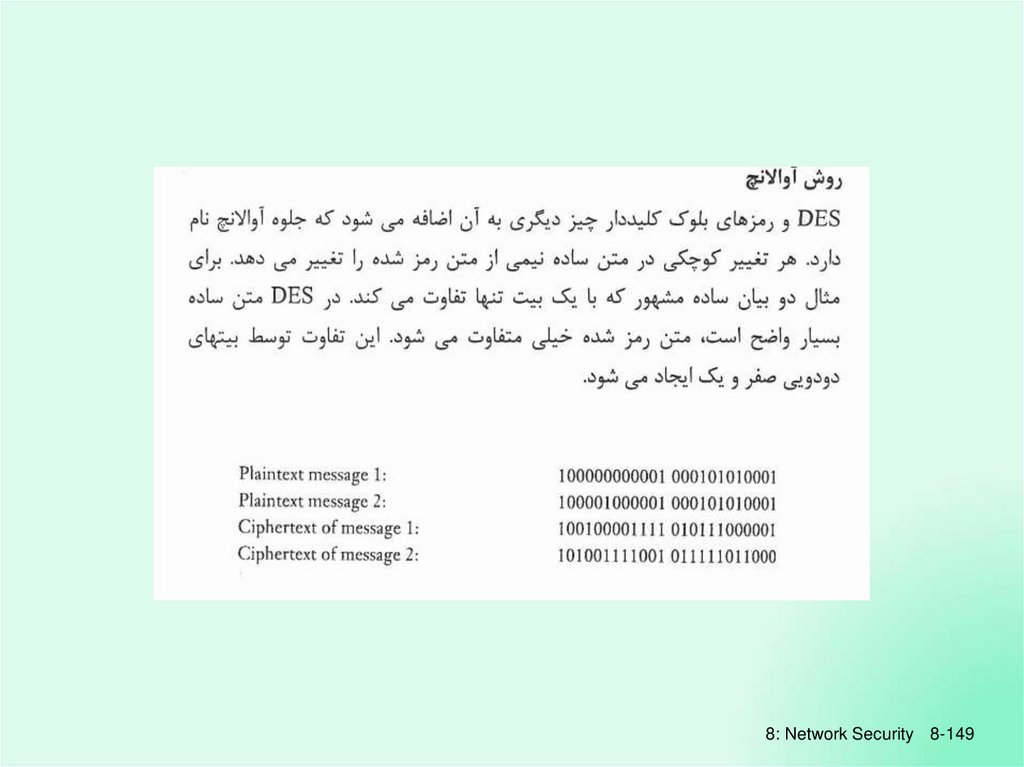
8: Network Security 8-148139.
8: Network Security 8-149140.
8: Network Security 8-150141.
8: Network Security 8-151142.
8: Network Security 8-152143.
8: Network Security 8-153144.
8: Network Security 8-154145.
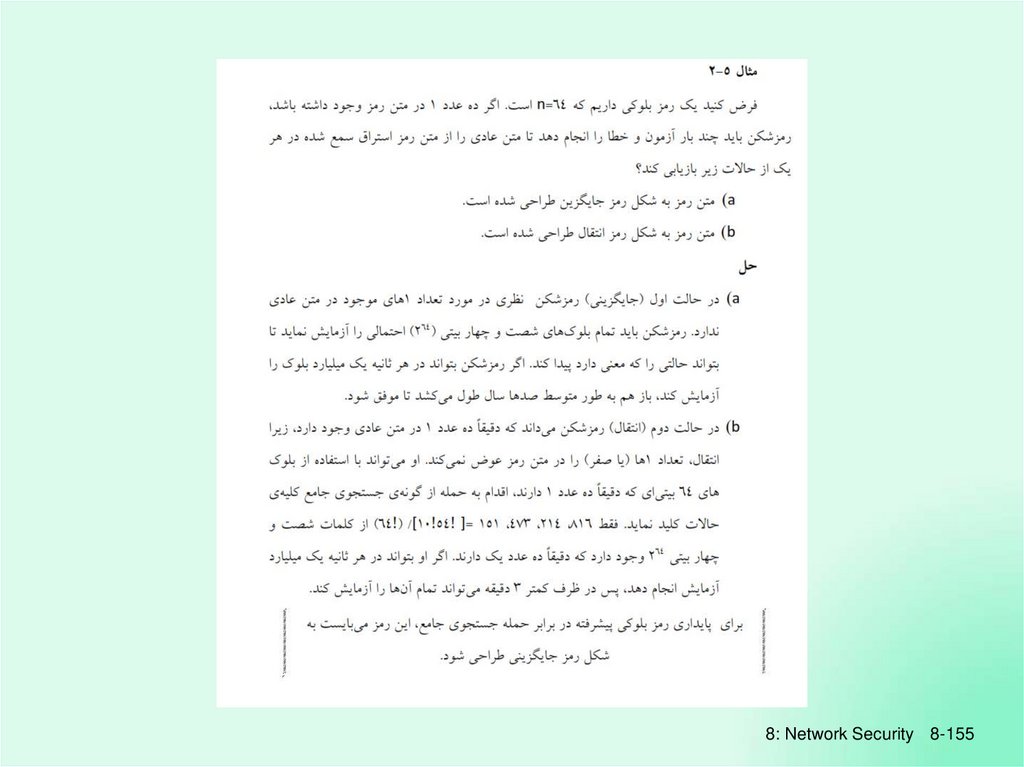
8: Network Security 8-155146.
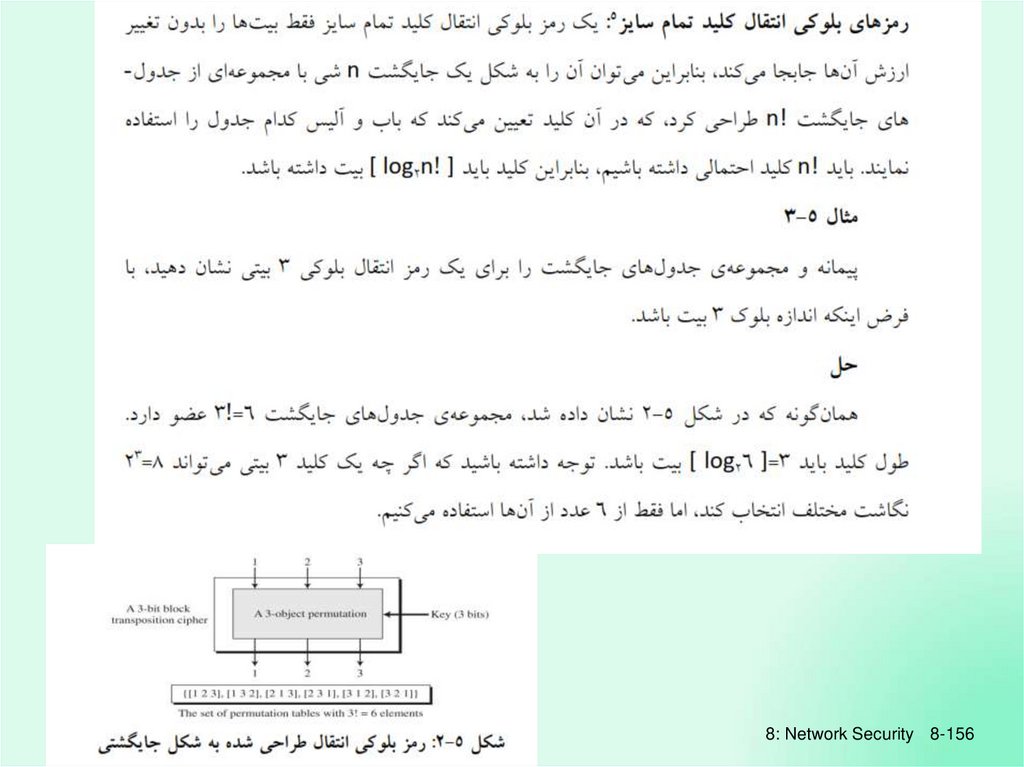
8: Network Security 8-156147.
8: Network Security 8-157148.
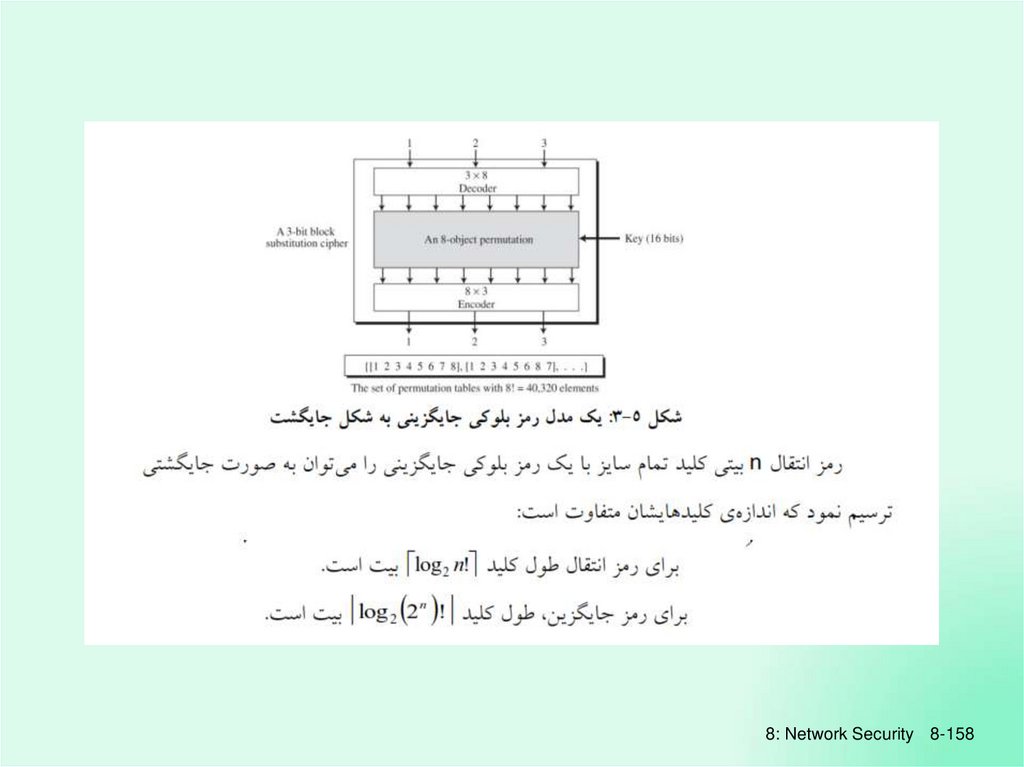
8: Network Security 8-158149.
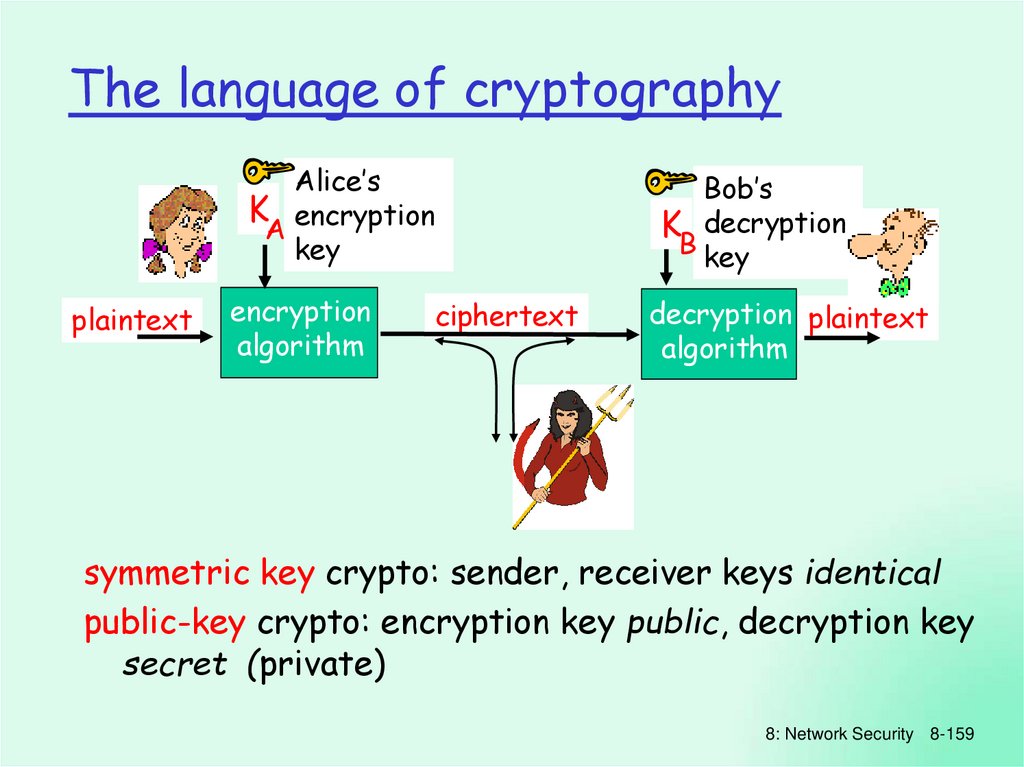
The language of cryptographyAlice’s
K encryption
A
key
plaintext
encryption
algorithm
ciphertext
Bob’s
K decryption
B key
decryption plaintext
algorithm
symmetric key crypto: sender, receiver keys identical
public-key crypto: encryption key public, decryption key
secret (private)
8: Network Security 8-159
150.
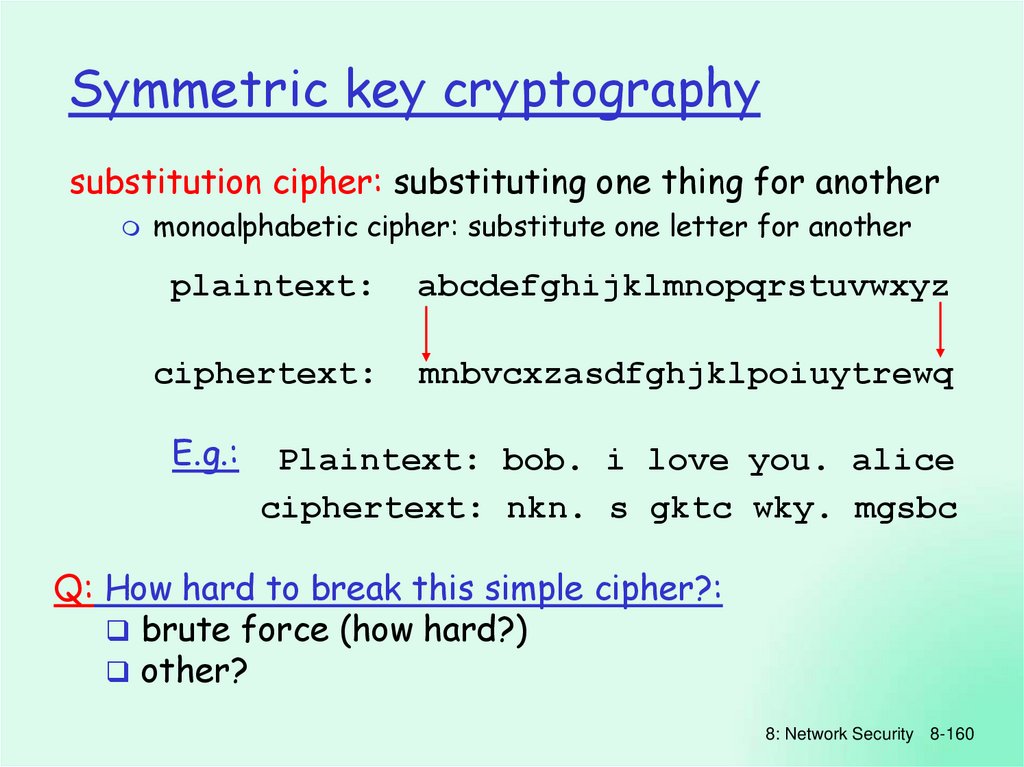
Symmetric key cryptographysubstitution cipher: substituting one thing for another
monoalphabetic cipher: substitute one letter for another
plaintext:
abcdefghijklmnopqrstuvwxyz
ciphertext:
mnbvcxzasdfghjklpoiuytrewq
E.g.:
Plaintext: bob. i love you. alice
ciphertext: nkn. s gktc wky. mgsbc
Q: How hard to break this simple cipher?:
brute force (how hard?)
other?
8: Network Security 8-160
151.
Symmetric key cryptographyKA-B
KA-B
plaintext
message, m
encryption ciphertext
algorithm
K (m)
A-B
decryption plaintext
algorithm
m = K ( KA-B(m) )
A-B
symmetric key crypto: Bob and Alice share know same
(symmetric) key: K
A-B
e.g., key is knowing substitution pattern in mono
alphabetic substitution cipher
Q: how do Bob and Alice agree on key value?
8: Network Security 8-161
152.
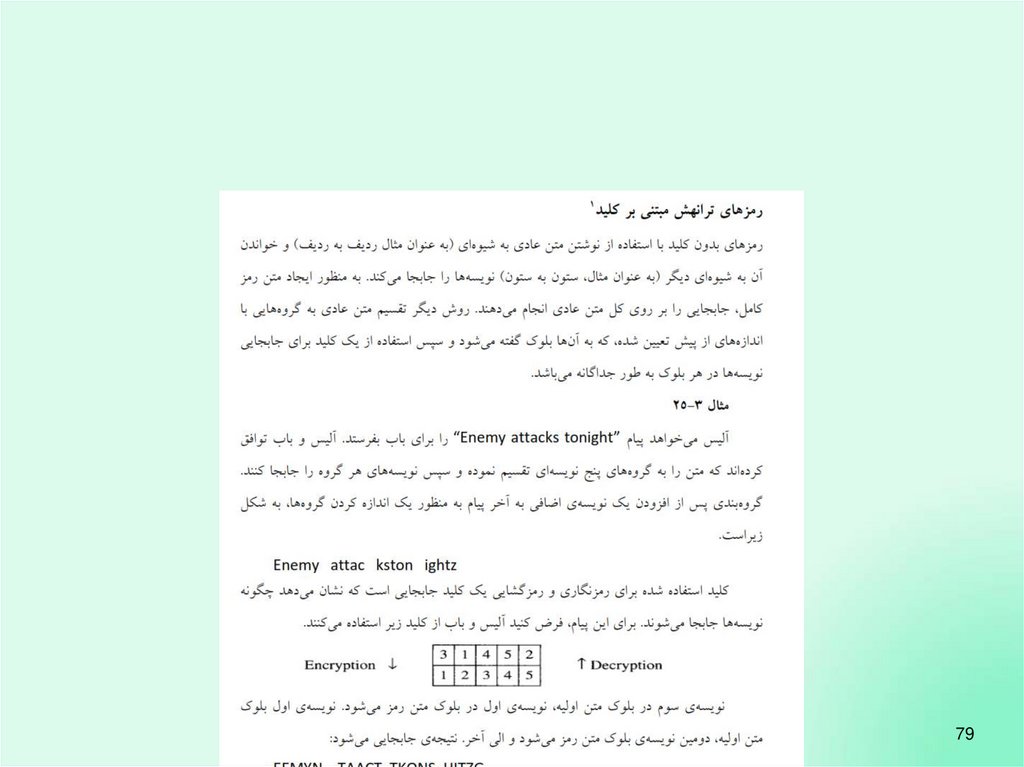
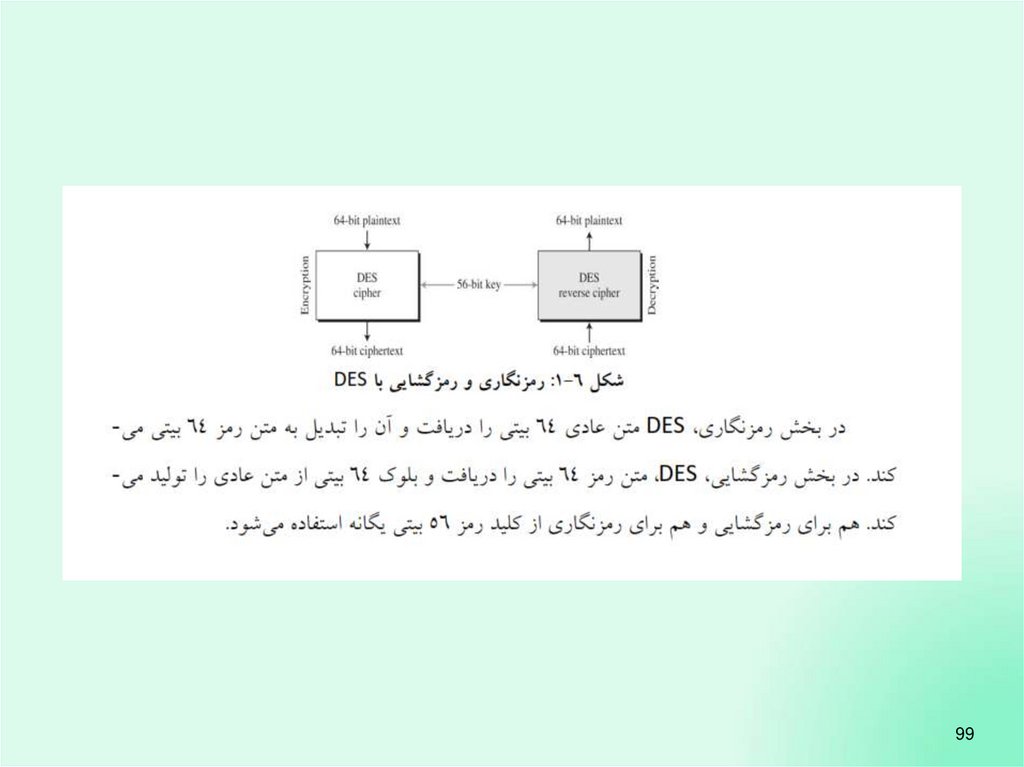
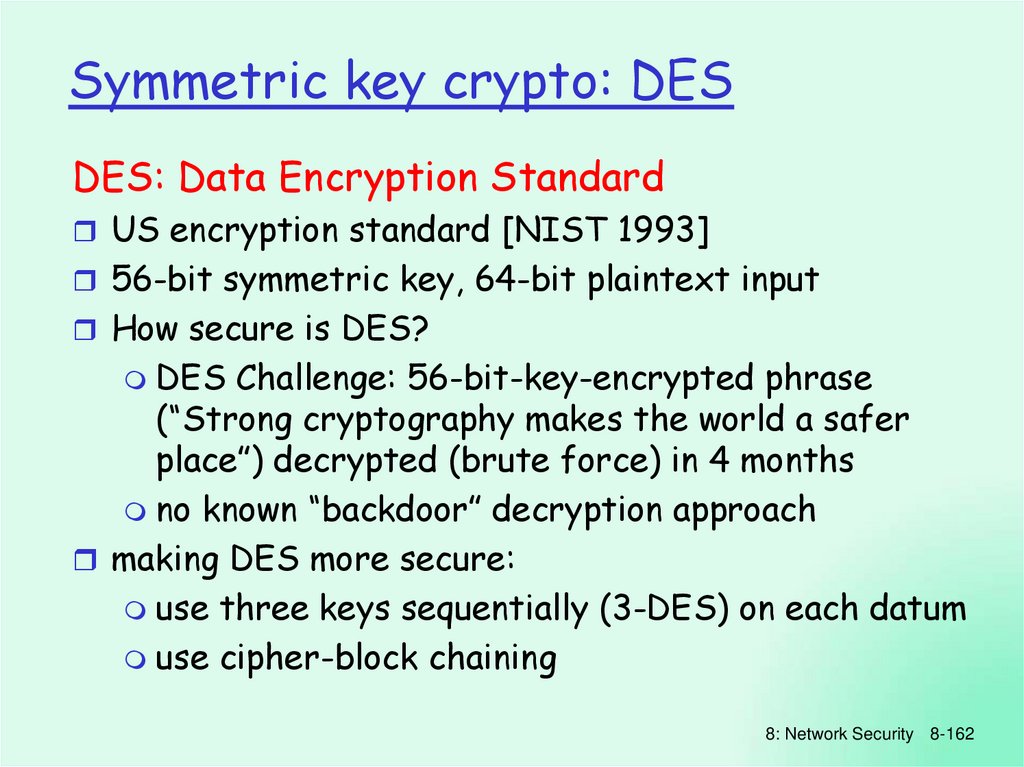
Symmetric key crypto: DESDES: Data Encryption Standard
US encryption standard [NIST 1993]
56-bit symmetric key, 64-bit plaintext input
How secure is DES?
DES Challenge: 56-bit-key-encrypted phrase
(“Strong cryptography makes the world a safer
place”) decrypted (brute force) in 4 months
no known “backdoor” decryption approach
making DES more secure:
use three keys sequentially (3-DES) on each datum
use cipher-block chaining
8: Network Security 8-162
153.
Symmetric keycrypto: DES
DES operation
initial permutation
16 identical “rounds” of
function application,
each using different
48 bits of key
final permutation
8: Network Security 8-163
154.
AES: Advanced Encryption Standardnew (Nov. 2001) symmetric-key NIST
standard, replacing DES
processes data in 128 bit blocks
128, 192, or 256 bit keys
brute force decryption (try each key)
taking 1 sec on DES, takes 149 trillion
years for AES
8: Network Security 8-164
155.
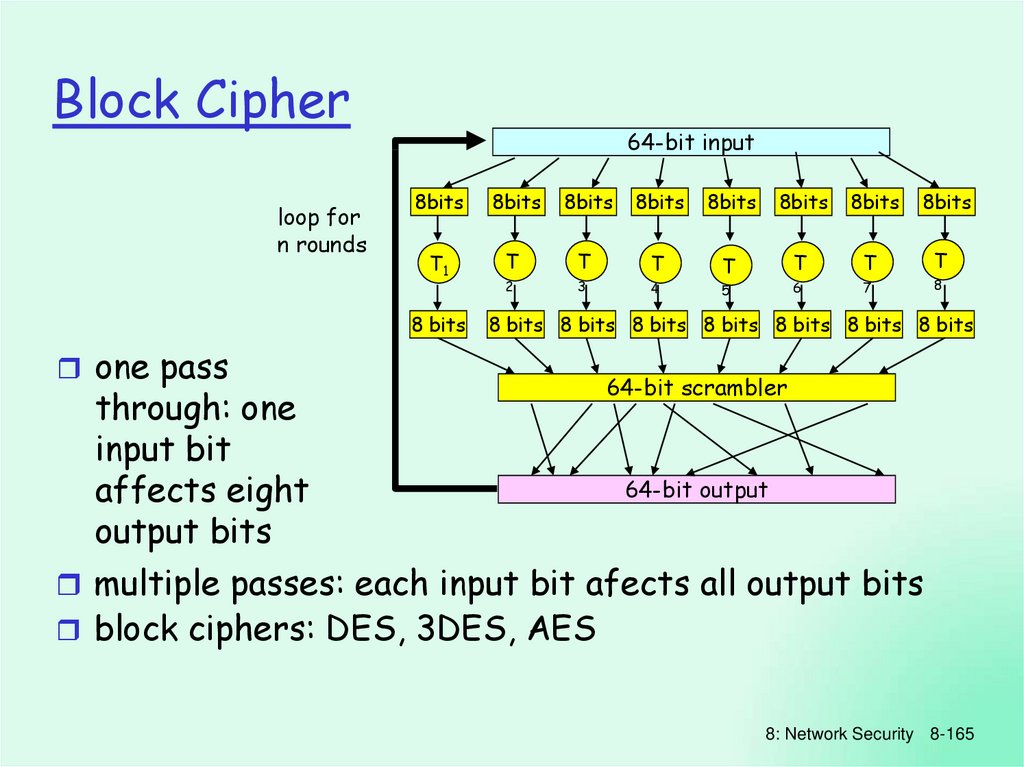
Block Cipherloop for
n rounds
64-bit input
8bits
8bits
8bits
8bits
8bits
8bits
8bits
T1
T
T
T
T
T
T
2
3
T
4
5
6
7
8
8 bits
8bits
8 bits 8 bits 8 bits 8 bits 8 bits 8 bits 8 bits
one pass
through: one
input bit
affects eight
output bits
64-bit scrambler
64-bit output
multiple passes: each input bit afects all output bits
block ciphers: DES, 3DES, AES
8: Network Security 8-165
156.
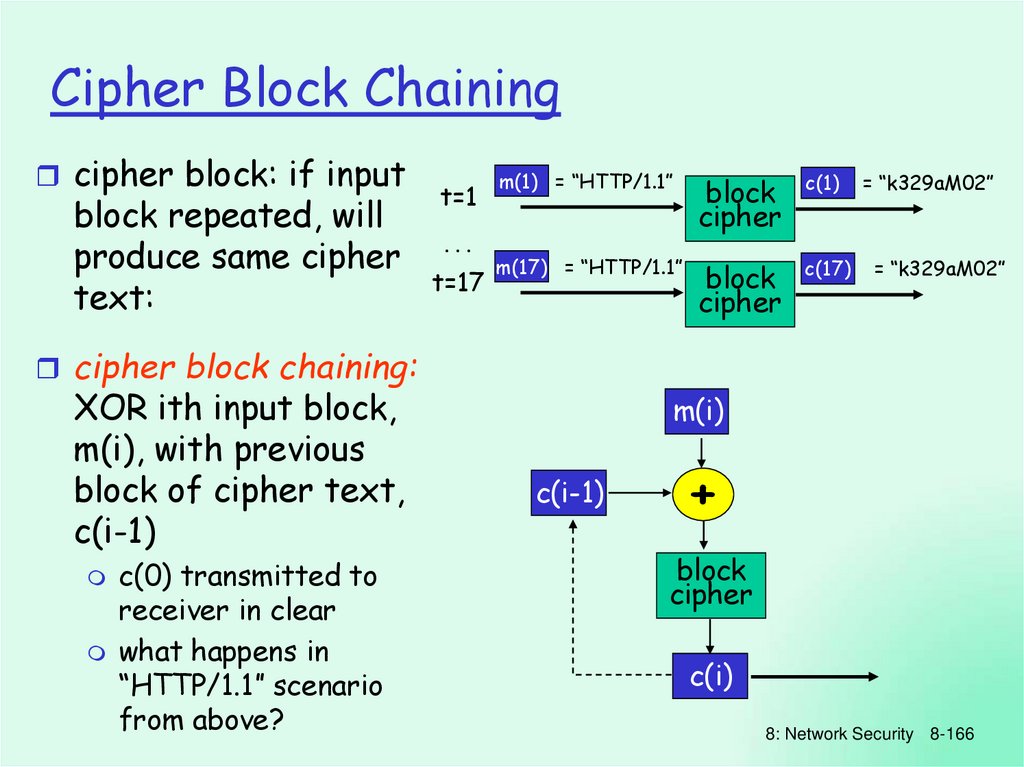
Cipher Block Chainingcipher block: if input
block repeated, will
produce same cipher
text:
t=1
…
t=17
m(1) = “HTTP/1.1”
block
cipher
c(1)
m(17) = “HTTP/1.1”
block
cipher
c(17)
= “k329aM02”
= “k329aM02”
cipher block chaining:
XOR ith input block,
m(i), with previous
block of cipher text,
c(i-1)
c(0) transmitted to
receiver in clear
what happens in
“HTTP/1.1” scenario
from above?
m(i)
c(i-1)
+
block
cipher
c(i)
8: Network Security 8-166
157.
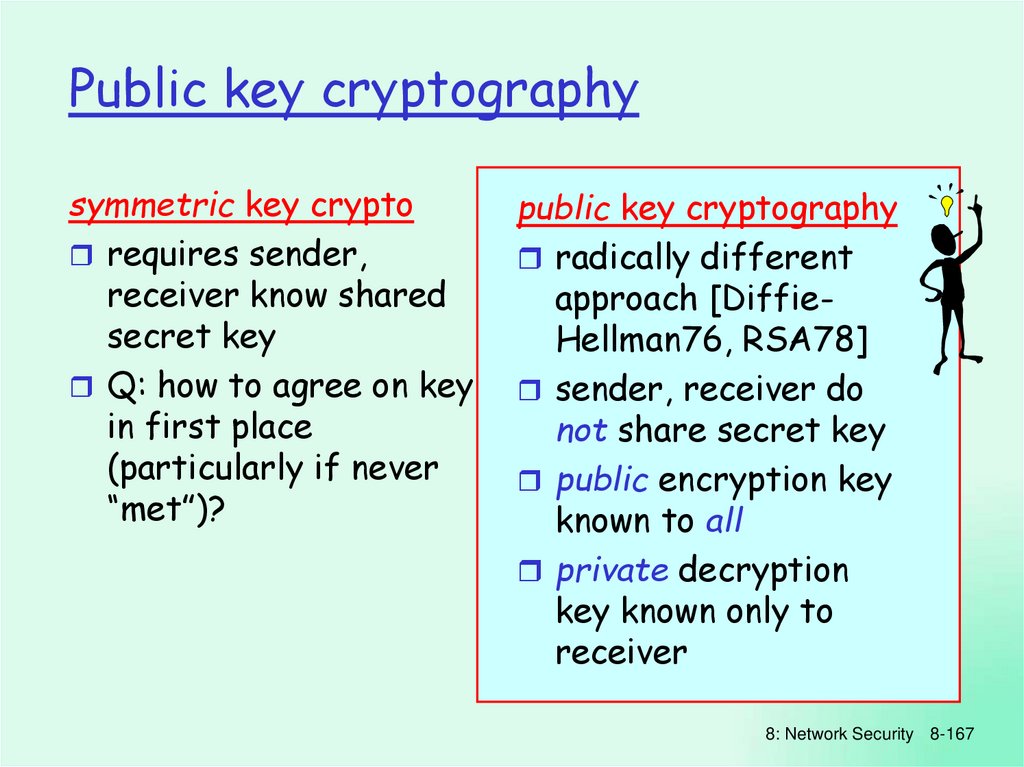
Public key cryptographysymmetric key crypto
requires sender,
receiver know shared
secret key
Q: how to agree on key
in first place
(particularly if never
“met”)?
public key cryptography
radically different
approach [DiffieHellman76, RSA78]
sender, receiver do
not share secret key
public encryption key
known to all
private decryption
key known only to
receiver
8: Network Security 8-167
158.
Public key cryptography+ Bob’s public
B key
K
K
plaintext
message, m
encryption ciphertext
algorithm
+
K (m)
B
- Bob’s private
B key
decryption plaintext
algorithm message
+
m = K B(K (m))
B
8: Network Security 8-168
159. The language of cryptography
Public key encryption algorithmsRequirements:
1
2
+
need K ( ) and K - ( ) such that
B
B
- +
K (K (m)) = m
B B
.
.
+
given public key KB , it should be
impossible to compute
private key KB
RSA: Rivest, Shamir, Adleman algorithm
8: Network Security 8-169
160. Symmetric key cryptography
RSA: Choosing keys1. Choose two large prime numbers p, q.
(e.g., 1024 bits each)
2. Compute n = pq, z = (p-1)(q-1)
3. Choose e (with e<n) that has no common factors
with z. (e, z are “relatively prime”).
4. Choose d such that ed-1 is exactly divisible by z.
(in other words: ed mod z = 1 ).
5. Public key is (n,e). Private key is (n,d).
+
KB
-
KB
8: Network Security 8-170
161. Symmetric key cryptography
RSA: Encryption, decryption0. Given (n,e) and (n,d) as computed above
1. To encrypt bit pattern, m, compute
e
e
c = m mod n (i.e., remainder when m is divided by n)
2. To decrypt received bit pattern, c, compute
d
m = c d mod n (i.e., remainder when c is divided by n)
Magic
d
m = (m e mod n) mod n
happens!
c
8: Network Security 8-171
162. Symmetric key crypto: DES
RSA example:Bob chooses p=5, q=7. Then n=35, z=24.
e=5 (so e, z relatively prime).
d=29 (so ed-1 exactly divisible by z.
encrypt:
decrypt:
letter
m
me
l
12
1524832
c
17
d
c
481968572106750915091411825223071697
c = me mod n
17
m = cd mod n letter
12
l
8: Network Security 8-172
163. Symmetric key crypto: DES
RSA: Why is thatm = (m e mod n)
d
mod n
Useful number theory result: If p,q prime and
n = pq, then:
y
y mod (p-1)(q-1)
x mod n = x
mod n
e
(m mod n) d mod n = medmod n
= m
ed mod (p-1)(q-1)
mod n
(using number theory result above)
1
= m mod n
(since we chose ed to be divisible by
(p-1)(q-1) with remainder 1 )
= m
8: Network Security 8-173
164. AES: Advanced Encryption Standard
RSA: another important propertyThe following property will be very useful later:
-
+
B
B
K (K (m))
+ = m = K (K (m))
B B
use public key
first, followed
by private key
use private key
first, followed
by public key
Result is the same!
8: Network Security 8-174
165. Block Cipher
Chapter 8 roadmap8.1 What is network security?
8.2 Principles of cryptography
8.3 Message integrity
8.4 End point authentication
8.5 Securing e-mail
8.6 Securing TCP connections: SSL
8.7 Network layer security: IPsec
8.8 Securing wireless LANs
8.9 Operational security: firewalls and IDS
8: Network Security 8-175
166. Cipher Block Chaining
Message IntegrityBob receives msg from Alice, wants to ensure:
message originally came from Alice
message not changed since sent by Alice
Cryptographic Hash:
takes input m, produces fixed length value, H(m)
e.g., as in Internet checksum
computationally infeasible to find two different
messages, x, y such that H(x) = H(y)
equivalently: given m = H(x), (x unknown), can not determine
x.
note: Internet checksum fails this requirement!
8: Network Security 8-176
167. Public key cryptography
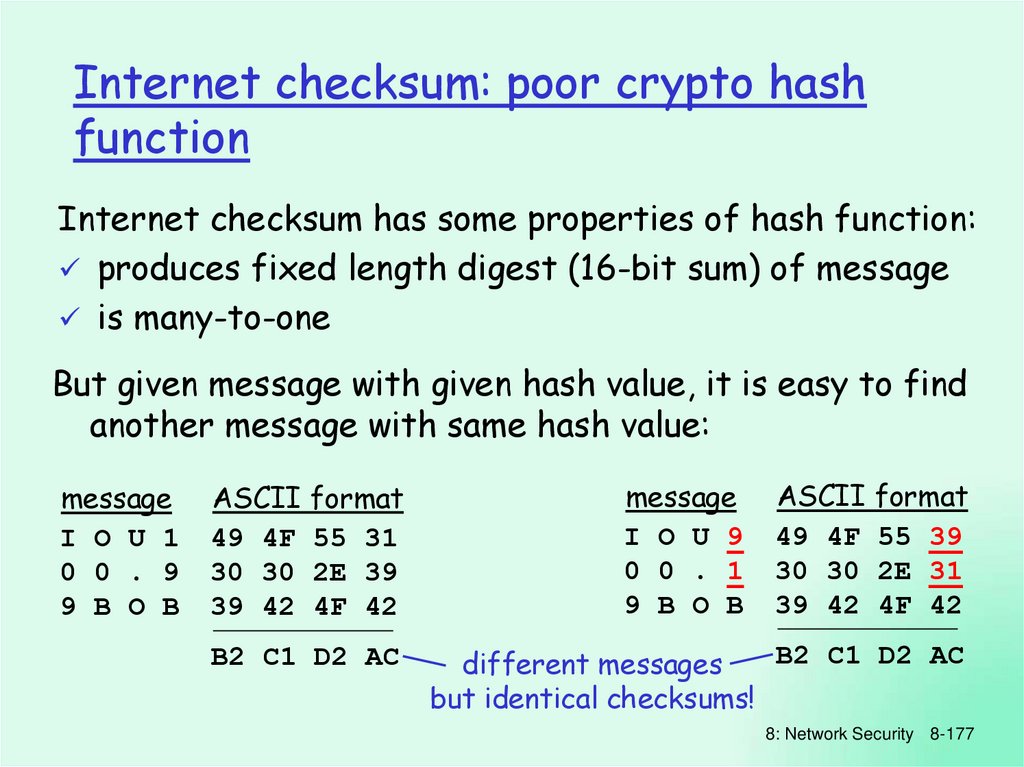
Internet checksum: poor crypto hashfunction
Internet checksum has some properties of hash function:
produces fixed length digest (16-bit sum) of message
is many-to-one
But given message with given hash value, it is easy to find
another message with same hash value:
message
I O U 1
0 0 . 9
9 B O B
ASCII format
49 4F 55 31
30 30 2E 39
39 42 4F 42
B2 C1 D2 AC
message
I O U 9
0 0 . 1
9 B O B
ASCII format
49 4F 55 39
30 30 2E 31
39 42 4F 42
B2 C1 D2 AC
different messages
but identical checksums!
8: Network Security 8-177
168. Public key cryptography
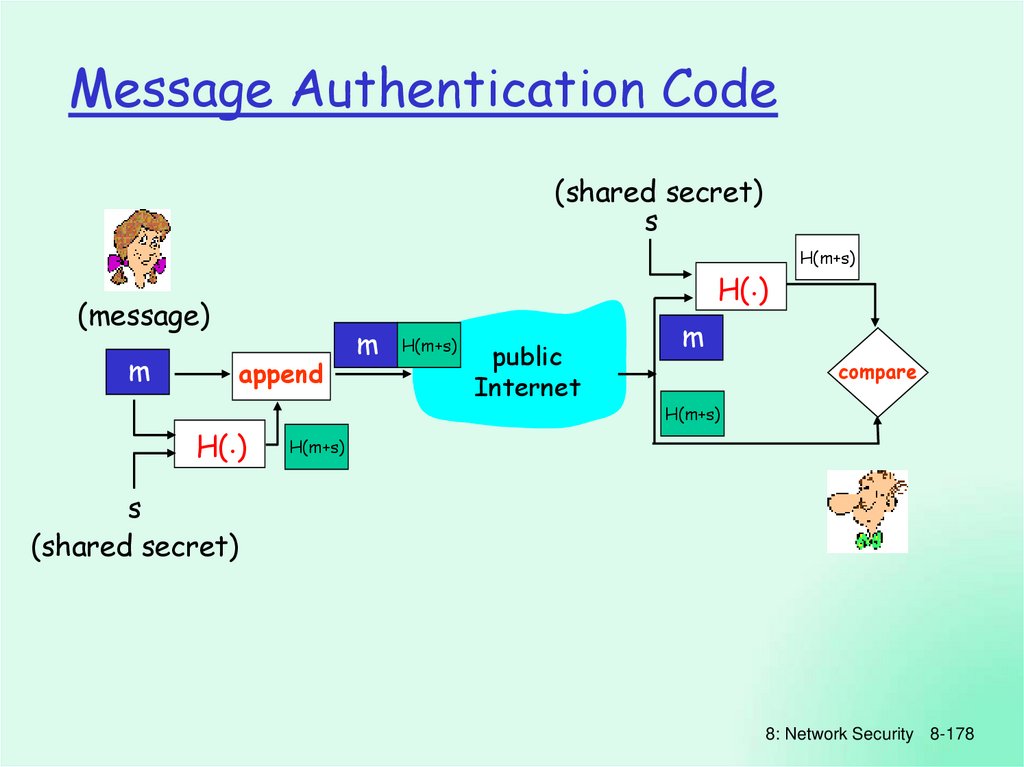
Message Authentication Code(shared secret)
s
H(.)
(message)
m
append
H(.)
m
H(m+s)
public
Internet
H(m+s)
m
compare
H(m+s)
H(m+s)
s
(shared secret)
8: Network Security 8-178
169. Public key encryption algorithms
MACs in practiceMD5 hash function widely used (RFC 1321)
computes 128-bit MAC in 4-step process.
arbitrary 128-bit string x, appears difficult to
construct msg m whose MD5 hash is equal to x
• recent (2005) attacks on MD5
SHA-1 is also used
US standard [NIST, FIPS PUB 180-1]
160-bit MAC
8: Network Security 8-179
170. RSA: Choosing keys
Digital Signaturescryptographic technique analogous to handwritten signatures.
sender (Bob) digitally signs document,
establishing he is document owner/creator.
verifiable, nonforgeable: recipient (Alice) can
prove to someone that Bob, and no one else
(including Alice), must have signed document
8: Network Security 8-180
171. RSA: Encryption, decryption
Digital Signaturessimple digital signature for message m:
Bob “signs” m by encrypting with his private key
-
KB, creating “signed” message, KB(m)
Bob’s message, m
Dear Alice
Oh, how I have missed
you. I think of you all the
time! …(blah blah blah)
Bob
K B Bob’s private
key
public key
encryption
algorithm
-
K B(m)
Bob’s message, m,
signed (encrypted)
with his private key
8: Network Security 8-181
172. RSA example:
Digital Signatures (more)-
suppose Alice receives msg m, digital signature KB(m)
Alice verifies m signed by Bob by applying Bob’s
+
-
+
-
public key KB to KB(m) then checks KB(KB(m) ) = m.
+
-
if KB(KB(m) ) = m, whoever signed m must have used
Bob’s private key.
Alice thus verifies that:
Bob signed m.
No one else signed m.
Bob signed m and not m’.
non-repudiation:
Alice can take m, and signature KB(m) to
court and prove that Bob signed m.
8: Network Security 8-182
173. RSA: Why is that
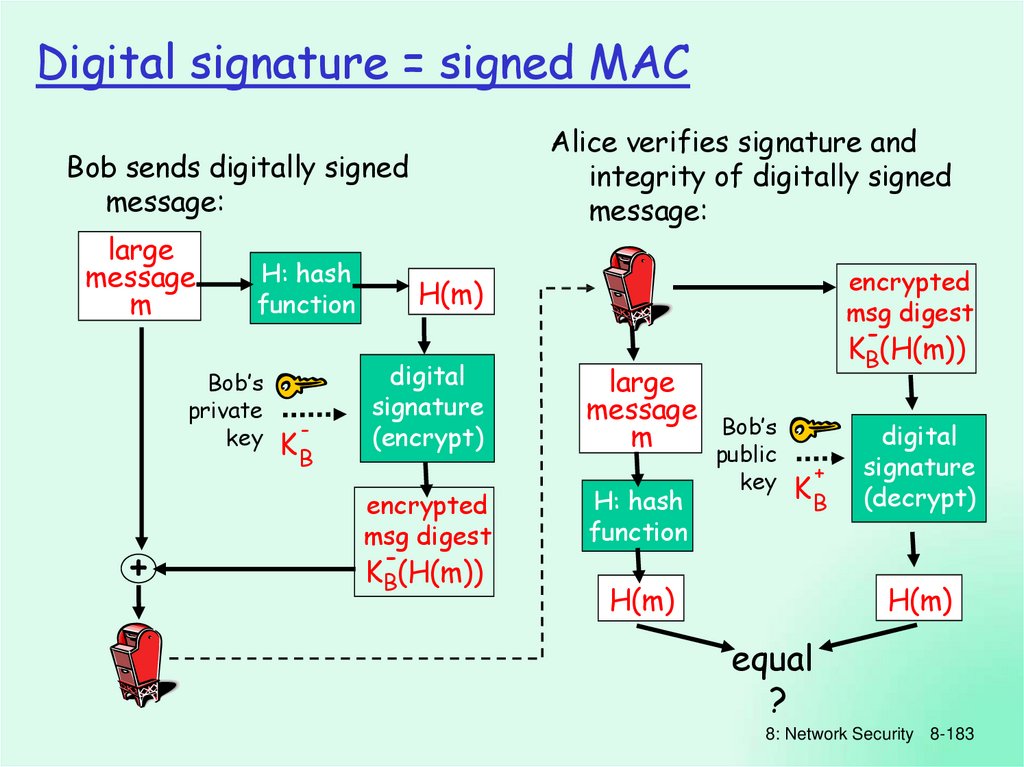
Digital signature = signed MACAlice verifies signature and
integrity of digitally signed
message:
Bob sends digitally signed
message:
large
message
m
H: hash
function
Bob’s
private
key
+
-
KB
encrypted
msg digest
H(m)
digital
signature
(encrypt)
encrypted
msg digest
KB(H(m))
large
message
m
H: hash
function
KB(H(m))
Bob’s
public
key
+
KB
digital
signature
(decrypt)
H(m)
H(m)
equal
?
8: Network Security 8-183
174. RSA: another important property
Public Key Certificationpublic key problem:
When Alice obtains Bob’s public key (from web site,
e-mail, diskette), how does she know it is Bob’s
public key, not Trudy’s?
solution:
trusted certification authority (CA)
8: Network Security 8-184
175. Chapter 8 roadmap
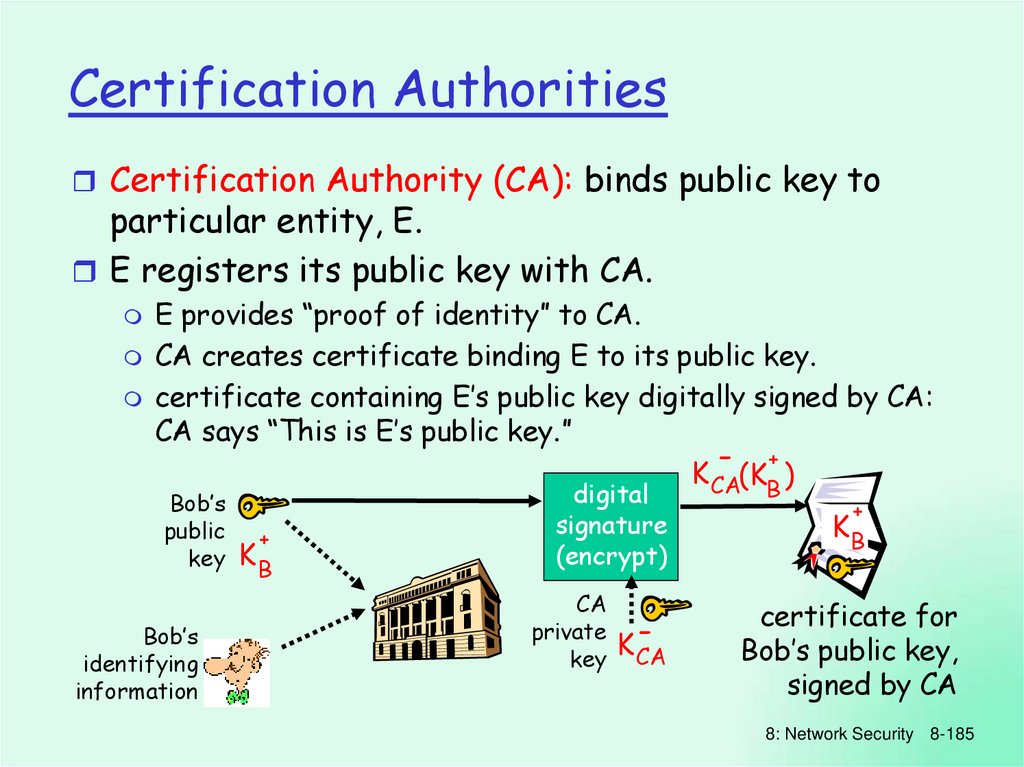
Certification AuthoritiesCertification Authority (CA): binds public key to
particular entity, E.
E registers its public key with CA.
E provides “proof of identity” to CA.
CA creates certificate binding E to its public key.
certificate containing E’s public key digitally signed by CA:
CA says “This is E’s public key.”
- +
K CA(KB )
Bob’s
public
key
Bob’s
identifying
information
+
KB
digital
signature
(encrypt)
CA
private
key
K-
CA
+
KB
certificate for
Bob’s public key,
signed by CA
8: Network Security 8-185
176. Message Integrity
Certification Authoritieswhen Alice wants Bob’s public key:
gets Bob’s certificate (Bob or elsewhere).
apply CA’s public key to Bob’s certificate, get
Bob’s public key
+
KB
-
+
K CA(KB )
digital
signature
(decrypt)
CA
public
key
Bob’s
public
+
key
KB
+
K CA
8: Network Security 8-186
177. Internet checksum: poor crypto hash function
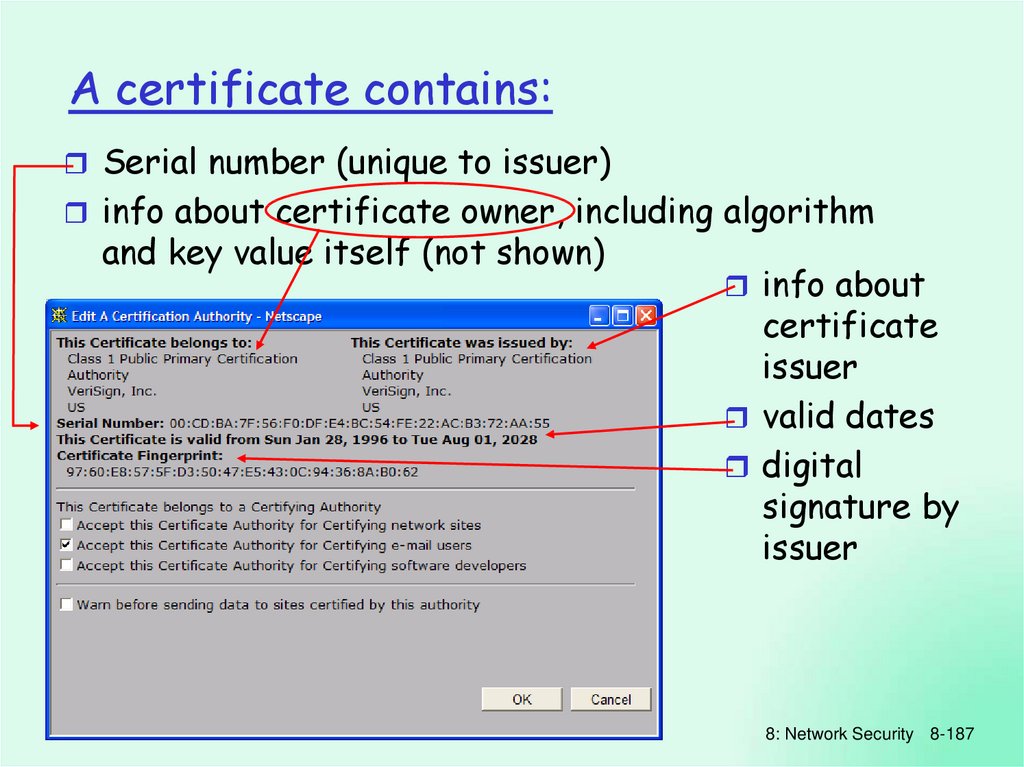
A certificate contains:Serial number (unique to issuer)
info about certificate owner, including algorithm
and key value itself (not shown)
info about
certificate
issuer
valid dates
digital
signature by
issuer
8: Network Security 8-187
178. Message Authentication Code
Chapter 8 roadmap8.1 What is network security?
8.2 Principles of cryptography
8.3 Message integrity
8.4 End point authentication
8.5 Securing e-mail
8.6 Securing TCP connections: SSL
8.7 Network layer security: IPsec
8.8 Securing wireless LANs
8.9 Operational security: firewalls and IDS
8: Network Security 8-188
179. MACs in practice
AuthenticationGoal: Bob wants Alice to “prove” her identity
to him
Protocol ap1.0: Alice says “I am Alice”
“I am Alice”
Failure scenario??
8: Network Security 8-189
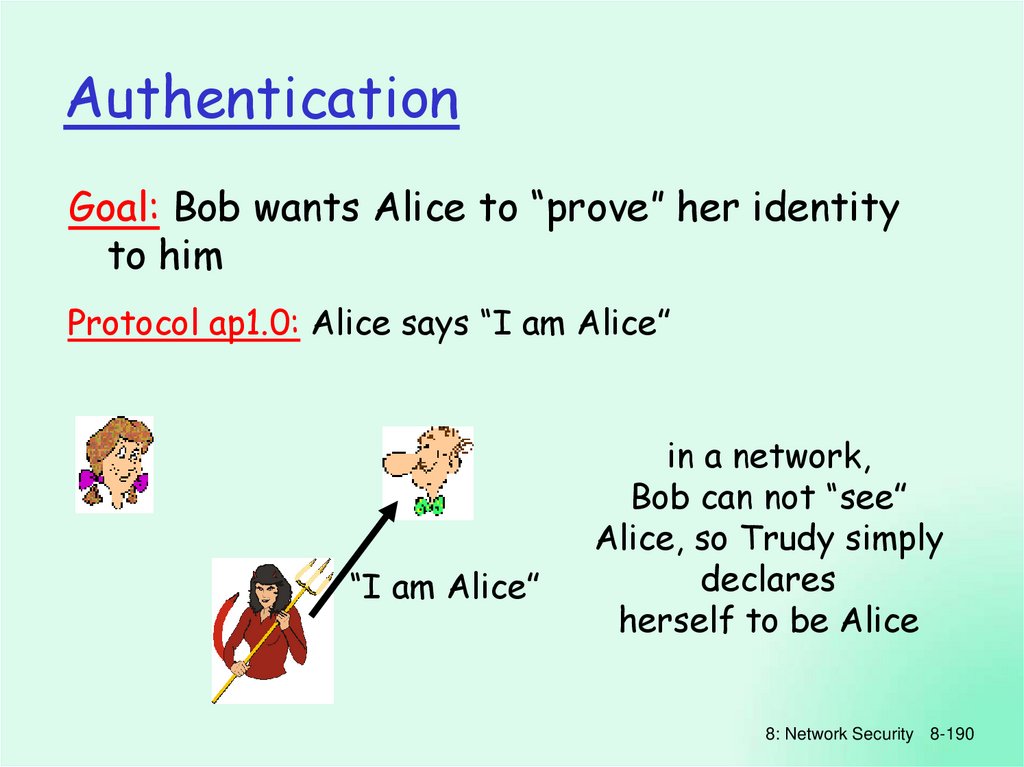
180. Digital Signatures
AuthenticationGoal: Bob wants Alice to “prove” her identity
to him
Protocol ap1.0: Alice says “I am Alice”
“I am Alice”
in a network,
Bob can not “see”
Alice, so Trudy simply
declares
herself to be Alice
8: Network Security 8-190
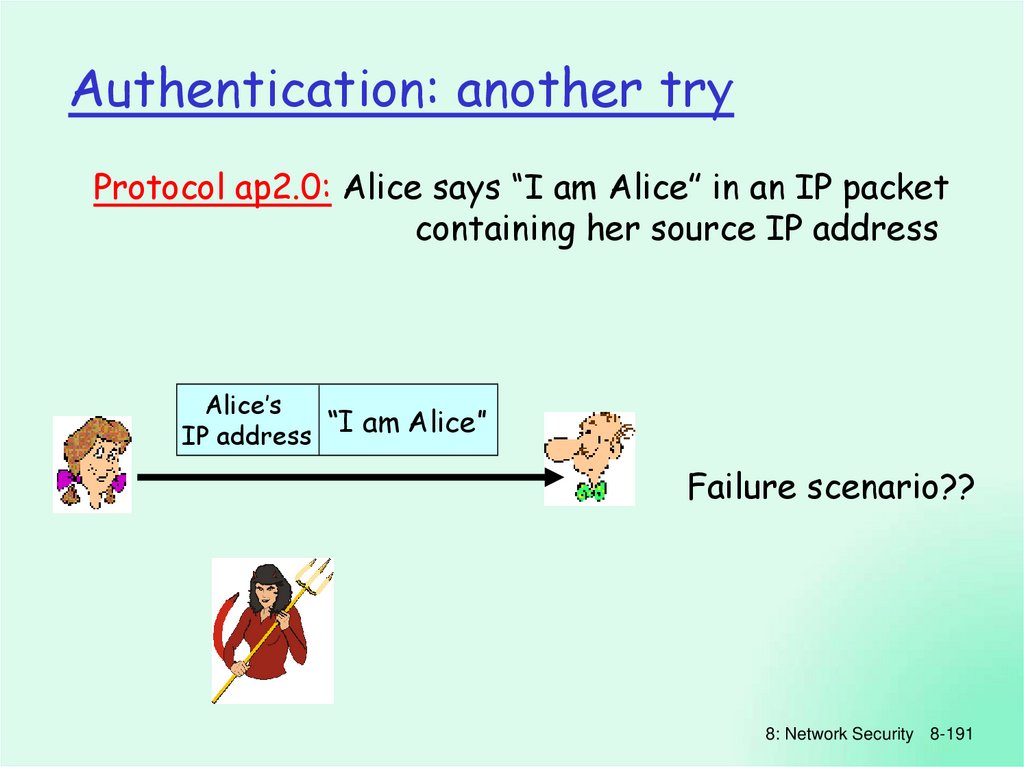
181. Digital Signatures
Authentication: another tryProtocol ap2.0: Alice says “I am Alice” in an IP packet
containing her source IP address
Alice’s
“I am Alice”
IP address
Failure scenario??
8: Network Security 8-191
182. Digital Signatures (more)
Authentication: another tryProtocol ap2.0: Alice says “I am Alice” in an IP packet
containing her source IP address
Alice’s
IP address
Trudy can create
a packet
“spoofing”
“I am Alice”
Alice’s address
8: Network Security 8-192
183.
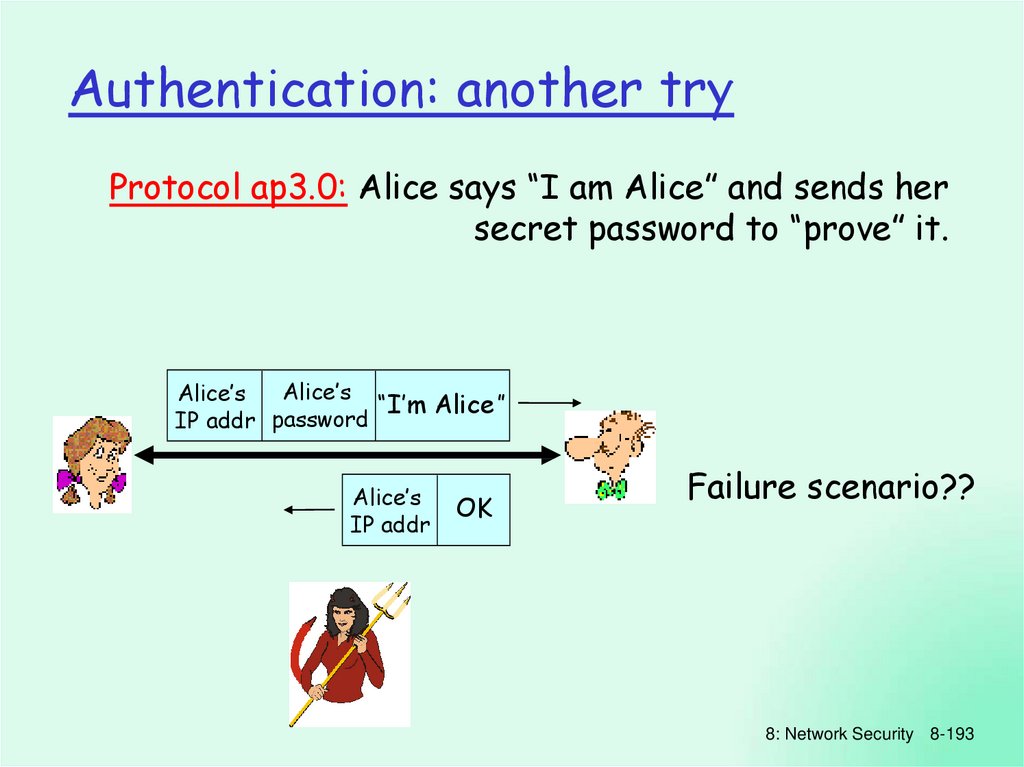
Authentication: another tryProtocol ap3.0: Alice says “I am Alice” and sends her
secret password to “prove” it.
Alice’s
Alice’s
“I’m Alice”
IP addr password
Alice’s
IP addr
OK
Failure scenario??
8: Network Security 8-193
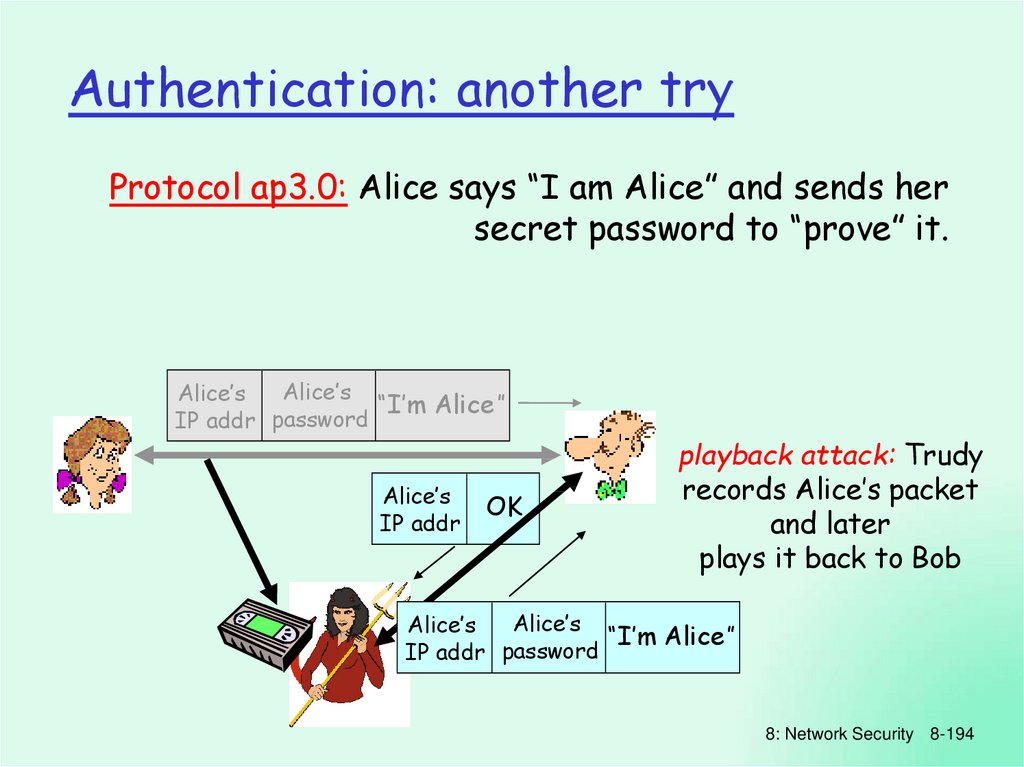
184. Public Key Certification
Authentication: another tryProtocol ap3.0: Alice says “I am Alice” and sends her
secret password to “prove” it.
Alice’s
Alice’s
“I’m Alice”
IP addr password
Alice’s
IP addr
OK
playback attack: Trudy
records Alice’s packet
and later
plays it back to Bob
Alice’s
Alice’s
“I’m Alice”
IP addr password
8: Network Security 8-194
185. Certification Authorities
Authentication: yet another tryProtocol ap3.1: Alice says “I am Alice” and sends her
encrypted secret password to “prove” it.
Alice’s encrypted
“I’m Alice”
IP addr password
Alice’s
IP addr
OK
Failure scenario??
8: Network Security 8-195
186. Certification Authorities
Authentication: another tryProtocol ap3.1: Alice says “I am Alice” and sends her
encrypted secret password to “prove” it.
Alice’s encrypted
“I’m Alice”
IP addr password
Alice’s
IP addr
OK
record
and
playback
still works!
Alice’s encrypted
“I’m Alice”
IP addr password
8: Network Security 8-196
187. A certificate contains:
Authentication: yet another tryGoal: avoid playback attack
Nonce: number (R) used only once –in-a-lifetime
ap4.0: to prove Alice “live”, Bob sends Alice nonce, R. Alice
must return R, encrypted with shared secret key
“I am Alice”
R
KA-B(R)
Failures, drawbacks?
Alice is live, and
only Alice knows
key to encrypt
nonce, so it must
be Alice!
8: Network Security 8-197
188. Chapter 8 roadmap
Authentication: ap5.0ap4.0 requires shared symmetric key
can we authenticate using public key techniques?
ap5.0: use nonce, public key cryptography
“I am Alice”
R
Bob computes
+ -
-
K A (R)
“send me your public key”
+
KA
KA(KA (R)) = R
and knows only Alice
could have the private
key, that encrypted R
such that
+ K (K (R)) = R
A A
8: Network Security 8-198
189. Authentication
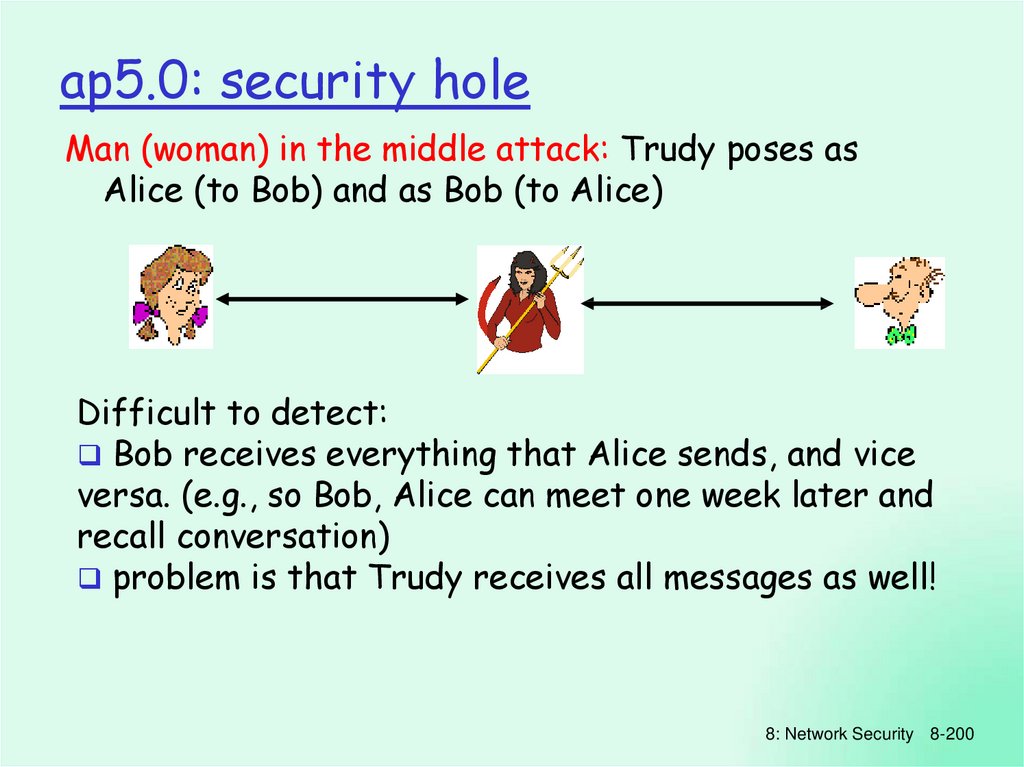
ap5.0: security holeMan (woman) in the middle attack: Trudy poses as
Alice (to Bob) and as Bob (to Alice)
I am Alice
R
I am Alice
R
K (R)
T
K (R)
A
Send me your public key
+
K
T
Send me your public key
+
K
A
- +
m = K (K (m))
A A
+
K (m)
A
Trudy gets
- +
m = K (K (m))
T Alice
sends T
m to
+
K (m)
T
encrypted with
Alice’s public key
8: Network Security 8-199
190. Authentication
ap5.0: security holeMan (woman) in the middle attack: Trudy poses as
Alice (to Bob) and as Bob (to Alice)
Difficult to detect:
Bob receives everything that Alice sends, and vice
versa. (e.g., so Bob, Alice can meet one week later and
recall conversation)
problem is that Trudy receives all messages as well!
8: Network Security 8-200
191. Authentication: another try
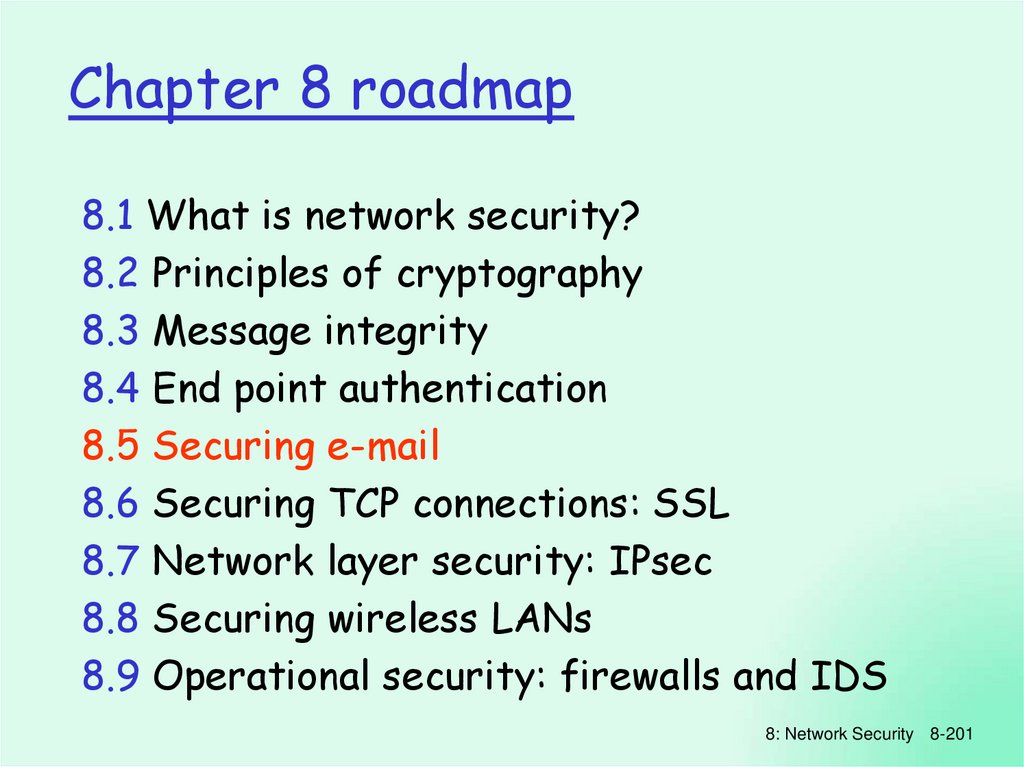
Chapter 8 roadmap8.1 What is network security?
8.2 Principles of cryptography
8.3 Message integrity
8.4 End point authentication
8.5 Securing e-mail
8.6 Securing TCP connections: SSL
8.7 Network layer security: IPsec
8.8 Securing wireless LANs
8.9 Operational security: firewalls and IDS
8: Network Security 8-201
192. Authentication: another try
Secure e-mailAlice wants to send confidential e-mail, m, to Bob.
KS
m
K (.)
S
+
KS
+
.
K B( )
+
KS(m )
KS(m )
+
KB(KS )
.
KS( )
-
Internet
+
KB(KS )
KB
m
KS
-
.
K B( )
-
KB
Alice:
generates random symmetric private key, KS.
encrypts message with KS (for efficiency)
also encrypts KS with Bob’s public key.
sends both KS(m) and KB(KS) to Bob.
8: Network Security 8-202
193. Authentication: another try
Secure e-mailAlice wants to send confidential e-mail, m, to Bob.
KS
m
K (.)
S
+
KS
+
.
K B( )
+
KS(m )
KS(m )
+
KB(KS )
.
KS( )
-
Internet
+
KB(KS )
KB
m
KS
-
.
K B( )
-
KB
Bob:
uses his private key to decrypt and recover KS
uses KS to decrypt KS(m) to recover m
8: Network Security 8-203
194. Authentication: another try
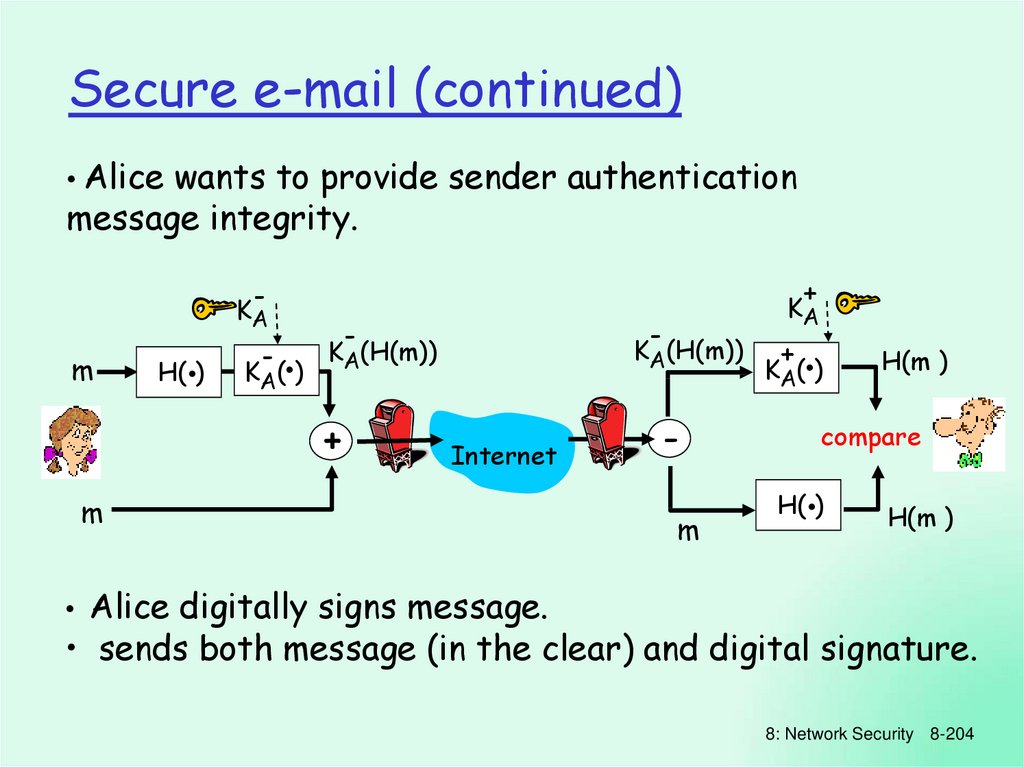
Secure e-mail (continued)• Alice wants to provide sender authentication
message integrity.
+
-
KA
m
H(.)
-
.
KA( )
-
-
KA(H(m))
KA(H(m))
+
KA
Internet
m
+
.
KA( )
m
H(m )
compare
.
H( )
H(m )
• Alice digitally signs message.
• sends both message (in the clear) and digital signature.
8: Network Security 8-204
195. Authentication: yet another try
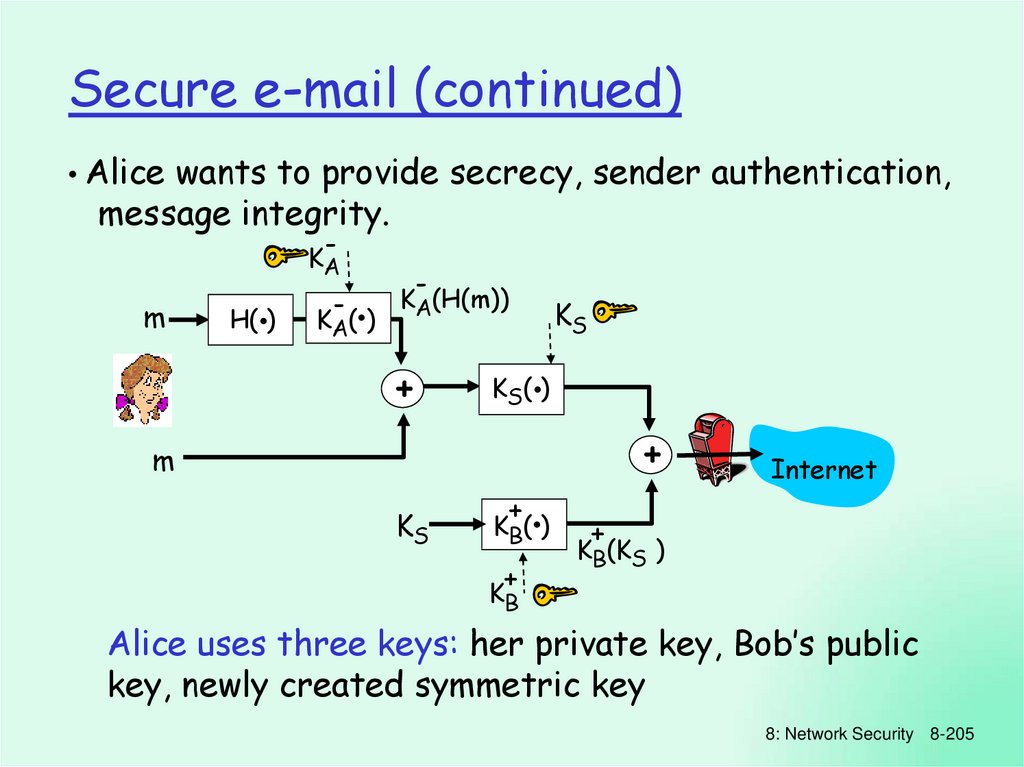
Secure e-mail (continued)• Alice wants to provide secrecy, sender authentication,
message integrity.
-
KA
m
.
H( )
-
.
KA( )
-
KA(H(m))
+
KS
.
KS( )
+
m
KS
+
.
K B( )
+
Internet
+
KB(KS )
KB
Alice uses three keys: her private key, Bob’s public
key, newly created symmetric key
8: Network Security 8-205
196. Authentication: another try
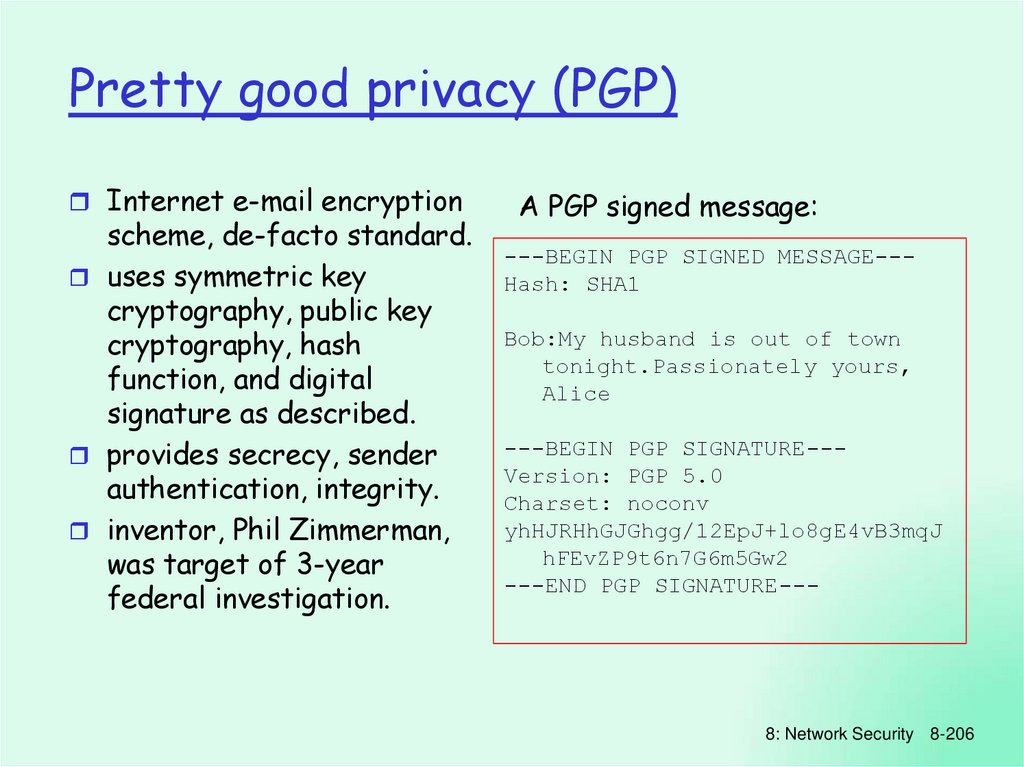
Pretty good privacy (PGP)Internet e-mail encryption
scheme, de-facto standard.
uses symmetric key
cryptography, public key
cryptography, hash
function, and digital
signature as described.
provides secrecy, sender
authentication, integrity.
inventor, Phil Zimmerman,
was target of 3-year
federal investigation.
A PGP signed message:
---BEGIN PGP SIGNED MESSAGE--Hash: SHA1
Bob:My husband is out of town
tonight.Passionately yours,
Alice
---BEGIN PGP SIGNATURE--Version: PGP 5.0
Charset: noconv
yhHJRHhGJGhgg/12EpJ+lo8gE4vB3mqJ
hFEvZP9t6n7G6m5Gw2
---END PGP SIGNATURE---
8: Network Security 8-206
197. Authentication: yet another try
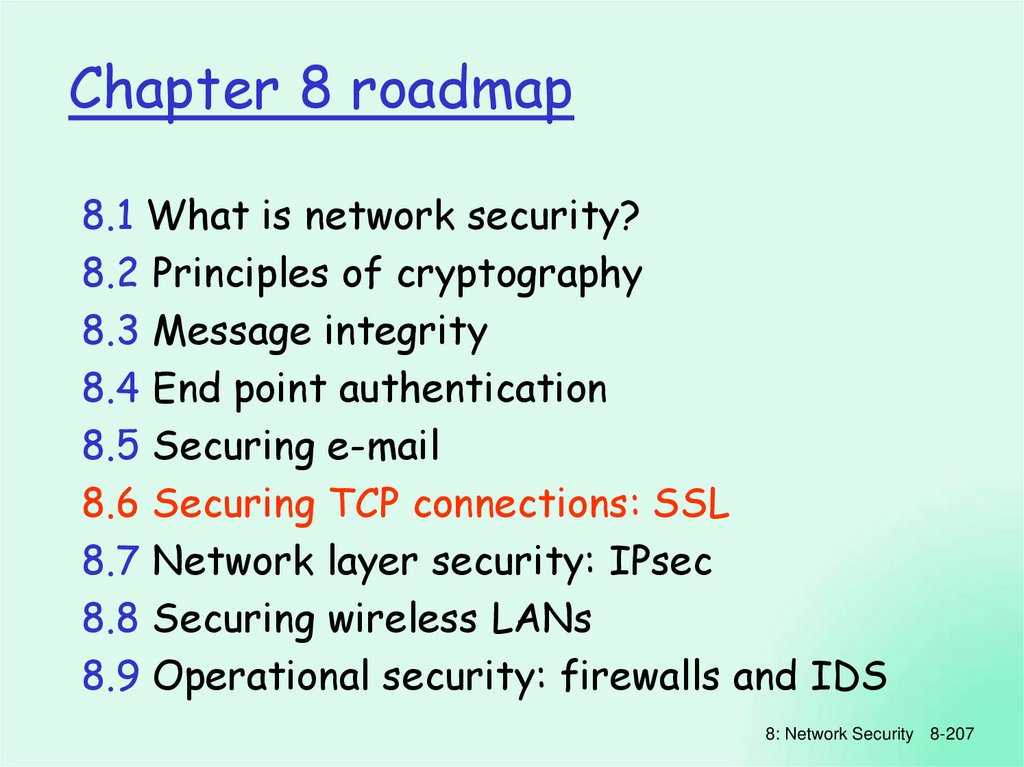
Chapter 8 roadmap8.1 What is network security?
8.2 Principles of cryptography
8.3 Message integrity
8.4 End point authentication
8.5 Securing e-mail
8.6 Securing TCP connections: SSL
8.7 Network layer security: IPsec
8.8 Securing wireless LANs
8.9 Operational security: firewalls and IDS
8: Network Security 8-207
198. Authentication: ap5.0
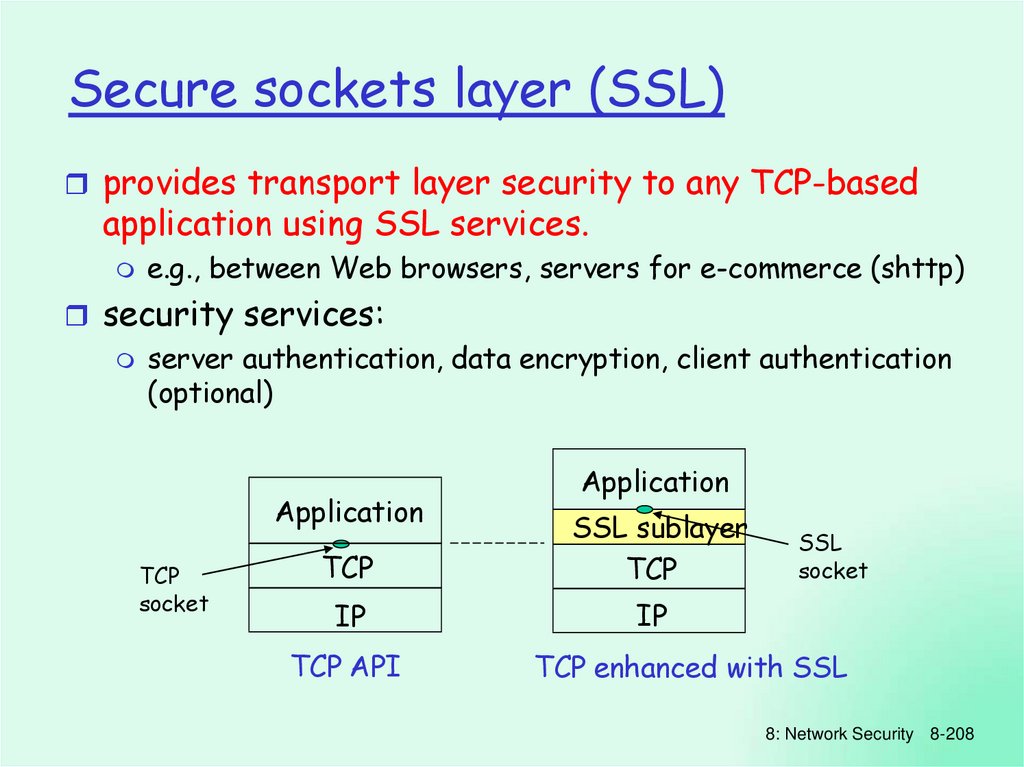
Secure sockets layer (SSL)provides transport layer security to any TCP-based
application using SSL services.
e.g., between Web browsers, servers for e-commerce (shttp)
security services:
server authentication, data encryption, client authentication
(optional)
Application
TCP
socket
Application
TCP
SSL sublayer
TCP
IP
IP
TCP API
SSL
socket
TCP enhanced with SSL
8: Network Security 8-208
199. ap5.0: security hole
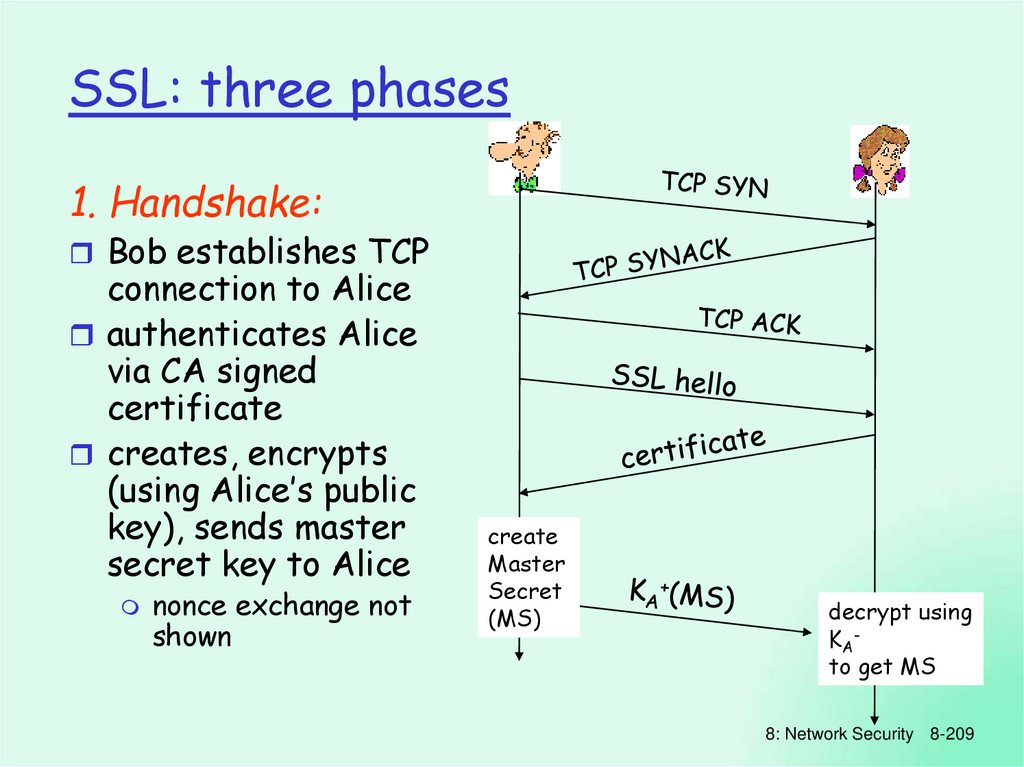
SSL: three phases1. Handshake:
Bob establishes TCP
connection to Alice
authenticates Alice
via CA signed
certificate
creates, encrypts
(using Alice’s public
key), sends master
secret key to Alice
nonce exchange not
shown
create
Master
Secret
(MS)
decrypt using
KAto get MS
8: Network Security 8-209
200. ap5.0: security hole
SSL: three phases2. Key Derivation:
Alice, Bob use shared secret (MS) to generate 4
keys:
EB: Bob->Alice data encryption key
EA: Alice->Bob data encryption key
MB: Bob->Alice MAC key
MA: Alice->Bob MAC key
encryption and MAC algorithms negotiable between
Bob, Alice
why 4 keys?
8: Network Security 8-210
201. Chapter 8 roadmap
SSL: three phases3. Data transfer
TCP byte stream
block n bytes together
b1b2b3 … bn
d
.
MB
H( )
d
H(d)
.
H( )
SSL record
format
Type Ver Len
d
H(d)
d
H(d)
EB
SSL
seq. #
compute
MAC
encrypt d,
MAC, SSL
seq. #
unencrypted encrypted using EB
8: Network Security
8-211
202. Secure e-mail
Chapter 8 roadmap8.1 What is network security?
8.2 Principles of cryptography
8.3 Message integrity
8.4 End point authentication
8.5 Securing e-mail
8.6 Securing TCP connections: SSL
8.7 Network layer security: IPsec
8.8 Securing wireless LANs
8.9 Operational security: firewalls and IDS
8: Network Security 8-212
203. Secure e-mail
IPsec: Network Layer Securitynetwork-layer secrecy:
sending host encrypts the
data in IP datagram
TCP and UDP segments;
ICMP and SNMP
messages.
network-layer authentication
destination host can
authenticate source IP
address
two principal protocols:
authentication header
(AH) protocol
encapsulation security
payload (ESP) protocol
for both AH and ESP, source,
destination handshake:
create network-layer
logical channel called a
security association (SA)
each SA unidirectional.
uniquely determined by:
security protocol (AH or
ESP)
source IP address
32-bit connection ID
8: Network Security 8-213
204. Secure e-mail (continued)
Authentication Header (AH) Protocolprovides source
authentication, data
integrity, no
confidentiality
AH header inserted
between IP header,
data field.
protocol field: 51
intermediate routers
process datagrams as
usual
IP header
AH header
AH header includes:
connection identifier
authentication data:
source- signed message
digest calculated over
original IP datagram.
next header field:
specifies type of data
(e.g., TCP, UDP, ICMP)
data (e.g., TCP, UDP segment)
8: Network Security 8-214
205. Secure e-mail (continued)
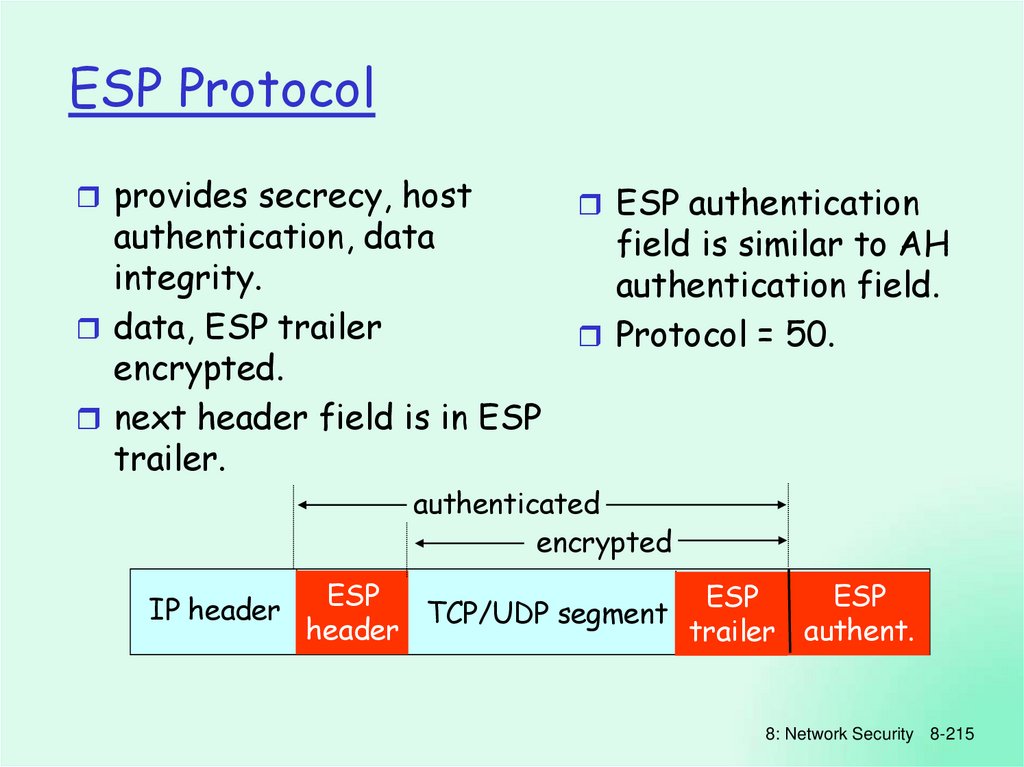
ESP Protocolprovides secrecy, host
authentication, data
integrity.
data, ESP trailer
encrypted.
next header field is in ESP
trailer.
ESP authentication
field is similar to AH
authentication field.
Protocol = 50.
authenticated
encrypted
IP header
ESP
ESP
ESP
TCP/UDP segment
header
trailer authent.
8: Network Security 8-215
206. Pretty good privacy (PGP)
Chapter 8 roadmap8.1 What is network security?
8.2 Principles of cryptography
8.3 Message integrity
8.4 End point authentication
8.5 Securing e-mail
8.6 Securing TCP connections: SSL
8.7 Network layer security: IPsec
8.8 Securing wireless LANs
8.9 Operational security: firewalls and IDS
8: Network Security 8-216
207. Chapter 8 roadmap
IEEE 802.11 securitywar-driving: drive around Bay area, see what 802.11
networks available?
More than 9000 accessible from public roadways
85% use no encryption/authentication
packet-sniffing and various attacks easy!
securing 802.11
encryption, authentication
first attempt at 802.11 security: Wired Equivalent
Privacy (WEP): a failure
current attempt: 802.11i
8: Network Security 8-217
208. Secure sockets layer (SSL)
Wired Equivalent Privacy (WEP):authentication as in protocol ap4.0
host requests authentication from access point
access point sends 128 bit nonce
host encrypts nonce using shared symmetric key
access point decrypts nonce, authenticates host
no key distribution mechanism
authentication: knowing the shared key is enough
8: Network Security 8-218
209. SSL: three phases
WEP data encryptionhost/AP share 40 bit symmetric key (semi-permanent)
host appends 24-bit initialization vector (IV) to
create 64-bit key
IV
64 bit key used to generate stream of keys, ki
IV
ki used to encrypt ith byte, di, in frame:
ci = di XOR kiIV
IV and encrypted bytes, ci sent in frame
8: Network Security 8-219
210. SSL: three phases
802.11 WEP encryptionIV
(per frame)
KS: 40-bit
secret
symmetric
key
plaintext
frame data
plus CRC
key sequence generator
( for given KS, IV)
k1IV k2IV k3IV … kNIV kN+1IV… kN+1IV
d1
d2
d3 …
dN
CRC1 … CRC4
c1
c2
c3 …
cN
cN+1 … cN+4
802.11
IV
header
WEP-encrypted data
plus CRC
Figure 7.8-new1:
802.11encryption
WEP protocol
Sender-side
WEP
8: Network Security 8-220
211. SSL: three phases
Breaking 802.11 WEP encryptionsecurity hole:
24-bit IV, one IV per frame, -> IV’s eventually reused
IV transmitted in plaintext -> IV reuse detected
attack:
Trudy causes Alice to encrypt known plaintext d1 d2
d3 d4 …
IV
Trudy sees: ci = di XOR ki
Trudy knows ci di, so can compute kiIV
IV
IV
IV
Trudy knows encrypting key sequence k1 k2 k3 …
Next time IV is used, Trudy can decrypt!
8: Network Security 8-221
212. Chapter 8 roadmap
802.11i: improved securitynumerous (stronger) forms of encryption
possible
provides key distribution
uses authentication server separate from
access point
8: Network Security 8-222
213. IPsec: Network Layer Security
802.11i: four phases of operationSTA:
client station
AP: access point
AS:
Authentication
server
wired
network
1 Discovery of
security capabilities
2 STA and AS mutually authenticate, together
generate Master Key (MK). AP servers as “pass through”
3 STA derives
Pairwise Master
Key (PMK)
4 STA, AP use PMK to derive
Temporal Key (TK) used for message
encryption, integrity
3 AS derives
same PMK,
sends to AP
8: Network Security 8-223
214. Authentication Header (AH) Protocol
EAP: extensible authentication protocolEAP: end-end client (mobile) to authentication
server protocol
EAP sent over separate “links”
mobile-to-AP (EAP over LAN)
AP to authentication server (RADIUS over UDP)
wired
network
EAP TLS
EAP
EAP over LAN (EAPoL)
IEEE 802.11
RADIUS
UDP/IP
8: Network Security 8-224
215. ESP Protocol
Chapter 8 roadmap8.1 What is network security?
8.2 Principles of cryptography
8.3 Message integrity
8.4 End point authentication
8.5 Securing e-mail
8.6 Securing TCP connections: SSL
8.7 Network layer security: IPsec
8.8 Securing wireless LANs
8.9 Operational security: firewalls and IDS
8: Network Security 8-225
216. Chapter 8 roadmap
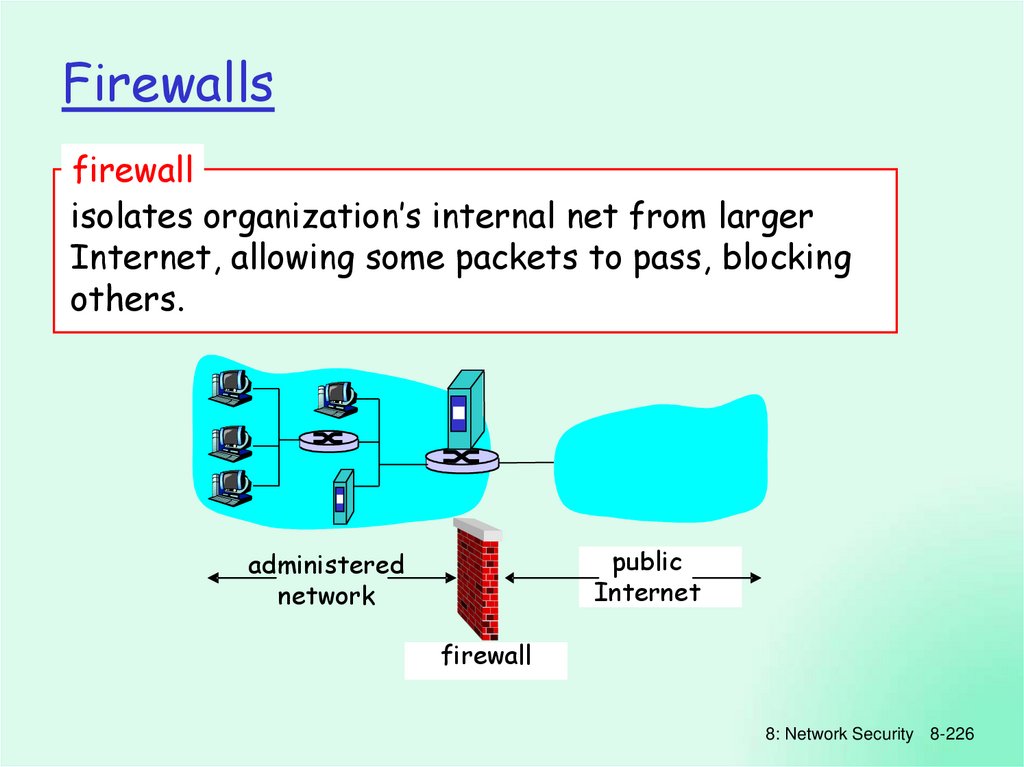
Firewallsfirewall
isolates organization’s internal net from larger
Internet, allowing some packets to pass, blocking
others.
public
Internet
administered
network
firewall
8: Network Security 8-226
217. IEEE 802.11 security
Firewalls: Whyprevent denial of service attacks:
SYN flooding: attacker establishes many bogus TCP
connections, no resources left for “real” connections
prevent illegal modification/access of internal data.
e.g., attacker replaces CIA’s homepage with
something else
allow only authorized access to inside network (set of
authenticated users/hosts)
three types of firewalls:
stateless packet filters
stateful packet filters
application gateways
8: Network Security 8-227
218. Wired Equivalent Privacy (WEP):
Stateless packet filteringShould arriving
packet be allowed
in? Departing packet
let out?
internal network connected to Internet via
router firewall
router filters packet-by-packet, decision to
forward/drop packet based on:
source IP address, destination IP address
TCP/UDP source and destination port numbers
ICMP message type
TCP SYN and ACK bits
8: Network Security 8-228
219. WEP data encryption
Stateless packet filtering: exampleexample 1: block incoming and outgoing
datagrams with IP protocol field = 17 and with
either source or dest port = 23.
all incoming, outgoing UDP flows and telnet
connections are blocked.
example 2: Block inbound TCP segments with
ACK=0.
prevents external clients from making TCP
connections with internal clients, but allows
internal clients to connect to outside.
8: Network Security 8-229
220. 802.11 WEP encryption
Stateless packet filtering: more examplesPolicy
Firewall Setting
No outside Web access.
Drop all outgoing packets to any IP
address, port 80
No incoming TCP connections,
except those for institution’s
public Web server only.
Drop all incoming TCP SYN packets to
any IP except 130.207.244.203, port
80
Prevent Web-radios from eating
up the available bandwidth.
Drop all incoming UDP packets - except
DNS and router broadcasts.
Prevent your network from being
used for a smurf DoS attack.
Drop all ICMP packets going to a
“broadcast” address (eg
130.207.255.255).
Prevent your network from being
tracerouted
Drop all outgoing ICMP TTL expired
traffic
8: Network Security 8-230
221. Breaking 802.11 WEP encryption
Access Control ListsACL: table of rules, applied top to bottom to
incoming packets: (action, condition) pairs
action
source
address
dest
address
protocol
source
port
dest
port
allow
222.22/16
outside of
222.22/16
TCP
> 1023
80
allow
outside of
222.22/16
TCP
80
> 1023
ACK
allow
222.22/16
UDP
> 1023
53
---
allow
outside of
222.22/16
222.22/16
UDP
53
> 1023
----
deny
all
all
all
all
all
all
222.22/16
outside of
222.22/16
flag
bit
any
8: Network Security 8-231
222. 802.11i: improved security
Stateful packet filteringstateless packet filter: heavy handed tool
admits packets that “make no sense,” e.g., dest port =
80, ACK bit set, even though no TCP connection
established:
source
address
dest
address
outside of
222.22/16
222.22/16
action
allow
protocol
source
port
dest
port
flag
bit
TCP
80
> 1023
ACK
stateful packet filter: track status of every TCP
connection
track connection setup (SYN), teardown (FIN): can
determine whether incoming, outgoing packets “makes sense”
timeout inactive connections at firewall: no longer admit
packets
8: Network Security 8-232
223. 802.11i: four phases of operation
Stateful packet filteringACL augmented to indicate need to check
connection state table before admitting packet
action
source
address
dest
address
proto
source
port
dest
port
allow
222.22/16
outside of
222.22/16
TCP
> 1023
80
allow
outside of
222.22/16
TCP
80
> 1023
ACK
allow
222.22/16
UDP
> 1023
53
---
allow
outside of
222.22/16
222.22/16
deny
all
all
222.22/16
outside of
222.22/16
flag
bit
check
conxion
any
UDP
53
> 1023
----
all
all
all
all
x
x
8: Network Security 8-233
224. EAP: extensible authentication protocol
Application gatewaysfilters packets on
application data as well
as on IP/TCP/UDP fields.
example: allow select
internal users to telnet
outside.
host-to-gateway
telnet session
application
gateway
gateway-to-remote
host telnet session
router and filter
1. require all telnet users to telnet through gateway.
2. for authorized users, gateway sets up telnet connection to
dest host. Gateway relays data between 2 connections
3. router filter blocks all telnet connections not originating
from gateway.
8: Network Security 8-234
225. Chapter 8 roadmap
Limitations of firewalls and gatewaysIP spoofing: router
can’t know if data
“really” comes from
claimed source
if multiple app’s. need
special treatment, each
has own app. gateway.
client software must
know how to contact
gateway.
filters often use all or
nothing policy for UDP.
tradeoff: degree of
communication with
outside world, level of
security
many highly protected
sites still suffer from
attacks.
e.g., must set IP address
of proxy in Web
browser
8: Network Security 8-235
226. Firewalls
Intrusion detection systemspacket filtering:
operates on TCP/IP headers only
no correlation check among sessions
IDS: intrusion detection system
deep packet inspection: look at packet contents
(e.g., check character strings in packet against
database of known virus, attack strings)
examine correlation among multiple packets
• port scanning
• network mapping
• DoS attack
8: Network Security 8-236
227. Firewalls: Why
Intrusion detection systemsmultiple IDSs: different types of checking
at different locations
application
gateway
firewall
Internet
internal
network
IDS
sensors
Web
server
FTP
server
DNS
server
demilitarized
zone
8: Network Security 8-237
228. Stateless packet filtering
Network Security (summary)Basic techniques…...
cryptography
(symmetric and public)
message integrity
end-point authentication
…. used in many different security scenarios
secure email
secure transport (SSL)
IP sec
802.11
Operational Security: firewalls and IDS
8: Network Security 8-238










































































 english
english








